Cloud computing
Cloud computing (German computer cloud or data cloud ) is an IT infrastructure that is made available via the Internet, for example. It usually includes storage space , computing power or application software as a service .
In more technical terms, cloud computing describes the approach of making IT infrastructures available via a computer network without these having to be installed on the local computer.
These services are offered and used exclusively through technical interfaces and protocols , such as a web browser . The range of services offered as part of cloud computing covers the entire spectrum of information technology and includes infrastructure, platforms and software , but also storage space and databases.
Definition
In 2011 the National Institute of Standards and Technology (NIST) published a definition that met with widespread acceptance and bundles different definition approaches:
Service models
Cloud computing contains four different service models:
Software as a Service (SaaS)
- Clouds provide access to use software collections and application programs. SaaS service providers offer special selections of software that run on their infrastructure. SaaS is also known as software on demand .
Platform as a Service (PaaS)
- Clouds offer access to programming or runtime environments with flexible, dynamically adaptable computing and data capacities. With PaaS, users develop their own software applications or have them run here within a software environment that is provided and maintained by the service provider.
Infrastructure as a Service (IaaS)
- Clouds provide access to use virtualized computer hardware resources such as computers, networks and storage. With IaaS, users are free to design their own virtual computer clusters and are therefore responsible for the selection, installation, operation and functioning of their software .
Function as a Service (FaaS)
Clouds provide user access to functional content. FaaS providers make frequently used functions available in a simple manner. This means that popular functions or functions with high computing power can be outsourced.
Delivery models
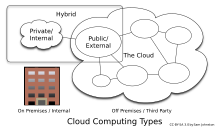
In addition, the definition of the National Institute for Standards and Technology (NIST) contains four delivery models:
Public Cloud - the public computer cloud
Provides access to abstract IT infrastructures for the general public via the Internet. Public cloud service providers rent out IT infrastructure to their customers. Payment is based on actual usage (pay-as-you-go), without having to invest capital in the computer and data center infrastructure.
Private cloud - the private computer cloud
A private cloud is a cloud environment that is operated exclusively for an organization or a company. The cloud platform can be hosted and managed internally (for example by the company's own data centers), but also by third parties. In such a case, the cloud is located in an external data center.
Hybrid cloud - the hybrid computer cloud
Offers combined access to abstracted IT infrastructures from the areas of public clouds and private clouds , according to the needs of their users.
Community Cloud - the communal computer cloud
Provides access to abstract IT infrastructures like the public cloud - but for a smaller group of users who, mostly locally, share the costs (e.g. several municipal authorities, universities, companies or companies with similar interests, research communities, cooperatives ).
There are also mixed forms of the above cloud types:
Virtual Private Cloud - a private computer cloud on an IT infrastructure that is generally accessible to the public
The isolation of the "virtual private" areas on the public infrastructure is guaranteed by suitable security measures ( VLANs ).
Multi cloud - bundling different cloud computing services
Further development of the hybrid cloud, in which several cloud computing services can be used simultaneously in a heterogeneous system architecture .
Essential characteristics
The NIST lists five essential characteristics for cloud computing:
On-demand self-service
Self-assignment of services from the cloud by the user or users who should be available when required.
Broad network access
Services from the cloud can be accessed over the network using standard mechanisms.
Resource pooling
Resources such as computing power, network or storage are shared between different projects and customers.
Rapid elasticity
Virtual resources scale quickly and from the user's point of view almost unlimitedly and can also be automatically adapted to load changes.
Measured service
Resource usage can be measured and monitored, for example for billing or automatic scaling.
As a result, cloud computing goes beyond other currently discussed approaches (e.g. virtualization ). Under the condition of public availability, similar for example to the public telephone network, cloud computing can, depending on the architecture, also be viewed as the sum of SaaS and utility computing .
history
The cloud is one of the oldest symbols of information technology and as such stands for computer networks, the inside of which is insignificant or unknown.
As early as the early 1990s, some personalities in the IT industry predicted that “computers would be distributed across the network”, that is, that cloud computing would emerge as soon as the technology was mature. The time had come with the development of the multitenant architecture in the late 1990s .
In 1995 the GMD (now Fraunhofer FIT ) introduced the BSCW, a system that is now referred to as the cloud. Web-based documents could be uploaded to folders and shared with others. BSCW has been offered commercially by the Fraunhofer spin-off OrbiTeam since 1996 .
When the social network Facebook was launched in 2004, its members were given the opportunity to save and publish (“post”) photos, videos, etc. online. However, the term cloud computing was mainly coined by some fast growing internet companies like Amazon , Google, and Yahoo . Due to the rapid growth of their user base, these companies were faced with the problem of having to maintain constantly growing systems that provide sufficient performance even at peak load times (for Amazon this would be the Christmas business, for example).
For Amazon, this peak load in 2006 was 10 times higher than the base load in day-to-day business. In order to counter this problem, it was decided to make the (service-oriented) architecture and the services that had been designed and established to cope with the sometimes strongly fluctuating or also very high user numbers into a product that was offered to the outside world , d. This means that this problem is distributed to the users of the cloud during peak load times.
For Amazon, this step was a logical consequence at the beginning of the 2000s, since at that time they had already switched internally to small, fast-moving teams (fast-moving "two-pizza teams"), which had new functionalities based on the existing cloud infrastructure implemented. The scaling effects of the cloud services thus became the basis of the cloud computing product itself, which from then on was no longer only offered internally, but also externally. Today, Amazon is the world's largest provider of cloud computing.
A mandatory requirement for the use and distribution of cloud computing services are broadband connections that are so fast that it no longer makes a difference whether data is stored locally on a PC or on remote servers in a cloud. The increasing relevance of cloud computing for private users is therefore linked to the market supply with fast, reliable and cost-effective DSL and LTE connections.
Differentiation from other techniques
" Grid computing " is about the common use of common resources and there is no central control. In the case of cloud computing, you have a resource provider and a user. The control of the resources is centralized.
Fog Computing represents the decentralized extension of cloud computing. Resources such as storage, computing power and software applications are placed closer to the end devices in order to achieve better efficiency and lower latency times through an optimized division. Only relevant and possibly compressed data are then sent to the central systems. Fog computing is closely related to edge computing , where, for example, sensor data is processed directly in the sensor system in order to then forward it to fog and cloud. There is great overlap between fog and edge computing, which is why they are sometimes used synonymously.
architecture
Since clouds were created primarily through the scaling concept, the strongest distinguishing features are also to be found there.
To get closer to the architecture, one can imagine a simple computer. It has processor cores, RAM, a hard drive and programs. These components can also be found in a cloud, only in a form that enables massive scaling.
As a result, the characteristics of a “cloud hard drive” read differently than that of a classic hard drive in the computer. Amazon says of its persistence layer (S3): “The number of objects that can be saved is unlimited.” Google has distributed its Google File System persistence layer to around 15,000 individual computers (as of 2009).
For the other components such as programs or processor cores, similarly large dimensions apply. Why this is so can only be explained by the numbers. In 2008, Google announced that it could sort 10 billion records across 1000 physical computers within 68 seconds.
"We are excited to announce we were able to sort 1 TB (stored on the Google File System as 10 billion 100-byte records in uncompressed text files) on 1,000 computers in 68 seconds."
"We are pleased to announce that we were able to sort 1 TB (stored in the Google File System in 10 billion documents, each with a data record size of 100 bytes in uncompressed text files), distributed over 1000 computers, within 68 seconds."
Technical implementation of cloud computing
There are different types of cloud computing. A possible structure is the so-called technical cloud stack with three layers, in which the upper layers can build on the lower layers, but do not have to:
- application
- platform
- Infrastructure
Each layer represents a degree of abstraction. In this way, the different types of "clouds" can also be classified.
Application (SaaS)
The application layer represents the most abstract layer on cloud services. The user does not bring his application into a cloud platform, nor does he have to worry about scalability or data storage. He uses an existing application that the cloud offers him to the outside world. This use case includes the two levels below, as the cloud functionalities such as upscaling, distributed storage, fail-safe infrastructure and usually a upscaling queuing system are the basis of the application used, but the user of the SaaS service does not come into contact with them.
A "cloud application" in the SaaS model typically takes the following aspects into account:
- The design should be modular and service-oriented (can be set up on the PaaS scenario).
- The load cannot be foreseen because it is often not possible to make reliable statements about the intensity of use and the number of users of an application.
- The application should be dynamic, distributed and multi-tenant .
Well-known examples of cloud applications are Apple iCloud , Google Drive , Microsoft OneDrive , ownCloud , Nextcloud or Salesforce.com .
Platform (PaaS)
A developer creates an application and uploads it to a cloud platform. This then takes care of the allocation to the actual processing units. In contrast to IaaS, the user has no direct access to the computing instances here. He also doesn't run any virtual servers. In the PaaS scenario, he only brings his program logic into the cloud platform, which acts as a programming interface for him .
The infrastructure of the cloud itself takes care of the necessary instantiation of the processing units and the distribution of the data to be processed.
As an example, the products Windows Azure from Microsoft, “App Engine” from Google or “force.com” from Salesforce.com can be assigned to the platform layer.
Because the user only provides his application logic here, the cloud platform can increase or reduce the number of instances actually working as desired. The abstraction of any technical component is explicitly desired here, since the user of the cloud primarily wants to process data, but does not want to administer the system.
Infrastructure (IaaS)
The infrastructure or "cloud foundation" represents the lowest layer in cloud computing. The user accesses existing services within the system, but manages his computing instances (see virtual server ) himself as far as possible. Services within the IaaS concept are typical distributed persistence (see Amazon's Simple Storage Service ) and a message service (see Message Oriented Middleware ). If the cloud services themselves are still designed to scale up, this does not necessarily apply to the programs that run on the computing instances brought in by the user.
The advantage over traditional data centers is their scalability: the computing instances can be expanded or reduced as required by additional instances, depending on the requirements. The user has full access to the instances with the property that he is responsible for the instances from the operating system level.
The biggest examples of this are Amazon Web Services and the Open Telekom Cloud .
Organizational types of clouds
In addition to the technical cloud stack, a distinction can also be made between different organizational forms of "clouds" that have their authorization depending on the application. The definitions for the terms “private”, “public” etc. were coined by the NIST , are used in the same way by the auditors (leading to the definition of the standards is the ISACA ) and have also been in ISO / IEC 17788 since 2014 available. The definitions by these committees are of high value, as the correct definitions of the models are established here in an internationally valid manner.
In summary, it can be said that the definitions refer to the possible group of users and have nothing to do with where “the cloud” is operated or what ownership structures look like. A “private cloud” is therefore to be understood as a cloud in which the resources are addressed by a predefined group of users and where management is carried out by excellent users. At the other end of the scale, the “public cloud” is to be found, for which there is no a priori any information about the possible users. Mixed forms in between are possible (e.g. "hybrid cloud"), but also relate to the group of users and not to the technical design.
The terms, as they are sometimes commonly encountered, and in the context of which "public cloud" is equated with "off premises" and "private cloud" with "on premises", are misleading and do not correspond to the basic idea of ISO / IEC standards nor those of other bodies.
Cloud Computing in Business
Cloud computing shifts the investment for application programs to the provider of the services and a fee corresponding to the actual performance. This makes it possible to replace cumbersome decision-making processes in the company of the customer.
Potential and advantages
Like virtualization , cloud computing enables cost advantages over conventional systems if, for example, payment is based on the length of time the service is used and the service is only used occasionally. Local resources (software and hardware) can be saved. A much-cited example is the implementation of e-mail systems based on cloud computing. Here, the complexity of the application increases due to measures to prevent attempts to compromise , so that smaller companies can use outsourcing. There are also advantages in the event of strongly fluctuating demand: one would have to have enough capacity for peak loads. With cloud computing, the capacity used can be adapted to requirements at short notice. According to a study by the Fraunhofer Institute for Material Flow and Logistics IML, halving costs in the area of warehouse management is feasible.
Risks and Disadvantages
One problem is securing access to application data during transfer between the local client and the remote server . Partial advances in the area of SSL / TLS encryption helped to alleviate the problem . On the other hand, risks from CPU design errors that have existed for decades or the future use of quantum computers still exist.
Another problem is the encryption of data in databases and file systems in the cloud. A third risk lies in unauthorized access from the cloud provider during processing. This requires distributed authentication and authorization.
Critics claim that the control of private user data by market-dominant providers like Google is getting out of hand. However, there are algorithms that distribute the calculations to the instances in such a way that it is not even possible for all instances to draw conclusions about the processed data. This is only possible for the executing entity, since only it knows the algorithm that merges partial results. A hitherto only experimental approach to solving the problem is homomorphic encryption . In the cloud, only encrypted data is calculated that can be decrypted in the private sector.
An alternative approach is the concept of the sealed cloud . The key management separates the encryption from the decryption, each using its own key. An orderly backup and subsequent deletion of unencrypted data takes place before an administrator has access to the memory, for example for maintenance purposes.
Another challenge is the dependency ( lock-in effect ) on the cloud provider, as the interfaces to the cloud are often manufacturer-specific. There is also the question of what happens to user data if the cloud operator or one of the many service providers involved becomes insolvent. Therefore, some providers offer data backup on their own storage media.
Regardless of technical risks, cloud computing entails legal risks that are difficult to foresee. In 2013, Adobe introduced a subscription model, which led to significantly higher sales and prices. Dolby Laboratories Inc. has been in a legal dispute over licensing costs for the cloud-based subscription model since 2018. Adobe banned tenants of the Lightroom Classic, Photoshop, Premiere, Animate and Media Director programs from using them due to a legal dispute with a licensing partner, saying, "We recently retired some older versions of Creative Cloud applications. Due to our Agreement, you no longer have a license to use it. Please note that if you continue to use the discontinued version (s) there is a risk that third parties may assert violations. "
Users are exposed to short-term changes to end-user license agreements (EULAs) by licensors without protection. Licensors as well as cloud operators can legally or physically terminate existing access authorizations at any time or request a subsequent purchase. This dependency did not exist before the introduction of cloud computing.
costs
There are various studies on the cost of cloud computing. According to a study by Dachyuk (2018), colocationing is cheaper than cloud computing from around 150 large AWS instances ( m4.2xlarge ).
Substitute solutions
Since some private users have concerns about storing their data with companies that could, for example, change their business conditions at any time, many NAS systems for home provide functions that are known from cloud storage operators. In this case, one speaks of a personal cloud , since the data storage infrastructure is operated entirely by the user himself. However, NAS solutions do not process data.
Differentiation from other forms of service
Some elements of cloud computing are related to classic online outsourcing . However, it differs from this in essential points. As a rule, in the Infrastructure as a Service provider, the IT infrastructure is used by several customers, so that capacity peaks can be more easily distributed and reserves can be shared. Cloud services can be adapted at short notice and thus differ from the classic model in which customers use the computer infrastructure “exclusively”. Furthermore, the control and administration of the services is carried out by the user himself via the web interface.
Legal issues
Legally, the relationships between cloud providers and their customers as well as the rights of affected third parties must be considered.
Data security
It must be taken into account that the legally required data protection cannot be achieved without technical data security. The data security is determined by the technology used by the provider and the applications used by the provider. In principle, an internal IT system offers greater security. However, a cloud system is not considered unsafe. The effort required to ensure the security level of an equivalent local system is much greater.
privacy
According to the judgment of the European Court of Justice , data may only reach the USA, where over 90% of the cloud computing infrastructure is located. National data protection agencies rely on the work of ENISA when they explain why cloud computing is not permitted for schools, for example, despite Safe Harbor . The data protection officers in Switzerland also warn against violating data protection law when using data centers abroad.
If personal data of third parties is stored online, German clients, for example, have to convince themselves in advance and then regularly on site that the requirements of the Federal Data Protection Act are being complied with. Because well-known cloud providers pass on data from their customers, customers face fines. Cloud operators based in the USA are subject to US law and therefore the Patriot Act . Companies based in the USA are therefore forced to deliver data to American authorities that are located on servers in foreign jurisdiction. This has been confirmed by Amazon, Microsoft and Google, for example.
Not least because of these problems in data protection and the question of the extent to which the individual actually retains the power of disposal over his data, the cloud or cloud computing as technology received the negative Big Brother Award in the category "Communication" in 2012 , the laudation was given by Rena Tangent from FoeBuD .
Performance debt
In the case of cloud-specific services, web or filespace , databases , applications and hosting services are usually made available. In the case of web hosting (possibly also for storage management ), in which data is stored on the host of the hosting provider, it is assumed that this is not a rental contract according to §§ 535 ff. BGB , but a contract for work and services according to §§ 631 ff. BGB. The hosting provider only owes the service that the customer's website is stored somewhere and that it can be accessed on the Internet. The actual service is therefore to store the information and make it available for retrieval on the Internet. For the customer, it is particularly important that the content is always available. How the hosting provider or cloud provider provides this service does not matter to the customer. This does not primarily leave storage space, but primarily a success, namely the availability on the Internet. Saving the website is only a technical requirement for the owed success.
When making applications available, a software-as-a-service (SaaS) or “ Application-Service-Providing ” (ASP) model is generally chosen. The ASP provider provides a customer with the temporary use of applications. The Federal Court of Justice has ruled that the provisions of tenancy law apply to application service providing contracts. Even if this decision was certainly significant, a considerable contractual arrangement is required, especially when it comes to the structuring of the service levels , since the tenancy regulations of §§ 535 ff. BGB alone should not be sufficient here.
The classification of hosting contracts for databases in the contract typological classification of the BGB is based on the contractually owed service. A basic distinction must be made here as to whether, as described above, filespace is made available by the provider to store the database (so-called database hosting) or an application such as an Oracle database (for temporary use) is made available. If the cloud IT provider owes services beyond the hosting service, such as B. when designing the databases, the regulations of §§ 87a to 87e UrhG may have to be taken into account.
copyright
Copyright issues must also be taken into account when copyrighted data is stored online. From a legal point of view, the upload of data represents nothing other than a reproduction in accordance with 16 UrhG, which requires the consent of the author. Only if the upload is for purely private purposes and the file is not made publicly accessible can the upload be made as a private copy in accordance with 53 UrhG. However, making files in the cloud publicly available (Section 19a UrhG) is always illegal without the consent of the author.
In addition, according to Marcel Bisges , cloud computing can undermine the current system of copyright remuneration by reducing the author's right to appropriate remuneration (for private copies). From a copyright point of view, on the other hand, according to Bisges, cloud computing is advantageous for software manufacturers because, in contrast to conventional software provision, the damage caused by illegal copies is avoided.
literature
- Christian Metzger, Juan Villar: Cloud Computing. Opportunities and risks from a technical and entrepreneurial point of view. Hanser, Munich 2011. ISBN 978-3-446-42454-8
- Alexander Bell: Mobile and Cloud Computing. Mobile and cloud computing - considering the companies Google, Amazon and SAP AG. Munich 2012, ISBN 978-87-403-0264-6 . Download Free eBook
- Wolfgang Tichy, Günther Leissler, Michael Woller: Cloud Computing . Vienna: Manz 2019. (Systematic Works series.) ISBN 978-3-214-08972-6
- Roland Frank, Gregor Schumacher, Andreas Tamm: Cloud Transformation . How the public cloud is changing businesses. Berlin: Springer 2019. ISBN 978-3-658-27324-8
Web links
- Cloud computing. In: Informatik Aktuell. February 1, 2019, accessed March 7, 2019 .
- Sebastian Minnich: The advantages and disadvantages of cloud computing. Heise Online , May 11, 2017, accessed on March 7, 2019 .
- Current term: Cloud Computing (PDF, 64 kB; 2 pages). German Bundestag , Scientific Services Number 15/10, March 12, 2010, accessed on March 7, 2019 .
- Cloud services for private users. Stiftung Warentest , April 24, 2012, accessed on March 7, 2019 .
- Cloud Computing Risk Assessment (including recommendations) (PDF, 2 MB, 125 pages, English). European Network and Information Security Agency (ENISA), March 7, 2009, accessed on March 7, 2019 .
- Cloud Computing - Guide, (PDF, 4 MB, 87 pages). Bitkom , accessed on March 7, 2019 .
- Guidelines on Security and Privacy in Public Cloud Computing (PDF, 1 MB, 80 pages, English). NIST Special Publication 800-144, accessed March 7, 2019 .
- The European Commission has proposed a comprehensive reform of the EU's 1995 data protection rules to strengthen online privacy rights and boost Europe's digital economy. , (English). hostingtecnews.com,accessed March 7, 2019.
- Cloud Computing (Podcast). cre.fm , accessed March 7, 2019 .
- Cloud computing as an instrument for efficient IT solutions (PDF; 953 kB). Retrieved March 7, 2019 .
Individual evidence
- ↑ The design element of an abstract cloud outline is often used in network diagrams to represent an initially unspecified part of the Internet.
- ↑ a b Federal Office for Information Security (BSI): What is cloud computing?
- ↑ Peter Mell, Timothy Grance: The NIST Definition of Cloud Computing. National Institute of Standards and Technology (NIST), September 2011, accessed November 3, 2016.
- ↑ Ubuntu in the cloud. In: Ubuntu.com , accessed May 15, 2015.
- ↑ Brief definition of the cloud delivery models. In: Fraunhofer.de , accessed on May 15, 2015.
- ↑ Elke Rekowski: Virtual Private Cloud: Compromise between costs and legal requirements. In: ZDNet.de . March 2, 2011, accessed June 10, 2016.
- ^ Above the Clouds: A Berkeley View of Cloud Computing. (PDF file; 570 kB) Accessed December 18, 2010 .
- ↑ The Internet Industry Is on a Cloud - Whatever That May Mean. In: Wall Street Journal . March 26, 2009. Retrieved January 29, 2012 .
- ↑ Ben Rodenhäuser: Cloud Computing - So that you don't fall out of the clouds. In: Manager Magazin. October 9, 2008, accessed March 18, 2015 .
- ^ R. Bentley, T. Horstmann, K. Sikkel, J. Trevor: Supporting Collaborative Information Sharing with the World Wide Web: The BSCW Shared Workspace System. 1995, accessed February 3, 2016 .
- ↑ Excerpts from the laudation at the awarding of the European Software Innovation Prize 1996. Archived from the original on October 8, 2015 ; Retrieved February 3, 2016 .
- ↑ The History of Cloud Computing. Salesforce.com, accessed May 15, 2015 .
- ↑ Amazon and Microsoft show Google the exhaust pipe - now the cloud boss is leaving. In: Watson . November 17, 2018, accessed November 19, 2018 .
- ↑ Information on Amazon S3 , accessed May 15, 2015.
- ^ Avinash Kumar: The Google File System. Presentation. Published April 22, 2009, accessed May 15, 2015.
- ↑ Sorting 1PB with MapReduce , Googleblog, November 21, 2008, accessed May 15, 2015.
- ^ Sam Charrington: Cloud Taxonomy: Applications, Platform, Infrastructure. ( Memento from December 21, 2008 in the Internet Archive )
- ^ Charles Arthur: Government to set up own cloud computing system. In: The Guardian . January 27, 2010.
- ↑ Michael ten Hompel (ed.), Maren-Bianca Meinhardt, Torben Lippmann: Cloud Computing for Logistics. Acceptance of the willingness to use the Logistics Mall among users and providers . Fraunhofer Verlag, Stuttgart 2011, ISBN 978-3-8396-0220-1 , p. 125.
- ^ David Smith: Google plans to make PCs history. In: The Observer. January 25, 2009.
- ↑ Data privacy protection: the grand challenge for cloud software. Cumulus4, 2012, accessed August 16, 2012 .
- ↑ Data in the cloud. Stiftung Warentest, April 25, 2012, accessed on April 25, 2012 .
- ↑ Reclaim.fm: Let's get our data back
- ^ Karl Bode: Adobe Tells Users They Can Get Sued for Using Old Versions of Photoshop. vice.com, May 14, 2019, accessed May 15, 2019 .
- ^ The true costs of hosting in the cloud , LWN, February 28, 2018.
- ↑ Cloud computing data security. Retrieved December 9, 2019 .
- ^ Cloud Computing Differences Between US And Europe. UBM, April 5, 2010, accessed August 14, 2012 .
- ↑ Processing of sensitive personal data in a cloud solution. Denmark Data Protection Agency, February 3, 2011, archived from the original on October 11, 2011 ; Retrieved October 2, 2011 .
- ↑ The trend towards the cloud - the growth market of cloud computing. Swiss television, May 14, 2011, accessed on October 2, 2011 .
- ↑ Data protection in the cloud. In: Spiegel online . Retrieved September 3, 2011 .
- ↑ German companies face trouble when using US clouds. Heise Verlag, October 1, 2011, accessed October 2, 2011 .
- ^ Arnd Böken: Patriot Act and Cloud Computing: Access to acclamation? In: iX. 1/2012, p. 110.
- ↑ Laudation for the “cloud” at the Big Brother Awards 2012
- ^ BGH, judgment of November 15, 2006 , Az. XII ZR 120/04, full text.
- ↑ Marcel Bisges: Impairment of the copyright remuneration system for private copies by cloud services. GRUR 2013, pp. 146–150.
- ↑ Marcel Bisges: Copyright Aspects of Cloud Computing. Economic advantage over conventional software provision? In: Multimedia und Recht , Issue 9, 2012, pp. 574–578.