Keylogger

A Keylogger (dt. "Key logger" ) is a hardware or software that is used to control the input from the user at the keyboard of a computer to monitor and thus monitor or reconstruct. Keyloggers are used, for example, by crackers , news services or investigative authorities to gain access to confidential data - such as passwords or PINs . A keylogger can either record all entries or target keywords such as B. Access Codeswait and then record to save storage space.
Software keylogger
Software keyloggers switch between the operating system and keyboard , read the keystrokes and pass them on to the operating system. Some keyloggers save the entries on the hard drive of the monitored computer, others send them to another computer via the Internet .
One example is the inputlog software from the University of Antwerp , which is used to scientifically study the writing process.
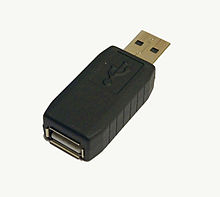
Hardware keylogger

Hardware keyloggers require immediate physical access to the affected computer. They are used in situations in which the installation of software keyloggers is not possible, does not make sense or is too costly. Hardware keyloggers are plugged directly between the keyboard and the computer and can therefore be attached within seconds. Devices that store the spied out data in an integrated memory ( RAM , EPROM, etc.) are then removed again later. The entries recorded by them are then read out on another computer. Other technologies send the logged data over networks or by radio. The easiest way to identify hardware keyloggers is to examine the hardware used (primarily the keyboard and connecting cables between the keyboard and computer). However, for many of the available models there is also the possibility of recognizing them using software.
Law (Germany)
In Germany, the unauthorized (without consent) use of keyloggers on third-party computers as spying on data is punishable under Section 202a of the Criminal Code. Companies that want to use keyloggers on company computers must first obtain the consent of the works council. In addition, according to section 22 of the annex to the VDU Regulation, “no device for qualitative or quantitative control may be used without the knowledge of the user [...]” .
Protection against keyloggers
You can protect yourself from hardware keyloggers with a virtual keyboard . The keylogger does not record the entries on this screen keyboard. It is therefore advisable to use this to protect yourself from hardware keyloggers. However, this does not offer any protection against software keyloggers.
To protect against software keyloggers, you should keep your system up to date with anti- spyware programs or the latest virus scanners . On other computers you can protect yourself against keyboard loggers by deliberately "dicing" the keyboard entries. B. registers on a website, remove the focus of the cursor between the individual character entries of the password by clicking on a free space on the website, type in the contaminating letters and continue typing on the password. Limits and a more detailed description of the method can be found in How To Login From an Internet Cafe Without Worrying About Keyloggers (web links).
See also
- Keylogger affair at the taz
Web links
- Learning More About the Underground Economy: Case study by the University of Mannheim on keyloggers, data collection points and the values of the stolen data (PDF file; 1.3 MB).
- Alexander Schultz: New criminal offenses and problems - The draft of the StrafÄndG to combat computer crime of September 20, 2006 Website accessed on October 21, 2014
- How To Login From an Internet Cafe Without Worrying About Keyloggers (PDF; 66 kB)
- Article "Keylogger" on pcwelt.de (from March 20, 2008)
- Lecture on detection of hardware keyloggers using software (PDF; 1.2 MB)
- The use of keyloggers without cause is not permitted. The Federal Labor Court of the FRG ruled on July 27, 2017 that the use of a software keylogger in the workplace is only possible under strict conditions. Privacy News , 2017.
Individual evidence
- ↑ input log. A research tool for logging and analyzing writing processes. University of Antwerp, accessed on February 18, 2016 .
- ↑ see HITB lecture (PDF; 1.2 MB)