Bluetooth
Bluetooth [ ˈbluːtuːθ ] is an industrial standard developed in the 1990s by the Bluetooth Special Interest Group (SIG) for data transmission between devices over short distances using wireless technology ( WPAN ). Connectionless and connection-based transmissions from point to point and ad-hoc or piconets are possible. The name "Bluetooth" is derived from the Danish King Harald Blauzahn ( English Harald Bluetooth ), who united warring parts of Norway and Denmark . The logo shows a monogram of the Norse runes ᚼ and ᛒ .
The radio processes for Bluetooth were originally developed for Ericsson by the Dutch professor Jaap Brille and the Swede Sven Mattisson . Other parts were added mainly by Nokia and Intel . Bluetooth forms an interface via which small mobile devices such as cell phones and PDAs as well as computers and peripheral devices can communicate with one another. The main purpose of Bluetooth is to replace wired connections between devices.

Technical background
Devices according to the standards of the Bluetooth SIG transmit as Short Range Devices (SRD) in a license-free ISM band (Industrial, Scientific and Medical Band) between 2.402 GHz and 2.480 GHz. They can be operated worldwide without authorization. However, interference can be caused by WLANs , cordless telephones ( DECT telephones in Europe have a different frequency band) or microwave ovens that work in the same frequency band. In order to achieve robustness against disturbances, a is frequency hopping (frequency hopping) is used in which the frequency band is divided into 79 channels in the 1-MHz-distance, which are changed up to 1600 times per second. However, there are also types of packets in which the frequency is not changed as often (multislot packets). At the lower and upper end there is a frequency band as a guard band to adjacent frequency ranges. Theoretically, a data transmission rate of 706.25 kbit / s can be achieved when receiving with a simultaneous 57.6 kbit / s when sending (asymmetrical data transmission).
From version 2.0 + EDR, data can be transmitted with EDR (Enhanced Data Rate) a maximum of around three times as fast, i.e. at around 2.1 Mbit / s. From version 1.1, a Bluetooth device can maintain up to seven connections at the same time, whereby the devices involved have to share the available bandwidth ( shared medium ) .
Bluetooth supports the transmission of voice and data. However, most devices can only manage three participants in a piconet during the necessarily synchronous transmission of voice .
An encryption of transmitted data is also possible.
Classes and range
| class | Maximum power | Range | ||
|---|---|---|---|---|
| (mW) | (dBm) | general | outdoors | |
| class 1 | 100 | +20 | approx. 100 m | approx. 100 m |
| 2nd grade | 2.5 | +4 | approx. 10 m | approx. 50 m |
| Class 3 | 1 | 0 | approx. 1 m | approx. 10 m |
The range that can actually be achieved depends on the transmission power and a large number of parameters. These include, for example, the sensitivity of a receiver and the design of the transmitting and receiving antennas used on radio communication links. The properties of the environment can also influence the range, for example walls as obstacles within the radio communication links. The types of data packets can also have an impact on the achievable range due to differences in length and security mechanisms.
To enable higher transmission rates over the 2.45 GHz ISM frequency band available worldwide, the Bluetooth SIG is planning the Alternate MAC / PHY Bluetooth extension; Here, Bluetooth is expanded to include the PHY and MAC layers of the IEEE 802.11 specifications (WLAN standards).
Eavesdropping and intrusion security
Bluetooth transmissions are only considered bug-proof or secure against unauthorized entry if they are operated as a connection with multi-level dynamic key assignment. With static key allocation, security is limited. When the key is transmitted, it is precisely this part of the communication that is particularly at risk, since a connection is only protected if the key is exchanged successfully.
Bluetooth is only no longer considered secure if the PIN code is too short (around four decimal digits or less). The Israeli researchers A. Wool and Y. Shaked described in their article from spring 2005 a method with which eavesdroppers can interrupt an existing, tap-proof connection and possibly break into a new connection. This data phishing is based on interrupting an existing connection by means of corresponding interference signals and encouraging the participants to re-establish an authenticated connection. The attacked have to re- enter their PIN on the devices used. The subsequent authentication with renegotiation of the connection key can then be intercepted using easily available special hardware and, if the PIN is badly chosen (because, for example, eight-digit numeric) PIN can be cracked by trial and error. This brute force attack can be accelerated further by using FPGA boards. This is not a purely academic attack, and there is a free program called BTCrack to prove it. After a successful attack, the attacker is in possession of the secret connection key and can establish any connections to the attacked devices. However, the attacker must know the Bluetooth address of a connected Bluetooth module. Contrary to popular belief, this cannot be prevented by the "invisibility mode".
This attack is possible if the attacker eavesdrop on the communication during the pairing process, the attacked person re-authenticates and uses a PIN that is too short. For devices that store the key permanently, there is therefore no risk, since no new PIN authentication is triggered after connection errors or a manual re-establishment of the connection, but the key stored on both devices is used. To protect against such attacks, the authors therefore recommend that remote stations be registered with PIN entry as rarely as possible. It is safer to save recognized remote sites permanently in the respective authentication lists and to deactivate re-authentication via PIN. In addition, users should use PINs that are significantly longer than eight characters, if the software used allows this. The Bluetooth protocol allows up to 16 characters (128 bits). In addition, an unexpected request for re-authentication should make you listen carefully and warn you to be careful.
Error handling
Up to version 2.0, Bluetooth knows two basic types of error handling (if used):
- 1/3 and 2/3 FEC block coding; enables the recipient to correct errors
- ARQ (Automatic Repeat Request) enables error detection at the receiver. In the event of errors, the corresponding package is requested again.
System architecture
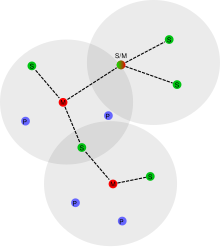
A Bluetooth network ( piconet ) consists of up to eight active participants, which can be addressed via a 3-bit address. All inactive devices can keep synchronization in park mode and activated in the network on request. There is an 8-bit address for parking mode, which can address 255 participants ("slaves"). In addition, the number of passive participants can be increased again via the 48-bit device address. The “master” controls the communication and assigns transmission time units (“slots”) to the “slaves” ( time division multiplexing ). A Bluetooth device can be registered in several piconets, but only act as a master in one network. Up to ten piconets form a Scatternet (from to scatter = to scatter ), whereby the participants can come into contact with each other. Each piconet is identified by a different frequency hopping sequence. However, the data rate usually suffers considerably in this Scatternet.
Such self-organizing radio networks - Scatternet - are implemented in a proprietary manner, until today no general solution has been standardized. This is due to the fact that no algorithm can be defined that meets all the requirements of a Scatternet at the same time and remains sufficiently lean and thus fast.
Bluetooth baseband
Two different physical data channels are made available. The synchronous data transmission is intended for the transmission of voice data with a data rate of 64 kbit / s. This procedure is called circuit-switched or synchronous connection (Synchronous Connection-Oriented - SCO). The other form of transmission is the packet switching or asynchronous connection (Asynchronous Connectionless - ACL), which requires a storing behavior of the transmission device, as with the Internet technology. Everything except voice is transmitted via ACL, in addition to all types of data, especially music. The Bluetooth protocol supports an asymmetrical data channel with data rates in version 1.2 of a maximum of 732.2 kbit / s in one direction and 57.6 kbit / s in the opposite direction, or a symmetrical data connection with 433.9 kbit / s in both directions . In the EDR version, higher data rates can be achieved.
Up to version 1.2 there are only HV1, HV2 and HV3 packets with good error correction (HV1) to none (HV3) for SCO transmission . These packets contain audio data for 1.25 ms, 2 x 1.25 ms or 3 x 1.25 ms and are accordingly sent every 1.25 ms, 2 x 1.25 ms and 3 x 1.25 ms. HV1 can be used when no other data needs to be sent. However, this operating mode has the highest power consumption, which is why almost all devices use HV3 packages. This has the advantage that you only need a third of the bandwidth for audio and the rest of the bandwidth can be used for ACL connections to the same or different devices.
With version 1.2 an extended synchronous transmission mode (enhanced SCO, eSCO) was introduced. For this purpose, new packet types and a more flexible division of the transmission period have been introduced. This also enables other audio formats to be transmitted, such as B. the SBC codec , which is also to be introduced in HFP version 2.0.
If no synchronous data packets are currently being sent, Bluetooth can offer asynchronous transmission . This is used to process all services, both the sending of user data packets and the transmission of control information, between two Bluetooth stations.
Bluetooth data packets consist of a 72-bit access code, a 54-bit header and a variable user data field from 0 bits to 2745 bits (packet type DH5). For Bluetooth 2.0 ° + EDR, up to 8168 bits of user data per packet (3-DH5) are possible.
Connection establishment
A connection is always established using the protocol architecture according to Bluetooth V2.1 etc. (new is from standard Bluetooth V3.0 and with the protocol Bluetooth V4.0 Low Energy a connectionless operation in the send and receive direction). A connection can originate from any device, which thereby rises to the “ master” above the responding “slaves ”.
As soon as Bluetooth devices are put into operation, the individual Bluetooth controllers identify themselves within two seconds via an individual and unmistakable 48-bit MAC address . In standby mode, unconnected devices listen for messages at intervals of up to 2.56 seconds (scan mode) and control 32 hop frequencies. The contact to the slaves is an inquiry message (of English inquiry = Inquiry (from) followed by a page message to page (Engl.) = Cry (as speaker) , message (Engl.) = Message ) is prepared if the hardware address of the devices is unknown. If the address is known, the first step is omitted. In the page state, the master sends 16 identical page telegrams on 16 different hopping frequencies that are intended for the slaves. Then the stations are in the connected status . On average, a connection is established within half the scan interval, e.g. 2.56 / 2 seconds (1.28 seconds).
If the master does not find a slave within a set time, page telegrams are sent on a further 16 hopping frequencies . This grouping should ensure a quick connection establishment if the "slave clock" is known. With adaptive hopping, the frequencies that are already occupied by other masters are omitted.
Since 2005, NFC can optionally be used to establish a connection between two Bluetooth devices . Bluetooth supports this additional RF protocol, especially when pairing Bluetooth OBEX for the first time .
Bluetooth protocol architecture
The Bluetooth specification was developed by the Bluetooth Special Interest Group (SIG). This includes protocols in a hierarchical order ( protocol stack , Eng. Protocol stack ) with which interactive services and applications are possible via mobile radio communications communicate. These are produced with the help of radio modules and are connectionless or connection-oriented .
The Bluetooth Special Interest Group (SIG) has also designed various application models for Bluetooth technology. The specification includes a description of the protocols with which these deployment models can be implemented. Special compositions based on these models are used with the profiles .
With Bluetooth Low Energy no will power saving mode called, but a special protocol stack, which differs from the previously known protocol stack, not replaced it, but opens up new possibilities for low energy consumption.
Energy saving modes
If there is no data to be transferred, a connection between a master and a slave can be put into energy-saving mode.
There are three energy saving modes:
- The HOLD mode is used for asynchronous absence. For example, a slave can report that it will not listen for 200 ms after a certain point in time. The master then does not address the slave for the specified time, and the slave does not listen to master packets either. Both devices can then use the time for other activities (scanning, scatternet, etc.).
- The SNIFF mode (from to sniff = to sniff ) is used to reduce periodic activity. It can e.g. B. inform a slave or master that it only listens every 500 ms for some time windows ("slots"). The SNIFF mode is used in almost all devices that are intended to reduce energy consumption.
- PARK mode is used to keep a device synchronized. However, the device cannot actively participate in the data traffic. Park mode is supported by almost all chipsets, but is still rarely used.
For all previous and new modes, details on reducing energy consumption in order to reduce the load on small batteries are dependent on the coordination of master and slave.
Security modes
The Bluetooth standard defines the following three security levels, from the most insecure to the most secure:
- Mode 1 (Non-Secure Mode): There are no security mechanisms in this mode. The devices only change frequency continuously to make eavesdropping difficult.
- Mode 2 (Service-Level Enforced Security): In this mode, it is up to the services used to enforce security mechanisms on the application layer . Services can be open to all devices, only provide authentication or require additional authorization .
- Mode 3 (Link-Level Enforced Security): In this mode, authentication takes place on the link layer when the connection is established . Encryption is optional.
Many cell phones can transfer data via Bluetooth. Malicious attackers can potentially cause high financial damage via Bluetooth through carelessly configured devices or incorrect implementations of the Bluetooth protocol in the devices by calling chargeable telephone and SMS services, reading private user data, writing phone book entries and manipulating the list of called numbers in order to cover up . General, device-independent DoS attacks at the network protocol level are possible with simple means (e.g. “ping” requests with large packets).
Bluetooth protocol stack
Bluetooth protocol stacks are software packages with drivers that enable connection to Bluetooth devices and contain services for using different Bluetooth profiles. Which stack you can use depends on the driver and the built-in chip.
The best known protocol stacks or their manufacturers are:
- affix
- BlueFRITZ! by AVM (development discontinued)
- BlueSoleil from IVT
- BlueZ (standard on Linux)
- In The Hand
- lwBT
- Microsoft
- Stollmann
- Toshiba
- Widcomm from Broadcom
Bluetooth stack is also a term for software packages that are required for the development of Java applications with Bluetooth functionality. For example, if a J2ME application is to be able to communicate with a J2SE server, a Bluetooth stack is required as an interface between the driver (e.g. Widcomm) and Java in addition to a Bluetooth driver (see above). Examples of Bluetooth stacks for Java are:
Bluetooth profiles
Data is exchanged between Bluetooth devices according to so-called profiles, which are defined as a layer above the protocol layer for the control of certain services. As soon as a Bluetooth connection is established, the devices select the profile used in each case and thus determine which services they have to provide for the respective other partners and which data or commands they need for this. For example, a headset requests an audio channel from a Bluetooth compatible mobile phone and controls the volume setting or regulation via additional data channels.
history
Since the late 1980s, there have been various efforts to avoid the tangled cables around a computer installation using wireless peripherals (e.g. wireless keyboards, printers with infrared interfaces, etc.). Various shortcomings (high power consumption, mutual interference, etc.) and, above all, a lack of standards prevented the breakthrough of these beginnings.
At that time, next to radio technology, infrared technology was very popular, and it looked as if the latter would prevail. In order to develop a manufacturer-independent protocol, around 30 companies (including HP , IBM , Digital ) joined forces in August 1993 and founded the Infrared Data Association (IrDA). The aim was to create a uniform protocol for data transmission via infrared. Numerous findings from the IrDA development were later incorporated into the newly acquired Bluetooth radio standard.
But the IrDA technology had to struggle with a central disadvantage: the required visual contact between the transmitter and receiver. Therefore, in 1994 Ericsson was commissioned to carry out a feasibility study to find a radio-based replacement for cable connections. The study gave a positive result, and in 1998 Ericsson , Nokia , IBM , Toshiba and Intel formed the Bluetooth Special Interest Group (SIG) to develop a standard that established mandatory specifications. The SIG published version 1.0a as the first final specification in July 1999, version 1.0b followed in December of the same year. Version 1.1 of the standard was only presented in February 2001. This was considered to be the first solid basis for marketable products, as the previous versions had a number of inaccuracies and errors.
The name "Bluetooth" is a homage to the Danish Viking King Harald Blauzahn , who was known for his communication skills. In the 10th century he succeeded in largely uniting and Christianizing Denmark . The name “Bluetooth” was originally a code name for the technology developed, which was later also used as a brand name due to the lack of good alternatives. A Scandinavian namesake was chosen because of the high involvement of Ericsson and Nokia in Bluetooth development.
Versions up to Bluetooth 3.0
A selection of important properties of the previous Bluetooth versions, all of which no longer correspond to the revision status of version 4.0 from December 2009 (see above):
- Bluetooth 1.0 and 1.0B (July 1999)
- Contains security issues from Bluetooth Hardware Device Address Transmission (BD_ADDR) ; maximum data transfer rate of 732.2 kbit / s
- Bluetooth 1.1 (February 2001)
- Signal strength indicator added Received Signal Strength Indication (RSSI) ; maximum data transfer rate of 732.2 kbit / s
- Bluetooth 1.2 (November 2003)
- Less sensitive to static interferers (e.g. WLAN) thanks to adaptive frequency hopping spread spectrum (AFH) ; new packet types for synchronous transmission (eSCO); maximum data transfer rate of 1 Mbit / s
- Bluetooth 2.0 + EDR (November 2004)
- About three times the data transmission speed thanks to Enhanced Data Rate (EDR) with a maximum of 2.1 Mbit / s; downward compatible, d. That is, EDR and non-EDR connections can be served at the same time.
- Bluetooth 2.1 + EDR (also called Lisbon Release , August 2007)
- New functions such as Secure Simple Pairing, Quality of Service .
- Bluetooth 3.0 + HS (also called Seattle Release , April 2009)
- Support for an additional high-speed (HS) channel based on WLAN and UWB is available for this version . The use of WLAN is clearly restricted locally. Communication works between individual devices (peer-to-peer) and not through distribution ( multicast ). The user does not need to log in for this either, the L2CAP protocol layer has been expanded to support this high-speed channel in addition to the standard Bluetooth channel. This means that a theoretical transfer rate of 24 Mbit / s can be achieved.
- With UWB ( ultra broadband ) as the physical transmission type (based on the ECMA-368 specification) and WiMedia MAC as the protocol layer, up to 480 Mbit / s were planned. Other protocols such as WUSB and IP should have been based on this specification .
- The specification was abandoned in October 2009.
- Bluetooth 3.0 + EDR
- "EDR" stands for "Enhanced Data Rate".
Bluetooth 4.0
Specification 4.0 was adopted on December 17, 2009. With this standard, the protocol stack Low Energy became available for the first time, and new profiles for Low Energy have been added continuously since then. Corresponding chips were already available in small numbers from the 4th quarter of 2010; further indications suggest that mobile phones equipped with Bluetooth 4.0 will be available from the 1st quarter of 2011. In June 2011, Bluetooth 4.0-compliant chips were already available from Atheros , CSR , Nordic Semiconductor, Texas Instruments , Toshiba and EM Microelectronic Marin.
- The 4.0 standard is backwards compatible with all previous versions. An improved error correction is used for connections with the previous protocols, and AES encryption with 128 bits should be used for the required level of security.
- Bluetooth Low Energy / Smart is part of the 4.0 standard, but does not offer any downward compatibility. It is possible to set up a transmission in less than five milliseconds and maintain it up to a distance of 100 meters.
- The most important advantage of using Bluetooth Low Energy in new end devices is the reduction in power consumption through optimizations such as the shorter setup time for a transmission or the sleep phases between the synchronized transmission cycles. However, audio data can no longer be transmitted as a result.
- Hybrid devices that support both Bluetooth Classic and Bluetooth Low Energy are called “Smart Ready”.
Announcements on the availability of devices with Bluetooth 4.0 remained speculative until mid-2011 and without confirmation of availability. Since then, a large number of different end devices from different manufacturers that support the Bluetooth 4.0 standard have been on the market. Since Android only supported Bluetooth 4.0 in version 4.3, which was released in mid-2013, the situation arose in the meantime that some mobile phones supported Bluetooth 4.0 on the hardware side, but could not use it due to the lack of a corresponding Bluetooth protocol stack.
Bluetooth 4.1
Version 4.1 of the Bluetooth specification was released in December 2013. Immediately afterwards, the first devices with the new standard were announced, e.g. B. the Samsung Galaxy Note 4 and the Nexus 6 .
Bluetooth 4.2 Smart
In December 2014, the Bluetooth 4.2 standard was introduced. The main focus during development was on enhanced security features, a higher transmission speed and an even more economical Bluetooth "Low Energy" mode. Devices such as the Samsung Galaxy Note 5 and the Apple iPhone 6 support this standard.
Bluetooth 5
On June 16, 2016, Bluetooth 5 was officially announced. According to this announcement, the range is to be quadrupled (100 m) and the data rate doubled (2 Mbit / s gross without EDR). In addition, new services such as location reporting are to be introduced. The final adoption took place on December 6, 2016. The Samsung Galaxy S8 is the first smartphone in which Bluetooth 5 has been implemented. According to the trade, the majority of the smartphones on offer will be equipped with Bluetooth 5 at the beginning of 2020.
Areas of application
computer
Special hardware is required to operate Bluetooth on a PC. Some computers (mostly notebooks) have this already integrated, otherwise small devices connected to the USB interface or PCMCIA cards are also available for this purpose. The operating system used also plays a crucial role. In Microsoft Windows , since Windows XP SP2 , it is no longer necessary to install a special driver thanks to the Microsoft Bluetooth stack supplied. However, you have a larger selection of supporting profiles with the Bluetooth stacks from other manufacturers. Current Linux distributions and Apple Macintosh models also support Bluetooth through their own certified Bluetooth stacks. Anyone who has a PC with Bluetooth at their disposal can also use the appropriate software to track down other Bluetooth devices within range and, depending on the range of functions of the software, see a detailed list of open services. Such software is called a bluetooth scanner.
Bluetooth applications on the computer
- SCO audio: synchronous headset operation (Skype, SIP etc.)
- AV or A2DP audio: HiFi music playback suitable for connecting one or more headphones
- Mobile phone synchronization (contacts, music files, mobile internet access, etc.)
- HID: input devices such as a mouse and keyboard
- Motion capturing: transmission of movement data to the evaluation computer (e.g. Xsens MVN)
- Two-factor authentication according to the U2F standard of the FIDO alliance
Hands-free kits and headsets
Many car radios function as a hands-free system by integrating the mobile phone via Bluetooth, so that there is no need to install special mobile phone brackets in the car. Not only can a call be received via Bluetooth, it can also be dialed and navigated. Useful additional information such as the number of the caller or their name is also transferred from the mobile phone address book to the car radio via Bluetooth. Hands-free systems outside the car also work via Bluetooth. Headsets that are connected via Bluetooth can often also answer incoming calls using a corresponding button.
The support of such control functions (e.g. activation of the voice assistant on the smartphone) varies greatly with the devices used and depends on the manufacturer's chips, resp. their programming according to the possibilities of the corresponding Bluetooth protocol stack.
Playground equipment
The toy industry uses this technique to make dolls and toy animals communicate and interact with one another.
The controllers of the Nintendo Wii / Wii U / Switch , the PlayStation 3 / PlayStation 4 , the Xbox One S / Xbox One X , Lego Mindstorms EV3 and the Ouya also use Bluetooth to communicate with the console.
communication
Bluetooth hotspots as radio cells enable cordless access to a network such as the Internet or a company LAN . Audio devices without Bluetooth, especially older cell phones and landline phones , can be expanded to include Bluetooth to a limited extent via a connected adapter. In recent years, many manufacturers have increasingly used Bluetooth, especially for motorcycle intercom systems, with ranges of up to 1.6 km. Particular advantages are very small sizes and the lack of annoying cables.
Universal additional factors for two-factor authentication can also communicate with operating systems or web browsers via Bluetooth , such as security tokens for the open U2F standard of the FIDO alliance .
Industry
Due to the adaptive frequency hopping method (AFH) used, Bluetooth offers a very reliable and interference-resistant radio link. This advantage of Bluetooth over other radio technologies was recognized early on by various manufacturers of automation products (e.g. Phoenix Contact , WAGO Kontakttechnik GmbH & Co. KG, Schildknecht AG ). As a result, Bluetooth-based industrial products were developed that are used in various areas of industry to communicate wirelessly between different components in machines. Meanwhile, the PROFIBUS user organization e. V. (PNO) Bluetooth is defined as a carrier process for wireless transmission of PROFINET data packets on the fieldbus level alongside WLAN . At the sensor / actuator level, 802.15.1 was also used as the carrier technology in the PNO standard WSAN-FA, but with a different protocol stack. The CAN in Automation Association (CiA) is also planning the specification of a Bluetooth-based system for the wireless transmission of CAN telegrams. Overall, the standardization efforts underpin the suitability of Bluetooth for industrial automation.
House technic
In the field of home automation and alarm systems, there are products that use Bluetooth 2.0.
Another application is Bluetooth as a key , for which any Bluetooth-enabled device can be used as a key. No additional software is required on the devices (mobile phones) for this.
Medical technology
In orthopedic technology, Bluetooth is used to adjust modern arm and leg prostheses. Settings such as stance phase damping and maximum load can be made via Bluetooth.
Hearing aids in higher price ranges are also available with Bluetooth receivers. This allows the signals from cell phones and audio devices to be selectively transmitted to the hearing aid via a transponder without any environmental distortion. The transponder communicates via Bluetooth and transmits the information to the radio range of the hearing aids.
With some insulin pumps , Bluetooth serves as an interface for communication with a blood glucose meter, a remote control or a personal computer.
Remarks
"HID Proxy Mode" for computers without Bluetooth support
The Bluetooth input devices are usually only available when the operating system and its Bluetooth stack have been loaded. This means that it is not possible to use a Bluetooth keyboard to e.g. For example, before loading the operating system, make settings in the BIOS or in the UEFI settings menu or wake up the PC from the S4 sleep mode using the "Wake up on Keyboard" function or switch it on from the switched-off mode. In addition, retrofitting a Bluetooth interface is not possible without problems in some systems for various reasons. This includes many smart TVs , many microcontroller boards, NAS systems, rack servers.
Some Bluetooth adapters overcome these problems with the "HID Proxy Mode". Using a microcontroller , such adapters themselves provide a Bluetooth stack for Bluetooth input devices. These devices can connect to the Bluetooth adapter before loading the operating system and can thus be used for the wake-up-on-keyboard function or changes in the BIOS or in the UEFI settings menu. The Bluetooth adapter pretends to be a normal USB HID input device to the BIOS and the UEFI firmware. It transfers the BT functionality to the operating system as soon as its Bluetooth driver and Bluetooth stack are loaded, which means that other Bluetooth devices can be used in addition to Bluetooth input devices.
The UEFI firmware itself could also provide a Bluetooth stack for Bluetooth input devices so that Bluetooth input devices can be used in the UEFI menu even without HID proxy mode support. A concrete implementation of a Bluetooth stack for the UEFI firmware of motherboards is not yet known.
See also
literature
- Martin Sauter: Basic course in mobile communication systems. From UMTS and HSDPA, GSM and GPRS to wireless LAN and Bluetooth piconets. 3rd, expanded edition. Vieweg, Wiesbaden 2008, ISBN 978-3-8348-0397-9 .
- Andreas Merkle, Anestis Terzis: Digital radio communication with Bluetooth. Theory and practice, bluetooth simulator, competing systems. Franzis, Poing 2002, ISBN 3-7723-4654-5 .
- Ralf Gessler, Thomas Krause: Wireless networks for the local area. Springer Vieweg, Wiesbaden 2015, ISBN 978-3-8348-1239-1 .
Web links
- www.bluetooth.com
- A short history of Bluetooth , July 14, 2014
- CHIP Bluetooth FAQ for beginners (only up to version 1.2), September 28, 2004
- Bluetooth 1.0 / 1.1 / 1.2 (IEEE 802.15) in the electronics compendium
- CRE 169 A look into the structure and security of the Bluetooth Protocol Stack , Tim Pritlove and Martin Herfurt via Bluetooth (podcast)
Individual evidence
- ↑ Bluetooth Fact or Fiction. In: bluetooth.com. Accessed April 22, 2018 .
- ↑ Speed and range. In: computerbild.de. December 31, 2009, accessed January 9, 2017 .
- ↑ Cracking the Bluetooth PIN1 .
- ↑ BTCrack Bluetooth PIN Cracker. In: nruns.com. Archived from the original on June 9, 2007 ; accessed on January 9, 2017 (English).
- ↑ Barn door Bluetooth. In: nruns.com. Archived from the original on June 9, 2007 ; accessed on January 9, 2017 (English).
- ↑ Stefan Krempl: 23C3: New hacking tools for Bluetooth. In: heise.de. December 29, 2006, accessed January 9, 2017 .
- ↑ A. Zanella, A. Tonello, S. Pupolin: On the impact of fading and inter-piconet interference on Bluetooth performance . In: The 5th International Symposium on Wireless Personal Multimedia Communications . IEEE, ISBN 0-7803-7442-8 , doi : 10.1109 / wpmc.2002.1088164 ( ieee.org [accessed August 9, 2018]).
- ↑ Get IEEE 802® Terms of Use for IEEE Standards Publications Delivered in Electronic Form ( Memento of May 7, 2006 in the Internet Archive )
- ↑ Core V3.0 + HS ( Memento from October 26, 2010 in the Internet Archive )
- ↑ Security. In: Bluetooth Special Interest Group. Archived from the original on April 5, 2010 ; accessed on January 9, 2017 .
- ↑ Bluetooth security modes . In: Gelsenkirchen University of Applied Sciences. Archived from the original on October 14, 2011 ; accessed on January 9, 2017 .
- ↑ Stefan Krempl: 22C3: New attacks on Bluetooth cell phones. In: heise.de. December 31, 2005, accessed January 9, 2017 .
- ^ Toshiba Bluetooth Portal. In: aps2.toshiba-tro.de. Retrieved January 9, 2017 .
- ↑ Matthias Kremp: Technology explains: What you need to know about Bluetooth. In: Spiegel Online . October 10, 2012, accessed January 9, 2017 .
- ↑ Dusan Zivadinovic: Bluetooth SIG turns away from UWB. In: heise.de. October 31, 2009, accessed January 9, 2017 .
- ↑ Sven-Olaf Suhl: Bluetooth 2.1 + EDR promises simple device coupling. In: heise.de. August 3, 2007, accessed January 9, 2017 .
- ↑ Bluetooth V4.0 Specifications & details out ( Memento from January 17, 2010 in the Internet Archive )
- ↑ Casio Bluetooth low energy watch wirelessly communicates with smartphones using new Nordic Semiconductor chip. In: bluetooth.com. Archived from the original on April 28, 2011 ; accessed on January 9, 2017 .
- ↑ Low energy RF transceivers ( Memento from March 15, 2013 in the Internet Archive )
- ↑ October 04, 2011: EM Microelectronic's CoolRF chip qualifies for Bluetooth V4.0. In: microwave-eetimes.com. February 11, 2016, accessed January 9, 2017 .
- ↑ Nicole Lee: Bluetooth 4.0: What is it, and does it matter? - CNET. In: cnet.com. October 5, 2011, accessed February 24, 2017 .
- ↑ Bluetooth learns to save. www.trainingdigital.info, archived from the original on January 18, 2012 ; accessed on January 9, 2017 .
- ↑ Apple is updating MacBook Air with next generation processors, Thunderbolt I / O, and a backlit keyboard. In: Apple press releases. Apple Inc., July 20, 2011, accessed on January 9, 2017 (You can only see that this is Bluetooth 4.0 from the feature list linked in the press release.).
- ↑ Bluetooth 4.0: Android only supports the new Bluetooth standard on paper. In: areamobile.de. March 10, 2013, accessed January 9, 2017 .
- ↑ Adopted Specifications. In: bluetooth.org. December 6, 2016, accessed January 9, 2017 .
- ↑ Samsung Galaxy Note 4 - Full phone specifications. In: gsmarena.com. Retrieved January 9, 2017 .
- ↑ Benjamin Schischka: Bluetooth 4.1 announced - the new standard can do that. In: pcwelt.de. December 5, 2013, accessed January 9, 2017 .
- ↑ Bluetooth 4.2 introduced: radio standard is safer, faster, more energy efficient. In: chip.de. December 5, 2014, accessed January 9, 2017 .
- ↑ Samsung Galaxy Note5 - Full phone specifications. In: gsmarena.com. Retrieved January 9, 2017 .
- ↑ Ben Schwan: Apple retrofits Bluetooth 4.2 on several iOS devices - Mac & i. In: heise.de. October 12, 2015, accessed January 9, 2017 .
- ↑ Bluetooth® 5 Quadruples Range, Doubles Speed, Increases Data Broadcasting Capacity by 800%. In: bluetooth.com. June 16, 2016. Retrieved January 9, 2017 .
- ↑ Jon Fingas: Samsung's Galaxy S8 is the first phone with Bluetooth 5.0. In: engadget. Verizon Media (Oath), March 29, 2017, accessed January 30, 2020 .
- ↑ Sena
- ↑ Cardo Systems. In: cardosystems.com. Archived from the original on January 18, 2013 ; accessed on January 9, 2017 (English).
- ↑ INTERPHONE F4 STEREO ( Memento from June 27, 2009 in the Internet Archive )
- ↑ The last word in Handsfree Motorcycle Bluetooth communication. (No longer available online.) Cardo, archived from the original on March 8, 2012 ; Retrieved March 8, 2012 .
- ↑ Anne Elisabeth Vallestad: WISA Becomes WSAN - from proprietary technology to industry standard. (PDF) April 17, 2012 (PDF)
- ↑ Wilfried Eckl-Dorna: The test: What high-end hearing aids with Bluetooth do in everyday life. In: wiwo.de. February 11, 2009. Retrieved January 9, 2017 .
- ↑ Dusan Zivadinovic: Bluetooth takes off. In: heise.de. November 16, 2005, accessed January 9, 2017 .
- ↑ Proxy firmware enables Bluetooth keyboard and mouse to work from boot up. In: csr.com. Archived from the original on September 12, 2013 ; accessed on January 9, 2017 (English).