Secondary radar


A secondary radar is a radar that works with active targets and therefore can operate with less power. In contrast to primary radar , in which only a (passive) reflection takes place at the target, in secondary radar an interrogator sends a data signal that is actively responded to by the transponder with a "response". This answer can contain additional information such as the flight altitude or friend-foe recognition .
Secondary radar devices are mainly used in aviation , but other areas of application have been opened up over time. They are used for airspace surveillance primarily in the transport sector . The principle of secondary radar is often used to determine the distance from space probes, also according to this principle, but RFID works over very short distances .
development
The secondary radar method developed from a military system whose original task was to differentiate between friend and foe on the radar screen . During the Second World War there was an urgent need for the British air defense to be able to differentiate between its own and enemy target signs on the radar screen. Therefore, Frederic Calland Williams and Bertram Vivian Bowden , who was later ennobled for his services, developed a system that later became known as the Identification Friend Foe (IFF) .
The first systems (IFF Mark I and Mark II) only received the transmission pulse of the radar device and transmitted it again amplified. The transponder was only switched on when requested. No technical enhancements were necessary in the radar device: the own aircraft was displayed twice on the radar screen. (A consequence of the internal signal transit time in the transponder.) It was only from the IFF Mark III system onwards that the response was sent on its own frequency band , at that time on 157 to 187 MHz. From this point on, a special receiver was necessary in the radar device.
From 1943 onwards, the IFF Mark V was developed as a joint British-American project in the United States Naval Research Laboratory under the leadership of Doctor Bowden, who had moved to Washington, and adapted for series production under the name United Nations Beacon (UNB) . This IFF system already worked in the frequency band 950 to 1150 MHz, i.e. the same frequency band as the modern IFF / SIF. A further development of this principle has been acclaimed as Mark X designates. The letter X was initially used as a symbol for an unknown version number. This system was still very simply structured and worked on 12 different channels with a frequency spacing of 17 MHz. This Mark X (IFF) could not yet transmit an individual identification of an aircraft.
Only the further development to the Mark X (SIF) system, with the now assigned meaning for the character X as a Roman number ten and the abbreviation SIF for Selective Identification Feature , made individual identification possible with a pulse-coded response. On this basic version, the international standard Mark X was formulated by the International Civil Aviation Organization ( ICAO ) in 1953 and, with many extensions, defined as the basis for the civil use of secondary radar in air traffic control , while the purely military use of the Mark X standard became less and less important.
During the same period, a secondary radar was also developed as an identification device in the former Soviet Union . Here, under the system name Kremni, a three- and sometimes four-digit pulse pattern was transmitted on a frequency in the UHF range, which was received by the transponder, if a valid coding was present (only three pulses are a valid query, the fourth pulse is for deception) modulated at a low frequency and re-transmitted. This low frequency represented the identifier and was implemented using twelve plug-in code filters. These different filters were changed in the Warsaw Pact armed forces according to a centrally prescribed, secret, pseudo-random scheme at intervals of two to six hours. From Russia's Pacific coast to Europe to Cuba , these code filters were changed simultaneously regardless of the local time zone . Civilian use was not actually intended, but since civil aviation was organized by the state and all civil aircraft were to be used as military transporters in the event of mobilization , all civil aircraft were also equipped with this transponder.
The military application of the secondary radar method is still an essential task today, but the scope of the IFF / SIF code is far too small for a counterfeit-proof friend / foe identification. For this reason, the data transmission process, known as IFF Mode 4 and Mode 5 and encrypted with crypto computers, was later integrated into the SIF for purely military applications.
The names of the mark systems come from the world of military terms. They combine several identification modes in one name and were described in the Standardization NATO Agreement 4193 (STANAG 4193 Part I - VI).
- Mark X or MkX (pronounced "mark ten") includes modes 1, 2, 3 / A;
- Mark XA or MkXA includes modes 1, 2, 3 / A, C;
- Mark XII or MkXII includes modes 1, 2, 3 / A, C, 4;
- Mark XII-A or MkXII-A includes modes 1, 2, 3 / A, C, 4, 5;
- Mark XII-A / S or MkXII-AS includes modes 1, 2, 3 / A, C, 4, 5, S
In older literature, the terms Super Beacon and Discrete Address Beacon System (DABS) are still used as former names for the Mode S method.
functionality
The secondary radar principle is a location method with time-of-flight measurement that, in contrast to conventional radar technology, does not work with the energy reflected at the target, i.e. the passive echo of a target, but with an active response device ( transponder ) on board the target . With secondary radar, the targets actively respond to a received radar signal by sending out a response on the same or a different frequency . In the system used in civil aviation, the query is transmitted on the frequency 1030 MHz and the answer on the frequency 1090 MHz.
For this purpose, the radar pulse is received with an antenna and triggers the transmission of a characteristic "echo" via the same antenna. This response can be a characteristic modulation or a data packet. In the simplest case, this is the delayed radar pulse itself, with the first systems for friend-foe identification a double point was written on the radar screen - one point from the passive reflection signal and another from the (delayed) secondary radar.
Both systems have different advantages and disadvantages due to the different principles. The main advantage of secondary radar compared to primary radar is its significantly greater range and the ability to identify the target. With the primary radar, reliable information about the direction, height and distance of the targets is obtained completely independently of the target. A secondary radar provides additional information such as identification, identification and also the height of the targets. However, this requires the cooperation of the target. If this cooperation is missing, for example because the transponder is defective, the secondary radar cannot work and this flight object is not recognized. That is why most secondary radars work in combination with a primary radar.
Block diagram
The procedure consists of two devices: the query device (interrogator) and the response device (the transponder ). In aviation, the interrogators are partly ground stations, partly (especially in fighter aircraft ) an interrogator can be scaffolded like the transponder in an aircraft.
Depending on the type of modulation (the so-called mode ), the interrogator sends a query encoded with different pulses, for example. These impulses are received and evaluated by the transponder. Depending on the content of the query, a response is generated, encrypted again and sent out.
By measuring the runtime between the transmission pulses and the response telegram, the distance between the interrogation device and the response device can be calculated. Because of the delays caused by decoding and coding in the transponder, this distance calculation is only correct if this additional delay time is known.
Range calculation
By actively cooperating with the target, a drastic reduction in the necessary transmission power can be achieved with the same range, since with primary radar the free space attenuation is included in the radar equation with the outward and return path , with secondary radar only with the outward path, since the return path counts as an independent radio link. In contrast to primary radar, in which the range is determined by the fourth root in the radar equation, the range of secondary radar is calculated using a function with a square root. A factor of around 1000 can be assumed here as a guide. The result is a much simpler, smaller and, above all, cheaper transmitter. The transmission pulse power of a secondary radar, which is usual in practice, is between 250 and a maximum of 2000 watts. The transmission power of the transponders is of the same order of magnitude.
At the same time, the receiver can be less sensitive, since the performance of the active responses is higher than that of the passive echoes. With a primary radar, the receiver sensitivity with good radar receivers reaches values of −110 dBm … −120 dBm. With a secondary radar, values around P e = −65 dBm are optimal in order to be sufficiently sensitive and at the same time sufficiently immune to interference. The range is calculated according to the formula:
R = range
P s = transmission power
P e = reception power
G s = gain of the transmitting antenna
G e = gain of the receiving antenna
λ = wavelength (here about 29 cm)
calculated.
Since the transmitting and receiving antennas (and thus the antenna gains to be used in the formula) are the same on both the query path and the response path in secondary radar as in primary radar, the only difference here is due to the different wavelengths at 1030 MHz (query path) and 1090 MHz (response path) given. The transponder can work with a slightly lower transmission power due to the slightly higher transmission frequency, since both antennas have a more effective effective area for the response frequency .
Above all, the necessary transmission power of the interrogation device is to be calculated from the range formula. The transponders must always respond with full power (just under 2 kW), since the transponder does not know the distance from the interrogator. The range up to which the IFF / SIF information can be displayed is only known in the interrogator. Therefore, the range formula can be changed according to the transmission power of the interrogator:
The square term here is the free space attenuation at a constant wavelength as a function of distance. The losses L can result in internal losses from the antenna to the plot extractor (a total of around −3.5 dB) and external losses due to the diagram form (see -3 dB limits) of the antenna, due to interference in the presence of reflections (average of −4 dB) or the influence of a radome (about −0.2 dB). Under very unfavorable conditions, the internal and external losses can total up to −9 dB.
| Receiver sensitivity | - 65 dBm |
|---|---|
| Free space attenuation for 278 km (rounded) | + 140 dB |
| Antenna gains | - (+ 27 dB) |
| Losses (rounded up) | + 9 dB |
| = necessary transmission power | 57 dBm |
Taking into account the antenna gains and losses, attenuation of 122 dB can be assumed from the transmitter to the receiver for a range of 150 nautical miles (= 278 km). The receiver sensitivity of the transponder is at least −65 dBm. The transmitter must therefore have a pulse power of
raise. A transmission power greater than 500 watts for the maximum representable distance of 150 nautical miles no longer has any effect on the range and only increases the mutual interference from Fruit . The transmitters of the secondary radar devices in air traffic control are usually designed for a pulse power of 2000 watts, but the transmission power can be reduced in -3 dB steps. If, for example, the primary radar only has a limited range, then increasing the transmission power of the secondary radar is counterproductive.
Business organization
The secondary radar method is used in civil and military aviation with mutually compatible systems:
- civil: “SIF” for Selective Identification Feature and “SSR” for Secondary Surveillance Radar
- military: "IFF" for Identification Friend or Foe - friend-foe recognition
In aviation, secondary radar offers additional information about an aircraft that primary radar cannot determine or cannot determine in terms of quality. It is a cooperative process, which means:
- The aircraft must be in the process cooperate and
- the individual steps of the process must be standardized so that the aircraft and the ground station understand each other.
Standard Mark X
The ICAO defines binding standards that regulate the secondary radar procedure. One such standard is known as Mark X ( read: Mark ten ). The classic fashion and code are defined in this standard. The aim of this query is to identify the aircraft and query the additional information about flight altitude .
Query format
The query is often referred to as mode. The question is something like: “Who are you?” The transponder on the plane responds with a transponder code . Alternatively, the question can also be asked “How high are you flying?” (This question arose from the fact that most radars used to be only 2D radars .) The aircraft answers this with another code. Fashion and code always belong together, because if the question is not known, the numerical value answered is not clear. The mode is transmitted coded by the distance between two short transmission pulses and has the following meanings:
| Fashion | Distance between P1-P3 |
use | |
|---|---|---|---|
| military | civil | ||
| 1 |
 3 (± 0.2) µs |
Military identification
This mode only supports 32 different codes (although 4096 codes are also technically possible). Normally, these codes convey information about the purpose, task and type. Hardly used in peacetime. |
|
| 2 |
 5 (± 0.2) µs |
Military identification
Mode 2 contains 4096 different codes for military purposes (like Mode A). Normally, these codes are used to transmit an individual code for the aircraft (military identifier). |
|
| 3 | A. |
 8 (± 0.2) µs |
Civil and military identification
The answer to mode A (code) is a four-digit number (octal 0000 to 7777; three bits or pulses per digit BCD-coded ) to identify the aircraft. It is entered by the pilot directly on the transponder or on the remote control unit. (Was once intended as an individual code, but is no longer sufficient for this task today.) |
| B. |
 17 (± 0.2) µs |
not used | |
| C. |
 21 (± 0.2) µs |
Barometric altitude
Height of the aircraft in steps of 30.5 m (100 ft ). This value is determined by a barometric altimeter, which has the same standard setting in all aircraft in the world (ICAO Standard Atmosphere). The value is technically transmitted in a similar way to mode 3 / A, but not coded directly in octal form, but using a Gillham code . The range of values covers data from −304.8 m (−1000 ft) to 38.7 km (127,000 ft). |
|
| D. |
 25 (± 0.2) µs |
not used | |
A P2 pulse is also integrated in each of the inquiries that are generally sent on 1030 MHz with this method. This serves to suppress sidelobes and ensures that only transponders from the main direction respond to the query.
Response telegram
The response telegram is 20.3 µs long for all modes mentioned so far and is transmitted on the frequency 1090 MHz. With this answer, a larger tolerance range must be accepted, because, for example, at high altitudes and in very cold weather, the frequency-determining components of the transponder have greater deviations from the target value.
The response telegram consists of 2 to 15 pulses with a pulse duration of 0.45 µs (± 0.1 µs) each. The two frame pulses F1 and F2 at least 20.3 µs apart must be present so that the receiver recognizes these pulses as a valid response. Between the frame pulses there are a total of 13 positions for the coding pulses at a distance of 1.45 µs. Of these, only a maximum of 12 are used in modes A and C for the transmission of the desired information in an octal code. The three spaces must not be occupied by pulses, as otherwise some decoders interpret the entire response as a disturbance and thus discard it. However, the response telegram does not contain any information about the mode. The decoder of the secondary radar always assumes that the response received matches the last mode queried.
The pulses between the frame pulses contain the code which, depending on the query mode, contains the desired information as an octal number. Due to the number of 12 possible pulses, the range of values for the unique information is limited to 4096 10 .
With the “squawk ident”, the SPI pulse (special position identification pulse) is placed 4.35 µs (three grid intervals) after the frame pulse F2 after the pilot manually presses the “IDENT” button in the control panel of the transponder. This causes z. B. on DERD radar screens, the head icon of the SSR target.
The nesting of the impulses and the space in the middle are included for historical reasons. The forerunner of this procedure only had the option of transmitting two octal numbers. For reasons of compatibility, the additional octal numbers were later placed in the spaces of the old answer.
display

In the simplest case, another, usually somewhat thinner, target is displayed on the radar screen behind the target of the primary radar device. The distance initially corresponded to the additional delay time in the transponder. Later it could be set individually on the viewing device. The numerical values of the identification code and the altitude information must be read on an additional display made of light-emitting diodes on the secondary radar or on a remote display next to the primary radar screen. Some radars can display this additional information on the screen as a number.
Modern digital radar devices can combine the information from the secondary radar with the target of the primary radar device. Both radar information is processed into a digital data word in a plot extractor each , which is then correlated to a data set in the radar data processor . The display is therefore on the digital screen of the primary radar device. Since the signal delay times also differ considerably in the ground station, the antenna of the secondary radar device must be mounted on the primary radar antenna with a small angular offset.
Standard Mark XII (Mode S)
Another binding standard defined by the ICAO (Mark XII - pronounced: Mark twelve ) is also referred to as Mode S (Mode Selective). This new standardization became necessary because the previous systems had reached their capacity limits due to the increased air traffic. Reasons were: Exceeding the maximum number of processable targets, false radar echoes (e.g. FRUIT generated by ACAS queries ), limited azimuth resolution . In several cases this led to aircraft being displayed incorrectly or not at all on the radar screen ("lost targets"). Another point was that the range of values for mode 3 / A (with only 4096 different codes) was too small.
In mode S, each transponder has a permanently programmed, individual address. The standard stipulates that not all transponders respond to a query, but only those that are expressly addressed via their address. This massively reduces the number of response signals. In addition, the response signal also contains the address information so that it can be clearly assigned to the respective aircraft and FRUIT is excluded. This standard was established by the ICAO and is required for new aircraft certifications.
"The individual SSR Mode S address should be one of 16,777,214 possible 24-bit addresses that are assigned by the ICAO or a state or other authorized general registration authority."

Below: CSA aircraft with additional Mode S information
The previous identification system in mode 3 / A only had a range of 4,096 different identification codes due to the four-digit octal code used . Therefore, this code had to be assigned dynamically, that is, when flying through different areas of responsibility, the aircraft was assigned a new identification code. So far this has caused the risk of mix-ups on the radar screen .
The Mode-S system can be defined as the basic protocol for communication between the transponder in the aircraft and the secondary radar on the ground. In addition to the identification code , which is now assigned individually (similar to a vehicle license plate ) for an aircraft, a great deal more information about the current flight status can be transmitted to the secondary radar. Military mode 4 cannot be evaluated by civilian devices because the answers are coded and the content is therefore classified (classified / secret).
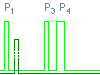
A major advantage of the system is that the ground stations can exchange the requested information via a network. This reduces the frequency of queries and thus also the mutual interference caused by Fruit . However, this presupposes that if the selective query of an aircraft has been made, its answer is assigned to a primary echo and no further query is made. The query must be backwards compatible again . An old Mark-X transponder must not be confused by the Mode-S queries. Therefore, these old transponders are queried as before, but a fourth pulse (P4) is added to the protocol, which blocks a Mode S transponder for these queries. The old transponders do not know this impulse and ignore it.
The query options of a mode-S-capable ground station are roughly classified into two types:
All-call interrogations
- "All-call interrogations" expect an answer from all aircraft in the area of view. However, under certain conditions the Mode-S transponder can block these responses. For example, a successful interrogation can have the effect that the ground station that triggered this interrogation no longer receives any responses to this interrogation mode. The transponder now expects a "roll-call interrogation" from this ground station.
Roll-call interrogations
- "Roll-call interrogations" are individually (selectively) addressed queries to which only the one addressed Mode S transponder reacts. The answer to this selective query is a telegram of up to 112 bits, which can contain various information such as course, speed or avoidance recommendations from the on-board collision warning system (see TCAS ). The exact content can be selected by the air traffic controller from a pool of possibilities.
Transmission protocols
Uplink
In addition to the actual Mode-S interrogation, the ground stations must also transmit pulse patterns compatible with the Mark-X system, which are shown in the following table:
| Pulse duration from P4 | Mode S inter mode | |
|---|---|---|
 no P4 |
Mode A reply | This query is sent in a downwardly compatible manner for transponders that are not mode S capable. Since the transponder cannot recognize whether a mode S-capable ground station is polling, it also answers. |
 0.8 µs |
no reply | Therefore a short P4-impulse is sent by mode S-capable interrogation stations, then a mode-S-transponder does not answer. Old transponders do not know this impulse and respond. |
 1.6 µs |
all-call reply | A long P4 pulse is sent to trigger an "all-call interrogation". This mode is seldom used because there are other and better ways of capturing the individual code and triggering a specific Mode-S query. |
 no P4 but large P2 |
Mode S reply | The radar sends a P2 pulse with the same amplitude as the P1 pulse. This activates mode S transponders to receive the P6 pulse with the data block. For transponders not capable of Mode-S, this query appears as if from a side lobe and is therefore not answered because the ISLS condition is met. |
A pulse modulation with differential phase shift keying (DPSK) is used as the transmission protocol on the so-called uplink path (query from the ground station up to the aircraft) within the P6 pulse . Since the P2 pulse is now used to block the old transponder, the sidelobe suppression has to be solved differently. A fifth pulse P5 is transmitted via an antenna with omnidirectional characteristics, like the P2 pulse before. This pulse covers the synchronous bit in the P6 pulse. If the P5 pulse is too large, the transponder cannot decode the P6 pulse. The P6 pulse can contain either 56 or 112 bits.
Technically it is also possible to send information to aircraft via the uplink, for example weather data, information about approaching aircraft (TIS, traffic information service, in the USA), flight clearances, etc. These possibilities are not yet used in the EU. A total of 25 different queries are possible with Mark-XII; there are also 25 individual answer options.
Downlink
On the downlink path (response from the aircraft to the interrogator), it is unfavorable to also use differential phase shift keying (DPSK). The transmission security is adversely affected by the extreme temperature fluctuations to which a transponder is exposed at high altitudes. Therefore a less sensitive modulation, Pulse Position Modulation ( PPM ) is used. Whenever a falling edge is detected in a synchronous pulse stored as a time pattern in the response diagram, then a logical "1" is present. A logical "0" is recognized with a rising edge. Either 56 or 112 bits are transmitted on the reply path.
Squitter mode
A special feature of the Mode-S-enabled transponders is the so-called squitter mode , in which the transponder transmits GPS position and identification as a broadcast independently of a query and at regular intervals (ADS-B Automatic Dependent Surveillance - Broadcast ). However, support for this mode is not mandatory in Germany. Also, not all Mode-S-capable transponders are technically capable of sending such a message.
This mode makes it possible to set up a virtual radar with a simple receiver connected to a computer via a USB interface on the frequency of 1090 MHz, which can display commercial flights within a radius of around 40 km on the computer display in real time with a small rod antenna . By linking many such small receiving stations via a network , seamless displays of the movements in the airspace are possible.
Equipment regulations
A transponder is mandatory in Germany:
- For IFR flights (§ 3 FSAV )
- For VFR flights in airspaces C and D (not control zone) (§ 4 FSAV)
- For VFR flights in airspace with prescribed transponder switching ( Transponder Mandatory Zone - TMZ) (§ 4 FSAV)
- For VFR flights at night in uncontrolled and controlled airspace (§ 4 FSAV)
- For VFR flights with motor-powered aircraft above 5000 ft above sea level or above an altitude of 3500 ft above ground (§ 4 FSAV)
Other uses
In addition to aviation, which is certainly the largest user of radar technology, radar systems (both primary and secondary) are also used in non-aviation areas. In addition to many other transponder applications , only those are referred to as secondary radar in which a distance determination is carried out by means of a transit time measurement.
In shipping, a radar beacon works on a similar principle, with the transponder attached to the navigation mark.
Secondary radar in automotive engineering
Modern automobiles use secondary radar to determine the approach of a radio key to the vehicle. In addition to measuring the transit time of the signal, data is also transmitted that identifies the key to the vehicle. The door locking system is only unlocked after successful identification and when the key is not far from the vehicle. An additional interior-exterior detection ensures that the drive can only be started when the key is inside the vehicle. Removing the vehicle from the vehicle does not result in the doors being locked again; this must be triggered (controlled) manually.
literature
- Michael Stevens: Secondary Surveillance Radar (Artech House Radar Library) . Artech House Publishers, ISBN 0-89006-292-7
- Peter Honold: Secondary radar, fundamentals and device technology . Siemens, Berlin / Munich 1971
- Eurocontrol: ICAO Annex 10 Volume IV (Surveillance Radar and Collision Avoidance Systems) . Issue 77
- Ordinance on air traffic control equipment for aircraft (FSAV). November 26, 2004 ( BGBl. I p. 3093)
Web links
- dfs.de (PDF) Detailed summary of the equipment regulations
- radartutorial.eu (virtual course "Radar Basics", section SSR and MSSR)
- lba.de Federal Aviation Office
- eurocontrol.int ( Memento from June 10, 2007 in the Internet Archive ) Mode-S-FAQ from Eurocontrol
Individual evidence
- ↑ Philipp Hartl: Telecontrol technology in space travel: telemetry, telecommand, orbit measurement . Springer-Verlag, March 8, 2013, ISBN 978-3-642-83364-9 , p. 14.
- ↑ Michael Stevens: Secondary Surveillance Radar . ISBN 0-89006-292-7 , p. 218
- ↑ a b ICAO - Standard Annex 10 Volume III Chapter 9, Supplements 71 ff.
- ↑ SBS-1 Real-Time Virtual Radar Receiver for Aircraft Transponder Signals, THIECOM ( Memento of the original from May 16, 2007 in the Internet Archive ) Info: The archive link was automatically inserted and not yet checked. Please check the original and archive link according to the instructions and then remove this notice.









