Man-in-the-middle attack
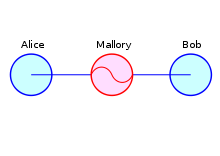
A man-in-the-middle attack ( MITM attack ) is a form of attack that is used in computer networks . The attacker is either physically or - today mostly - logically between the two communication partners, has complete control over the data traffic between two or more network participants with his system and can view and even manipulate the information at will. The attacker's Janus-headedness consists in pretending to the communication partners that he is the other person.
Examples of MITM attacks
This special position between the communication partners can be achieved, for example, in the following ways:
- The attacker is on the same LAN as the attacked:
- The attacker has physical access to the data lines.
- In the Ethernet , the attacker modifies the ARP tables of the victim systems and thereby routes all data traffic through his system. This method also enables eavesdropping on data traffic on switches , see ARP spoofing . This procedure always works when the attacker and the victim are in the same local network. This is also the case with cable network providers and z. B. given in public WLAN hotspots.
- The attacker is on the same network bus as the victim, which means that he receives all the packets anyway. However, this only works in networks with a bus structure, such as B. Ethernet with hub or 10BASE2 as well as with a token ring infrastructure.
- Another attack method of this type is playing a fake DHCP server. By specifying an incorrect standard gateway address to the Internet, communication can be routed through a computer belonging to the attacker.
- For WLAN-related attacks only:
- With public WiFi hotspots, it is possible to fake a fake WiFi access point by snarfing . In this case, too, the wrong access point forwards the data - after evaluation and possibly manipulation - to the correct access point.
- Other MITM attacks:
- The attacker has control over a router through which the data traffic is channeled. This works in the WAN as well as in the LAN and in the WLAN.
- With DNS cache poisoning , the attacker specifies an incorrect target address for Internet communication and thereby routes the traffic through his own computer (poison routing).
- By manipulating the hosts file on the computer of the attacked person, fake IP addresses can be resolved despite entering the real URL . If the attacker then simulates a valid web server, he has a good chance of remaining undetected as a MITM. See also: Pharming
Well-known computer programs for MITM attacks are Ettercap and Cain & Abel .
Countermeasures
Protection against reading
This type of attack can be counteracted most effectively by encrypting the data packets, although keys must be verified using a reliable medium. This means that mutual authentication must take place; the two communication partners must have exchanged their digital certificates or a common key in another way , d. In other words, they either have to know each other or use a certification authority. Otherwise z. For example, if an attacker is using an encrypted connection, they can fake the wrong key for both victims and thus also read the data traffic. The principle of this form of secrecy always corresponds to the HBCI standard.
Notes on individual protocols that use encryption:
- SSH (Secure Shell) offers the possibility of using a fingerprint to check whether you have actually reached the target computer after you have logged on for the first time.
- TLS (Transport Layer Security) : The u. a. TLS used with HTTPS is based on certificates; a key pair (public and private) plus descriptive information. This certificate is i. d. R. by a trusted certificate authority signed after it has verified the identity of the applicant. It should be noted, however, that TLS can only encrypt the transmission and secure the authenticity of the parties involved. Targeted manipulations during data processing in the systems of the individual parties themselves, e.g. B. by malware , can neither be detected nor excluded. Another weak point: If the certification body cooperates with the eavesdropper, e.g. B. on official orders or because of a compromise , the man-in-the-middle can set up a TLS proxy and listen in unnoticed; of course, he can then also fake content. If the certificate is checked manually (e.g. by comparing the fingerprint), this option is ruled out.
In October 2014, the Poodle security vulnerability became known, which exists through a man-in-the-middle attack in SSL 3.0 as well as TLS 1.0 and 1.1.
Protection against manipulation
In addition to encryption, there are other techniques that do not protect against being read, but prevent or make visible changes to the data due to MITM attacks. This includes:
- The so-called integrity protection , as used in the UMTS radio access network . Each transmitted message receives an identity stamp, the Message Authentication Code (MAC), which is generated using a code previously negotiated between the network and the user. Only if the MAC received with the message corresponds to the MAC expected by the recipient is the message recognized as valid by the recipient system and processed further.
- Your own monitoring of the physical address helps against an attack using ARP spoofing (see above), as the target address is changed in the event of such an attack (visible in the console (arp -a)). The physical address can also be entered manually into the console to prevent an MITM attack.
Secured by a second channel
The same can be achieved with the Mobile TAN (mTAN). With this method, the user is sent a TAN via SMS via a second channel, the mobile phone, which can only be used for the transaction that has just been entered (e.g. bank transfer). Usually, in addition to the TAN, recipient data is also communicated, so that the user on the PC also receives information via the second channel about which transaction he is currently confirming. This can prevent improper disposal. However, users of the PIN / TAN system should be aware that the common "Trojans" first spy out the access ID and PIN and thus the confidential account data for those in the middle or any other unauthorized account access, thus compromising the account becomes. Under certain circumstances, if the customer is allowed access to his stored telephone number via the online banking portal, this may mean that this available information is skimmed off in order to manipulate the mobile phone as well. Smartphones or other phones with internet access are particularly affected. The seemingly harmless offer to update the telephone software actually hides a component which forwards the mTAN received from the bank to a specified third-party connection without the knowledge of the authorized person. This in turn gives the ultimate recipient the opportunity to use the account like an authorized person.
With the eTAN , or TAN generator , presented in December 2006 , the recipient data (recipient IBAN or recipient account number) is entered. Taking into account the time or other defined data, a TAN is generated (generated) and displayed on the device. This TAN must now be entered again using the keyboard. Through this process, the TAN is linked to the recipient account and is only valid for a few minutes. The user himself cannot determine any change or manipulation of the information during transmission. However, the bank has the option of checking the validity of the TAN in connection with the recipient information entered on the device and the time of transmission.
Another possibility for preventing man-in-the-middle attacks is two-factor authentication, for example according to the U2F standard of the FIDO alliance . A security token is required for authentication , which cannot be simulated by an attacker, but must be physically available.
See also
Individual evidence
- ↑ A detailed description of SSH can be found under SSH Host Key Protection
Web links
- Tina Grüner: What exactly is a man-in-the-middle attack?
- Attacking Tor: how the NSA targets users' online anonymity - Description of a real man-in-the-middle attack