The (also the) e-mail ( English [ ˈiːmeɪl ], short mail ; English electronic mail for "electronic mail") is on the one hand a system for the computer-based management of letter-like messages and their transmission over computer networks , in particular over the Internet . On the other hand, the messages transmitted on this electronic path are also referred to as e-mails themselves.
In addition to the World Wide Web, e-mail is an important Internet service , not least because it is possible to send text messages as well as digital documents (e.g. graphics or office documents) around the world in just a few seconds to send.
In contrast to telephone or Internet relay chat , which enable simultaneous (synchronous) communication, e-mail - like letter post - is an asynchronous communication medium : The sender sends his message regardless of whether the recipient can receive it immediately or not.
Articles and spellings
In Germany, the feminine form (e-mail) of the grammatical gender has largely established itself as standard language , whereas in Switzerland the neuter (e-mail) , while in Austria and in parts of southwest Germany both forms are used. The Austrian dictionary names both the feminine and the neuter form, but names the latter first. The fact that the neuter form predominates is underlined by the fact that "e-mail" is explained as "send an e-mail".
According to Duden , Wahrig and the official vocabulary of the reformed German spelling, e-mail is the correct spelling.
A less common synonym is the term E-Post .
history
Before the advent of e-mail, messages were transmitted as letters or telegrams , later also - as the first two electronic transmission methods - telex and teletex as well as fax . At the end of the 1980s, e-mail began to spread around the world - it was one of the first applications to use the possibilities of the Arpanet . The introduction of e-mail was not specifically driven, but conquered the network because of user behavior. This surprised the Arpanet initiators, because in 1967 Lawrence Roberts , who later became the head of IPTO , said that the possibility of exchanging messages between network participants was not an important motivation for building a network of scientific computers (“ not an important motivation for a network of scientific computers ").
A forerunner of e-mail was the MAIL system command in the Multics extension of the CTSS time-sharing system at MIT , proposed in 1964/65 by the system developers Glenda Schroeder , Louis Pouzin and Pat Crisman and implemented in 1965 by Tom Van Vleck. JCR Licklider suggested ways of sending mail in the Arpanet as early as 1968 and the idea was discussed among the developers ( RFC 196 , " Mail Box Protocol " by Richard W. Watson of July 20, 1971). After Multics, in which a mail program for communication between users had been implemented, was connected to the Arpanet in October 1971, a mail program was implemented via the Arpanet by the MAC Networking Group under Mike Padlipsky in early 1972 .
Ray Tomlinson sent the first electronic letter in 1971 and has been the inventor of e-mail ever since. He was involved with the research company Bolt, Beranek and Newman (BBN) in the development of the TENEX operating system , which was available on many computers connected to the Arpanet, and worked among other things on the SNDMSG program for the transmission of messages between users the mainframe and the CPYNET protocol for transferring files between computers. As mentioned, programs like SNDMSG have existed since the early 1960s. They allowed users to add text to other users' mailboxes on the same computer. At the time, a mailbox was nothing more than a single file that only one user could read. In 1971 Tomlinson came up with the idea of changing CPYNET so that it could add to existing files and then incorporate it into SNDMSG. The first application of this combination was a message from Tomlinson to his colleagues, in which he announced in late 1971 that messages could now be sent over the network by adding the " @ " character and the host name of the computer to the user name of the addressee .
At the beginning of the 1980s, systems with which messages could be transmitted developed in most networks parallel to the Internet. These included mailbox systems, X.25 , Novell and BTX . These systems were largely supplanted by the spread of the Internet in the mid-1990s. The RFC 822 protocol dates from 1982 . RFC 822 was replaced by RFC 2822 in 2001 , which in turn was replaced by RFC 5322 in 2008 .
The first Internet e-mail was received in Germany on August 3, 1984 at 10:14 am CET : Michael Rotert from the University of Karlsruhe (TH) received a message of greeting from Laura Breeden at his address “rotert @ germany” (“breeden @ csnet-sh.arpa ”) to the US platform CSNET from Cambridge (Massachusetts) for electronic communication by scientists, which had been sent the day before (on August 2, 1984, 12:21 pm). A copy of this e-mail was sent as “CC” to the head of the project, Werner Zorn with the address (“zorn @ germany”) .
“Welcome to CSNET! Michael, This is your official welcome to CSNET. "
Today, emails are mostly sent via SMTP . Various protocols exist for retrieving e-mails from the target server, such as POP3 , IMAP or webmail . X.400 is an open standard that is mainly used in LAN or WAN .
The first major e-mail discussion group to emerge at Arpanet was a mailing list called "SF-LOVERS," in which a number of DARPA researchers participated in public discussions about science fiction . SF-LOVERS appeared in the Arpanet in the late 1970s. Initially, attempts were made to intervene because such activities had little to do with research, even if interpreted in the most liberal manner. The list was therefore blocked for a few months. In the end, however, those responsible at DARPA were convinced with the argument that SF-LOVERS was an important pilot project for researching the administration and operation of large mailing lists. The systems engineers had to rebuild the system repeatedly so that it could cope with the explosion in the volume of messages.
In 2014, around 506.2 billion emails were sent in Germany. In 2015, an estimated 4.353 billion email accounts were in use by 2.586 billion users worldwide. 81% of Germans sent and received emails in 2015.
Access to email
There are two options for writing, sending, receiving and reading e-mails (user interfaces).
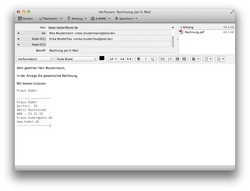
An e-mail program, also known as an e-mail client or mail user agent (MUA), can be used to use e-mail. Such a program is installed locally on the user's computer and communicates with one or more e-mail inboxes .
Alternatively, you can access your email via webmail. The user manages his e-mails in his web browser. This is made possible by a web application on the web server of the e-mail provider , which in turn accesses the e-mail inbox on the web server.
Elements and formatting of an email
Structure of an email
E-mails are internally divided into two parts: the header with headers and the body (text body) with the actual content of the message. In addition, further subdivisions are defined within the body.
Header - the head of the email
The header headers mentioned an email provide information about the way that e-mail has taken, and provide clues to the sender, recipient, date of creation, format the content and stations of the transmission. The user will normally not need many details from the header lines. This is why e-mail programs offer to hide the header except for the basic data such as sender, recipient and date. If necessary, the header can be made completely visible again at any time.
Body - the content of the email
The body of an email is separated from the header by a blank line and contains the information to be transmitted in one or more parts.
According to RFC 5322 section 2.3, an e-mail may only contain characters from the 7-bit ASCII character set. If other characters, such as German umlauts, or data, such as images, are to be transmitted, the format must be declared in the header section and the data must be encoded appropriately. This is regulated by RFC 2045 ff (see also MIME and Base64 ). Current e-mail programs automatically encode text and file attachments (see below) if necessary.
The message can consist of a plain text , a formatted text (for example HTML ) and / or binary data (for example an image or fax , see below for file attachments). Several formats can be sent as alternatives or any other files can be attached. The signature and footer may form the conclusion . All of these additional parts are optional, so they don't necessarily have to appear in an email.
- Signature - the signature under the email
- A signature is optional, it may be part of the body. The most common signature to be found is what is known as the signature . It provides more detailed information on the sender, for example their real name, job, personal preferences and the like. In addition to or as an alternative to this “simple” electronic signature, an e-mail can also contain a digital signature which makes forgeries or falsifications of the e-mail recognizable. Under certain conditions, a digital signature can legally represent a qualified electronic signature , which then has legal force equivalent to the manual signature of a letter. See also section Evidence .
- As an alternative to the signature, a vCard (electronic business card, although the v stands for something else, see there) can also be attached. However, this standard could not prevail decisively.
- In Germany, certain content is required for business e-mails, see signature (e-mails in business transactions) . In addition, if a signature specifies the sender, this represents an electronic signature within the meaning of the Signature Act .
- Mailfooter
- Text under the mail, mostly used for advertising in private mail services.
Attachments
- An attachment, also known as an attachment, is a file that is sent as an attachment to the text of an email. Technically, this file is part of the body, but it is perceived as separate and is also treated as such in common usage.
- File attachments can contain computer viruses , so they should be handled carefully. A file attachment should only be opened if the e-mail comes from a trustworthy sender.
- A file attachment is typically encoded according to the MIME protocol, which regulates the subdivision of the body and the encoding of the file.
- The size of a file attachment is in principle not limited; In reality, however, the sender's email provider or the recipient's email inbox often limit the maximum size of an email that can be sent.
- A file attachment is usually around a third larger than the corresponding file on a data carrier, because most file types in MIME mails are Base64- encoded.
Formatting in HTML
E-mails formatted in HTML are partly unintentionally and unconsciously sent by the default setting of the e-mail program used, in particular by Microsoft programs, and partly deliberately in order to be able to use fonts , for example in e-mail newsletters .
Although the HTML format is standardized , it was not originally intended for use in emails. Among other things, this led to the fact that in the past there were many, also conceptual, security gaps in the HTML rendering engines of e-mail programs, which on the one hand contributed to the spread of e-mail worms and on the other hand unintentional information about the recipient have disclosed ( tracking pixels ). This situation has improved over time and known problems, such as the standard execution of active content (e.g. JavaScript ) or the automatic reloading of external images, have been mitigated by other default settings. The often inconsistent deactivation of potentially dangerous HTML features in various e-mail programs also has the effect that optical effects or formatting are not displayed as intended by the sender.
In principle, HTML-formatted e-mail messages always offer considerably more opportunities for attack and are therefore potentially more insecure than plain text messages. That is why many IT advisors and software manufacturers recommend deactivating or completely excluding the HTML display of e-mails at least in the preview window of the e-mail program and not sending any e-mail messages in HTML format yourself. The Federal Office for Information Security (BSI) recommends:
- If you want to be on the safe side, you can configure the e-mail client so that it only displays an e-mail as text by default.
- Generally, no HTML-formatted emails or emails with active content should be sent.
Delivery of an email (principle)
The E-Mail adress
An e-mail address uniquely identifies the recipient of an e-mail and thus enables delivery to this recipient. As it is used for the transport via SMTP in the Internet, it consists of two parts: In [email protected]is wikipedia.orgthe domain part , infothe local part . (Other transport mechanisms such as UUCP or X.400 use a different address syntax.) The domain-part names the MX resource record (mostly identical to the domain) of the mail server to which the e-mail is to be delivered. The local-part uniquely identifies the owner of an e-mail mailbox on this mail server.
The way of a typical email (principle)
In a typical case, an email takes the following route from a sender (in the example: Anja) through the Internet to an addressee (in the example: Bertram), see figure on the right.
- Anja writes an e-mail to Bertram in her e-mail program on her laptop.
- The email program on Anja's laptop sends the message to the mail server of Anja's email provider "ArKom" via the home WiFi and via Anja's Internet service provider.
- The “ArKom” mail server sends the email via the Internet (and possibly many other servers) to the mail server of Bertram's “HeissBrief” email provider.
- The “HeissBrief” mail server stores the incoming e-mail from Anja in Bertram's e-mail inbox.
- The e-mail program on Bertram's smartphone regularly calls up the e-mail box for “HeissBrief” via UMTS and Bertram's telecommunications provider. As soon as it finds Anja's email there, it downloads it to Bertram's smartphone.
- As soon as Bertram sees the new e-mail in the inbox of his e-mail program, he opens and reads it.
Special features: Anja's Internet service provider and Anja's email provider will often be one and the same company. If Anja and Bertram have their e-mail accounts with the same e-mail provider, step 3 is omitted.
Delivery and read confirmations
Depending on the version of the e-mail program used, the sender of an e-mail can request a delivery confirmation and / or a read confirmation.
If a delivery confirmation has been requested, the sender (Anja in the above example) receives a Delivery Status Notification (DSN) in the form of an email as soon as the email has been successfully stored in the recipient's mailbox and the architectures involved support this. In relation to the example above, this would happen immediately after step 4.
If a read confirmation has been requested, the sender (Anja in the above example) receives a Message Disposition Notification (MDN) in the form of an email when the recipient (Bertram in the above example) opens the email addressed to him and this confirmation is triggered not prevented. In relation to the above example, this would happen immediately in step 6 when the e-mail is opened. The read confirmation can therefore not be interpreted to mean that the recipient actually read or even understood the email.
In this respect these confirmations have - but non-legal, but merely informative - character of a throw-writing (Delivery Confirmation) or of a registered letter with acknowledgment of receipt (read receipt) in Germany.
Technical details
The format of an e-mail is determined by RFC 5322 . After that, e-mails only consist of text characters (7-bit ASCII characters). In order to be able to transmit other characters, further Internet standards have been defined, with the help of which 8-bit characters are encoded in ASCII . The standard quoted printable, for example, encodes the letter “ß” as a string “= DF”. The standards of the MIME series have found widespread use, with the help of which not only special characters in texts but also binary files can be encoded, for example to send them as e-mail attachments.
In principle, the total size of emails is not limited. In reality, however, there are limits due to technical or administrative restrictions on the systems that transmit or receive the e-mail. E-mail providers , e-mail inboxes and participating mail servers can limit the size of an e-mail. In such cases, the limiting mail server should send the sender a bounce message (error message).
storage
Where the emails are permanently stored depends on the technology used by the end user. If he uses a web interface , the mails are always kept on the mail server. If he uses a mail program that reads the mails with the IMAP protocol , the e-mails are also held on a mail server. Originally, the alternative POP protocol provided that the mails were fetched from the server and deleted there at the same time. The client is therefore responsible for saving on its local mass storage device. With newer POP versions, however, it is also possible - depending on the server settings - to leave the mails on the server.
E-mails (locally or on the mail server) are often not saved individually as separate files, but grouped together in container files. mbox is a frequently used option under Unix / Linux, an alternative is Maildir .
Among other things, the file extension .emlused by programs such as Novell GroupWise , Microsoft Outlook Express , Lotus Notes , Windows Mail , Mozilla Thunderbird and Postbox is common for individual emails . The files consist of plain text in MIME format and contain the headers, the message content and attachments in one or more formats.
The e-mail program Pegasus Mail (PMail for short) uses its own mail folders .
Delivery of an e-mail: involved servers and protocols
Example of a process:
- Client sends SMTP request to the source mail server (a.org)
- Mail server requests "Mail eXchanger record" from the DNS server (ns.b.com)
- DNS server delivers MX record with priority list of target mail servers (b.com)
- a.org sends emails to all b.com one by one until someone accepts the email
- The destination mail server saves the e-mail until the user “Bob” picks up his e-mails via POP3.
Protocols used
- SMTP is a protocol for sending and transporting mail. To send via an e-mail program , you need the name of an SMTP relay computer , often referred to as an SMTP server. This corresponds to the delivery of a postal letter public mail box .
- POP3 is used to retrieve mail from the mailbox of a mail server . For the letter post it corresponds to the corridor to the letter slot on the front door.
- IMAP is also used to access mailboxes that are on mail servers. In contrast to POP3, IMAP is designed to leave the mails on the server and manage them there in folders.
- SMAP is a further development of IMAP, which is still in the experimental stage.
Nowadays mainly SMTP, POP3 and IMAP are in use, often in connection with SSL encryption (see SMTPS , POP3S and IMAPS ).
running time
The transit time (transport time of a mail item from the sender to the recipient) of the e-mail can be a problem because - unlike, for example, faxes - it cannot be foreseen and can fluctuate greatly under unfavorable conditions. The fluctuations in the runtime are influenced by a large number of parameters, above all by the utilization of the mail systems involved and the transmission capacity of the lines connecting the mail systems available for e-mail. If the recipient's mail server cannot be reached for a longer period of time, or if the mail is only transmitted to the recipient's server at long intervals, it can take several days.
The disadvantages of the not firmly defined runtime are, however, almost negligible in today's modern e-mail systems (rarely more than a minute worldwide), since in well-maintained systems only relatively seldom major errors occur that could cause longer runtimes. However, delays can also occur in modern e-mail systems due to various spam protection measures ( e.g. the greylisting process ).
Advantages and disadvantages
The email system has a few advantages and disadvantages, which are listed below:
Practical advantages over paper mail
A major advantage of e-mails is that they can be transmitted very quickly (within a few seconds) and read by the recipient. The practical effort of sending and receiving an e-mail is lower, since no printing, enveloping, addressing, franking or post box dropping is required at the sender and no mail box emptying and letter opening at the recipient is necessary. Letters written on the computer can be sent directly and easily by e-mail and read directly on the recipient's computer and, if necessary, further processed.
The individual financial outlay (costs for sending an e-mail) is usually lower (no material and postage costs), provided that many e-mails are processed or the necessary infrastructure (computer with internet access) is already used by the sender and recipient for further use is available. In addition, the more effort and cost savings are, the more recipients are to receive the same email (circular). E-mail services are usually offered free of charge on the Internet for private use. They are generally funded by advertising.
With regard to the environmental friendliness of e-mails in particular, there are various discussions and views, as is the case with the Internet and computer technology in general. At least e-mails are more environmentally friendly than conventional letters in that they do not use any paper immediately and do not require any material transport (truck, train, plane, ship, etc.).
E-mails have the advantage over normal paper mail that their address and sender texts (e-mail addresses) are significantly shorter than with normal paper mail addresses with name, street / post office box, zip code, city and possibly country . E-mail addresses can largely be chosen freely and there is no need to use your own name in plain text (e.g. [email protected] ) as the e-mail address, provided the domain owner ( xyz.org) has not established any rules about the format of its email addresses or no laws are broken. Instead, pseudonyms can also be selected, which achieves a higher level of anonymity , since the e-mail address does not make any information or only to a limited extent (derived from the domain) or allows conclusions to be drawn about names, origin, gender, address, geosocial status, etc. Likewise it is possible to have several different e-mail addresses.
In terms of practical handling, e-mails also offer advantages over paper mail. An email can be sent to several recipients at the same time, whereby concealed recipient lists ( BCC ) can also be used so that the complete recipient list cannot be viewed by every recipient. E-mails can easily be archived on the computer and the archives can easily be searched for quick retrieval of an e-mail. Sent and deleted e-mails can also be archived automatically.
E-mail systems also offer some practical automatisms. E-mails can be forwarded automatically if desired, either to a different e-mail address or on other communication channels, for example as SMS or fax. The reverse is also possible, i.e. forwarding a fax or an SMS to an e-mail address. If desired, an automatic reply can be sent to the sender when an e-mail is received (for example an absence message) or a notification is given that a new message has been received. It is also possible to automatically sort out unwanted e-mails (spam filters & personal blacklists) or to sort them automatically into various folders according to freely definable criteria.
Another advantage is that further files of any kind can be attached to e-mails, which the recipient can use. E-mails (only the body of the text, not the head) can also be encrypted for data protection reasons and electronically signed for authentication. If desired, digital business cards with additional information (such as address or telephone number) can be sent as an attachment to an e-mail, which makes it easier for the recipient to fill and maintain his address book with e-mail contacts.
There are also practical advantages in replying to e-mails. Replies to e-mails can be started more easily and quickly by automatically adopting the sender and CC recipients of the original e-mail as recipients of the reply. Likewise, the content of the original e-mail can be quoted or added to replies in order to be able to refer to or reply more easily in the reply or to document the discussion thread.
Spam
As spam [ spæm ] or junk mail ( [ dʒʌŋk ] ; English for 'waste' or, danish ') unsolicited e-mails are called, mostly advertising, etc. included. The efficiency of e-mail is partially limited by the massive traffic of spam, i.e. e-mails that are sent to the recipient unsolicited and often have advertising content, insofar as the processing of spam e-mails costs the recipient time. As of around 2002, spam has accounted for more than 50% of global e-mail and since 2007 approximately 90%. In 2010 around 107 trillion emails were sent, with a spam share of 89.1%. In October 2015, the proportion of spam in emails was 54%.
In 2014, the Bonn Regional Court ruled in relation to a lawyer’s liability case that the spam folder of an account, which is made available as a contact option in business dealings, has to be checked daily in order to retrieve e-mails accidentally rejected as advertising.
Authenticity, data protection and integrity
Like any means of communication, e-mail must meet various requirements in order to be considered a secure means of communication. The most important criteria here are authenticity, data protection and the integrity of an email.
The authenticity of an email means that it is ensured that the email actually originates from the sender, i.e. is an original and not a fraudulent forgery. In the case of emails, data protection essentially refers to protection against being read by third parties on the transmission path. When integrity is called the protection objective that the e-mail content remains complete and unaltered during transmission.
To achieve authenticity, privacy and integrity already exist various protective mechanisms, as already described elsewhere ( encryption , sender authentication , Pretty Good Privacy , GNU Privacy Guard , S / MIME ). However, these protection mechanisms are not yet applied to the majority of today's e-mail traffic. Without these protective mechanisms, however, conventional e-mails have less protection than a normal postcard .
The following subsection is intended to illustrate the very low security standard of a conventional email compared to a postcard as vividly as possible.
Comparison with the postcard
Conventional (unencrypted) e-mails can be compared to a postcard because the content is sent in an open and easily readable manner. Encrypted email is like a locked letter, but email encryption is still the exception today. But even with an encrypted e-mail, in addition to the sender and recipient (like a letter ), the subject line and generally all headers can be read.
Like mail, e-mails are stored at the e-mail service provider like at a post office. This means that unencrypted e-mails can be read like postcards from the e-mail service provider. In addition, unlike normal paper mail, emails can be easily and automatically searched for useful information and evaluated.
To increase the reliability of the e-mail service, copies of e-mails are made by the e-mail service provider and stored for a while, as if the post office were making and archiving photocopies of postcards and letters.
In the case of paper mail, the delivery can be documented (registered mail with acknowledgment of receipt) or the post automatically returns to the sender if acceptance is refused. Conventional e-mails also have the mechanism of confirmation of acceptance, but the recipient can still read the e-mail without having to confirm acceptance to the sender. The refusal of acceptance as an independent mechanism with feedback to the sender does not exist with conventional e-mails.
A postcard is usually only accepted, transported and given to the recipient by one postal company for domestic mail or two postal companies for international mail. An e-mail, on the other hand, usually passes through the computers of different companies in different countries. In theory, an e-mail can make its way across half the globe through many countries via many intermediate stations (computers), and everyone involved can read it. It has become known in particular through Edward Snowden that secret services systematically search e-mail traffic for certain keywords.
A burglar has to appear in person at a post office, but a hacker can (in the event of a security breach) simply break into an email inbox remotely without leaving any traceable trace or even noticing the break-in. With e-mail espionage, burglars have less risk to fear with higher chances of success and better tools. However, the intruder must have a high level of professional qualification.
With paper mail, security measures are easy and comprehensible for everyone to implement (registered mail with acknowledgment of receipt, seal, safe, alarm system ...). In the case of emails, security measures are much more difficult and only halfway controllable by advanced computer users. But also negligence on the part of the user, e.g. B. by choosing insecure passwords, the chances of burglars ease.
Just as easily as sending a letter or postcard, e-mails can be sent with the wrong sender address, which is often observed with spam or phishing , for example . Recipient, copy and blind copy addresses ( marked with TO , CC or BCC in the e-mail header ) can be forged ( e-mail spoofing ).
Paper mail is usually signed (signed) by hand and a fraudster has to forge the handwriting to defraud, but the electronic signature is dispensed with in the vast majority of e-mails and unsigned e-mails are received by the recipient despite the lack of or limited legal force generally accepted.
In summary, it can be said that a much lower security standard is generally accepted with conventional e-mails than with a postcard, although hardly anyone would think of sending personal sensitive data with a postcard. This acceptance is probably due to the lack of transparency of email technology, because the risks are not so obvious, not recognizable or simply unknown to the non-computer expert, or the disadvantages are simply accepted in comparison to the many advantages.
Sender authentication
In 2004 there were various attempts to get the spam problem under control. The procedures Sender ID from Microsoft , Sender Policy Framework (SPF), DomainKeys from Yahoo and RMX competed for the implementation. An IETF working group tried to define a standard. The functionality is similar for all procedures. An additional entry in the DNS should make it possible to verify the sending mail server. The IETF working group ultimately failed due to unresolved patent claims on the part of Microsoft. The various procedures are now to be implemented as RFCs in their own procedures .
documentation
In contrast to telephone calls, the sender and recipient of emails automatically receive written documentation about the communicated content. This can be stored in the e-mail program used or in an archive system and can be used later for recapitulation.
Quality of the communication content
Compared to spontaneous statements during a telephone conversation, the written formulation offers the opportunity to better think through and structure the content to be conveyed. Likewise, the risk of a thoughtless statement that is regretted in retrospect is reduced.
On the other hand - in contrast to a telephone call - the author of an e-mail must expect that his statements can be read as often as required in the long term and can be forwarded by the recipient to practically any selection of other readers with little effort or even thoughtlessly. They therefore have a stronger public character.
In terms of linguistic psychology, their recipients often perceive e-mails to be stronger and harder than the author intended. In contrast to a telephone call or a personal conversation, there is no immediate feedback while the communication is being written and thus an essential regulating function.
Email versus social media and wikis
The ease with which it was used led to e-mail becoming a worldwide standard in electronic communication. In corporate communication, however, it is not only the information overload caused by the flood of e-mails that is perceived as a problem.
The fact that the sender has no control over the extent to which his e-mail has been processed or that too many employees are unnecessary or that other parties involved in the business process may not be informed at all limits the usefulness of e-mail in the business environment. Analysts assume that in the future the proportion of communication that will be handled via social community platforms (with task lists, processing status and subscription functions) and wikis instead of email or instant messaging will increase wherever transparency, structuring and networking of project knowledge from Meaning are.
Modern networks in knowledge-intensive companies are organized more horizontally. However, emails tend to promote hierarchical structures.
Legal Aspects
Evidential value
Legally relevant declarations and liabilities can be established even with simple e-mails. E-mails, however, have little evidential value, since with conventional protocols and log mechanisms the sender no longer has the option of proving when they are sending what to whom, whether the recipient has received the e-mail or whether it was actually sent . Over time, the data stored in the so-called user account will be deleted.
A digital signature and, above all, a qualified electronic signature can create liabilities in legal transactions ( civil law , administrative law ) that are easier to enforce in court. Colloquially, one speaks of a "digital signature". The binding setting of a time stamp is also recognized under certain conditions. Further details are regulated, for example, in the German , Austrian or Liechtenstein Signature Act. However, a signature cannot prove that the message has been received; this requires, for example, a response - ideally also signed. Some service providers offer solutions that automate signature, encryption and response ("registered e-mail").
In Germany, the legal literature takes the view that an e-mail is deemed to have been delivered as soon as it is received on the server of the recipient provider. The arrival of an email in the recipient's personal user account is not absolutely necessary in order to achieve the status of delivery. Transmission errors when sending an e-mail from the recipient provider to the recipient's individual e-mail account cannot be asserted by the recipient in order to question the legal consequences of an e-mail. More recent judgments confirm this view. For example, brokerage contracts and warnings can be sent legally by e-mail.
Publication of emails
General
There is no general ban on publishing e-mails in Germany. Only the content of the mail can give the author the right to take action against the publication. Various legal consequences are possible, ranging from injunctive relief, civil law claims for damages in money to criminal liability, other legal consequences are possible.
In civil law context, publication of a letter can the copyright infringing the author, however, this is not the case with "general nature". Furthermore, the publication can violate the general personality rights of the author, in this respect the courts of instance, following a judgment of the Federal Court of Justice from 1954 , carry out an extensive weighing of interests in each individual case. This general case law should also apply to e-mails.
It can be assumed that the case law ( Higher Regional Court of Rostock , decision of April 17, 2002 - 2 U 69/01), according to which an unwritten secondary contractual obligation of both contracting parties applies to business letters that are exchanged within the framework of a contractual cooperation, the letters to be treated confidentially, also applicable to business e-mails, at least if they have been sent in encrypted form.
Decision of the Regional Court of Cologne 2006
The Cologne Regional Court decided in the guiding principle of the judgment on file number 28 O 178/06:
- Whether the unsolicited publication of e-mails is lawful has to be determined in a comprehensive weighing of interests.
- If a business e-mail, which is only intended for a certain group of recipients, is published without being asked, this represents an interference with the general privacy rights of the e-mail sender. This is all the more true if the person publishing the said e-mail in an unfair manner.
The publication of an external email to a third party on a website can, as evidenced by this judgment, constitute an encroachment on the general personal rights of the sender in the form of the confidentiality . In this respect, however, the illegality is not indicated, but can be positively determined in individual cases, which requires a comprehensive weighing of interests and interests. The purpose of the publication and the purpose sought by the publishing party as well as the form, type and extent of the intervention are in opposition. A violation triggers an obligation to pay damages .
The regional court equates the e-mail with a sealed letter.
The judgment relates to a case in which e-mails have been published which, on the one hand, were addressed to a third party and, on the other hand, were obtained unfairly by the publishing party. In the case of the publication of e-mails addressed to the person concerned, the reasoning of the judgment is not applicable.
monitoring
In many countries, e-mail traffic is now monitored by the state. In Germany, Internet service providers have been obliged since 2005 to have the appropriate hardware and software in stock in order to be able to follow a surveillance order immediately without receiving financial compensation for the resulting costs.
commercial use
Austria
- The company code has been in force in Austria since January 1, 2007 . This stipulates an imprint obligation for e-mails for entrepreneurs .
Germany
- In Germany, the law on electronic commercial registers and cooperative registers as well as the company register ( EHUG ) of 10 November 2006 have introduced new formal requirements for e-mails, faxes, postcards and other letters that replace business letters since January 1, 2007. These regulations also apply to all commercial e-mails such as offers, orders, cancellations and newsletters. The e-mail must therefore contain the same information as messages sent in classic letter form, for example the full company name with legal form, the location of the commercial register, the competent registry court and the commercial register number, all managing directors or board members and, if applicable, the chairman of the supervisory board. Violations can be punished with fines or warned by competitors. See also signature (e-mails in business transactions) and e-mail archiving .
- In the case of info mails to customers, invitations to events, etc., not all e-mail addresses of the recipients may be entered in the To or CC field without their consent , since the addresses already represent personal data and may not be passed on to third parties. The BCC field, on the other hand, can easily be used for corresponding mail, since the recipient list cannot be seen here for the recipients.
Use of language
For the classic letter of expression is in English variously to distinguish snail mail (Engl. Snail mail ) is used.
In 2003, the French Ministry of Culture banned the use of the word e-mail in official correspondence from state institutions and instead prescribed the use of the suitcase word " courriel " (from " courrier électronique "). The term was already common in French-speaking Québec in Canada in the 1990s , where there is a stricter law protecting the French language than in France itself.
Although the Yiddish language is more strongly influenced by the English language than the German , the non- foreign language terms בליצפאסט (Blitzpost) and בליצבריוו (Blitzbrief) have established themselves there .
An e-mail with unfriendly, warning and unpleasant content is called nastygram in popular English . Aggressive emails are called flame emails .
Adequate behavior in electronic communications, including email communications and social networking, is known as netiquette .
See also
literature
- Etienne Ruedin, Carla Buser: email - the hermaphrodite . Alleged and real influences of e-mail on people. Benziger Education - Émosson, [Zurich] 2008, p. 90 ( Lulu (USA) - Summary of the common and non-uniform definitions of email in science from the point of view of language, gender, terminology, history, development, technology).
- Wayne Jansen et al .: Guidelines on Electronic Mail Security . Ed .: National Institute of Standards and Technology . February 2007, p. 139 ( csrc.nist.gov (PDF) - Recommendations of the National Institute of Standards and Technology).
- Holger Lüngen; Otfried Mickler (preface): Organization on the wire . Consequences of the use of e-mail in companies. Eul, Lohmar / Köln 2004, ISBN 978-3-89936-198-8 (Dissertation Gottfried Wilhelm Leibniz Universität Hannover 2003, XVIII, 287 pages).
- Paul Ferdinand Siegert: The History of E-Mail . Success and crisis of a mass medium. In: Technology - Body - Society . Transcript, Bielefeld 2008, ISBN 978-3-89942-896-4 (dissertation at the University of Lüneburg 2008, 360 pages).
Web links
- FAQs: Read and understand e-mail headers , th-h.de , Thomas Hochstein
- Online advertising right - email as evidence , online advertising right , Arno Glöckner
- Internet tutorial: sending and receiving e-mails , stefanbucher.net , Stefan Bucher
- E-Mail - About the nature of electronic mail in modern times , chaosradio.ccc.de , Chaos Computer Club Berlin e. V.
- RFC 2142 - Mailbox Names for Common Services, Roles and Functions
- RFC 2368 - The mailto URL scheme
- RFC 5321 - Simple Mail Transfer Protocol
- RFC 5322 - Internet Message Format
- RFC 5335 - Internationalized Email Headers
Individual evidence
- ↑ Duden | How do you write "E-Mail"? | Spelling, orthography. Retrieved December 11, 2019 .
- ↑ German or English pronunciation according to PONS large dictionary German-English / English-German (4th edition 1999) p. 246 or, p. 1286.
- ^ Fourth round: "E-Mail" (Genus) (Question 24e) , Atlas of German Everyday Language, Phil.-Hist. Faculty of the University of Augsburg
- ↑ Official Austrian Dictionary , 42nd edition, 2012, p. 207.
- ^ Advice for German Spelling: Part II - Dictionary. (PDF; 1.33 MB) Retrieved November 26, 2018 .
- ↑ Email - How do you write an email? , Ralph Babel
- ↑ Writing emails. In: Duden online. Retrieved February 28, 2015 .
- ^ Paul Ferdinand Siegert, Die Geschichte der E-Mail, Bielefeld: transcript 2008, p. 192 (dissertation University of Lüneburg)
- ^ Tom Van Vleck, The history of electronic mail
- ↑ The First Email ( Memento from January 2, 2013 in the web archive archive.today )
- ^ A b c Ray Tomlinson: The First Network Email. Retrieved May 30, 2009 .
- ↑ XXL city sign. In: Stadtwiki Karlsruhe. Retrieved October 12, 2017 .
- ↑ The 1st E-Mail (picture)
- ↑ 25 years of e-mail in Germany - And it made “Pling!” (Spiegel Online) and 25 years of e-mails in Germany - “My e-mail address was 'zorn @ germany'.” (Archive version) ( Memento from 5 June 2011 in the Internet Archive ), (Tagesschau, Das Erste)
- ↑ (Rheingold, 1994)
- ↑ (Hoods, 1993)
- ↑ a b c Facts and figures on e-mail traffic. Retrieved February 13, 2015.
- ↑ Email Statistics Report, 2015–2019 (PDF) March 2015, p. 3. Retrieved January 22, 2016.
- ↑ bsi.bund.de IT-Grundschutz- Kataloge M 4.199 Avoiding problematic file formats
- ↑ E-Mail and Spam Statistics 2010. Spiegel Online
- ↑ Email and Spam Statistics 2010 (PDF; 5.4 MB) MessageLabs Intelligence (English)
- ^ Bonn Regional Court, judgment of January 10, 2014 (Az .: 15 O 189/13)
- ↑ Peter Schütt: The end of the flood of emails is near . Computer Week, November 20, 2006.
- ↑ What are the benefits of digital mail? ( Memento from February 14, 2015 in the Internet Archive ) BITKOM - Federal Association for Information Technology, Telecommunications and New Media e. V., Berlin, 2012, p. 22 ff.
- ^ Ingo Leipner: The End of the Digital Stone Age , Berliner Zeitung, April 30, 2013.
- ^ Social Court Aachen , September 2006, Az, p. 11 AL 13/06: "E-Mails are lost."
- ^ Paul E. Mertes (lawyer), Johannes JW Daners (trainee lawyer): Access to e-mails in legal dealings - risk distribution when handling the digital mailbox. Zeitschrift für die Anwaltspraxis (ZAP), 2008, Issue 22, pp. 1239-1246.
- ↑ Effective brokerage contract by sending a synopsis to the previously communicated email address Oberlandesgericht Duesseldorf Decision v. 03/26/2009 - I-7 U 28/08 :: Online & Law. Retrieved March 17, 2019 .
- ↑ Sending of warning by email sufficient district court Hamburg judgment v. 07/07/2009 - 312 O 142/09 :: Online & Law. Retrieved March 17, 2019 .
- ↑ BGHZ 13, 334 - publication of letters , German case law
- ^ LG Cologne, judgment of September 6, 2006, Az. 28 O 178/06 , lexexakt.de , C. Loscher
- ↑ Fine for an open email distribution list
- ↑ Daniel von der Helm: Chronological Development of the Internet. Retrieved March 2, 2015 .
- ↑ Urban Dictionary ; Word Spy