Symmetrical cryptosystem
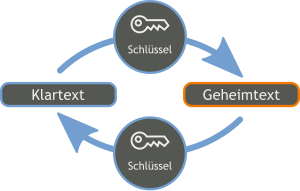
A symmetric cryptosystem is a cryptosystem in which, in contrast to an asymmetric cryptosystem, both participants use the same key . With some symmetrical procedures (e.g. IDEA ) the two keys are not identical, but can easily be calculated apart. This article is limited to the presentation of encryption methods . Sometimes Message Authentication Codes are also referred to as a symmetric cryptosystem.
Formally, a symmetric encryption method is a tuple , where the amount of possible plaintexts, the amount of possible ciphers and the amount of allowed keys. is the encryption function and the decryption function. The procedure must be correct, in the sense that for all true .
The symmetrical methods are divided into block ciphers -based methods and stream ciphers . With stream ciphers, the plain text is encrypted character by character in order to obtain the ciphertext , or decrypted in order to obtain the plain text. A block cipher works with a fixed block size and encrypts or decrypts several characters in one step. In order to be able to encrypt texts of any length, operating modes have been defined that determine how the block cipher is used.
The major disadvantage of symmetrical methods is the use of one and the same key for encryption and decryption, i.e. H. In addition to the encrypted information, the key must also be transmitted. The problem with using symmetrical procedures is that the key must be transmitted over a secure channel, because the security of the procedure depends on the confidentiality of the key. In the past, the key was typically delivered personally by a messenger. Since the 1970s, asymmetrical key exchange protocols with Diffie-Hellman key exchange have been known, with which keys can also be transmitted securely over a tapped channel. Another possibility is the use of asymmetric encryption methods to encrypt the symmetric key itself and to be able to transmit it in a protected manner via an insecure channel. During communication, this hybrid encryption can take advantage of the advantages (for example, the higher speed) of symmetric encryption, while the key is protected against access by an attacker by asymmetric encryption.
Symmetrical processes have been around since ancient times . Until the 1970s, only symmetrical methods were known.
Procedure
- AES ( Advanced Encryption Standard ) or Rijndael: the American encryption standard, successor to DES; Block encryption method developed by Joan Daemen and Vincent Rijmen
- DES ( Data Encryption Standard ) or Lucifer : until October 2000 the encryption standard of the USA. Lucifer, the process, was developed by IBM in 1974 . The version for private users is called the Data Encryption Algorithm (DEA).
- Triple DES : a further development of the DES process; three times slower, but orders of magnitude safer
- IDEA ( International Data Encryption Algorithm ): a block encryption process developed at ETH Zurich in 1990 ; Software patented by Ascom Systec ; Application in PGP
- Blowfish : Block encryption method developed by Bruce Schneier in 1993 , unpatented
- QUISCI ( Quick Stream Cipher ): very fast stream encryption method developed by Stefan Müller in 2001, unpatented
- Twofish : block encryption method, by the Counterpane team ; we you. a. used in Microsoft Windows .
- CAST-128 , CAST-256 : Block encryption method by Carlisle M. Adams , unpatented
- RC2 , RC4 , RC5 , RC6 (“Rivest Cipher”): several encryption methods from Ronald L. Rivest
- Serpent : Block encryption method by Ross Anderson , Eli Biham and Lars Knudsen , unpatented
- One-Time-Pad : unbreakable one-time key procedure by Gilbert Vernam and Joseph Mauborgne
Web links
- CAST algorithms (English)