Enigma (machine)


The Enigma ( Greek αἴνιγμα aínigma , German ' Rätsel ' , spelling also: ENIGMA ) is a rotor key machine that was used in the Second World War to encrypt the Wehrmacht's communications. The police , secret services , diplomatic services , SD , SS , Reichspost and Reichsbahn also set them as secret onesCommunication a. Despite various improvements in encryption quality introduced before and during the war, the Allies succeeded in deciphering German radio messages almost continuously with a great deal of personnel and machine effort .
history


During the First World War (1914–1918), the German military was looking for a replacement for the now outdated, cumbersome and insecure manual encryption methods , such as ÜBCHI , ABC-Chiffre and ADFGX , which had been used until then. For this came Machinery method into consideration because they easier handling and improved cryptographic promised security. With the introduction of the electric typewriter and teleprinter at the beginning of the 20th century, several inventors, some independently of one another and almost simultaneously, came up with the idea of the rotor principle for encrypting texts. The first were the two Dutch naval officers Theo van Hengel and Rudolf Spengler in Batavia (then capital of the Dutch East Indies , now Jakarta , capital of Indonesia ) in 1915 . However, they were not allowed to apply for a patent for their invention. The next was the American Edward Hugh Hebern in 1917 ( patent application 1921 ). In 1918, the German was followed by Arthur Scherbius (picture) and finally in 1919 the Dutchman Hugo Koch and the Swede Arvid Gerhard Damm , all their ideas rotor cipher machines for patent anmeldeten.
The inventor of the Enigma was Arthur Scherbius (1878–1929), an electrical engineer with a doctorate and successful entrepreneur , whose first patent for this was dated February 23, 1918 (see also: Enigma patents ). In the same year on April 15, he offered his new invention to the Imperial Navy , which tested a first “trial machine” and praised its “good key security”. Furthermore, the Reichsmarineamt came to the conclusion that "for the time being, the use of machines would not be worthwhile with the type of naval key traffic".
After the war, Scherbius decided to market the machine for civil applications. On July 9, 1923, the Chiffriermaschinen-Aktiengesellschaft (ChiMaAG) was founded in Berlin ( W 35 , Steglitzer Str. 2, today Pohlstrasse in Berlin-Tiergarten ) for production purposes. The first model of the Enigma (1923) was the " trading machine " (picture) . It was quickly followed by “ Enigma Writing ” (1924). The new cipher machines were offered for sale commercially at trade fairs , such as in Leipzig and Bern in 1923 and at the International Postal Congress of the Universal Postal Union in Stockholm in 1924 .
This also aroused the interest of the German military, who in the meantime had learned of the Allied successes in decoding through publications such as Winston Churchill's “The World Crisis” and Julian Corbett's “Naval Operations” . This included the British deciphering of the German naval radio messages, which was achieved with the help of the German signal book ( code book ) recovered from the stranded cruiser Magdeburg by allied Russian divers , the French deciphering of ÜBCHI , an early manual key method of the Imperial Army , and its successors, the ABC and ABCD -Chiffre , also the British deciphering of the Zimmermann dispatch , which was followed by the entry of the USA into the war , and the French deciphering of the ADFGX and ADFGVX cipher , which culminated in the Radiogramme de la Victoire ( German "Funkspruch des Sieges" ).
Since the German military absolutely wanted to avoid a repetition of this cryptographic catastrophe of the First World War , they recognized the new type of machine encryption as the most secure solution. In 1926, the Enigma was first used by the Reichsmarine under the name of " Radio Key C ", two years later by the army on a trial basis and then disappeared from the civilian market. Shortly after the start of series production , Scherbius had a fatal accident in 1929 . In 1934 Rudolf Heimsoeth and Elsbeth Rinke took over ChiMaAG. Under the new company " Heimsoeth & Rinke " (H&R) they continued the development and production of the machine in Berlin. The time of National Socialism had already begun. In the course of arming the Wehrmacht , a reliable encryption system was required, and so nothing stood in the way of the Enigma's success.
It is estimated that around 40,000 machines were made. The Norwegian historian and cryptologist Frode Weierud determined the number of Enigma machines (with plug board ) delivered to the Wehrmacht at 35,636 in 2021. In the course of time up to the end of the war in 1945 and beyond, for example in Korea in 1965 , many different models and variants of the Enigma were used. The most widely used was the Enigma I (read: "Enigma one"), which was used from 1930 by the Reichswehr and later by the Wehrmacht and which embodied the machine key method most frequently used on the German side during the Second World War. On the American side, it was the M-209 (picture) developed by the Swede Boris Hagelin with around 140,000 units .
principle

The Enigma I essentially consists of the keyboard for entering letters, a set of three interchangeable rollers and a light bulb field for display. The set of rollers is the heart of the encryption. The three rollers are arranged side by side so that they can rotate independently. Each of them has 26 electrical contacts on both sides . Each contact is assigned one of the 26 capital letters of the Latin alphabet . In each case a contact on one side of a roller is connected to a contact on the other side of the roller by an insulated wire inside the roller. Overall, different for each roller, all 26 contacts on one side of a roller are electrically connected in pairs and irregularly to the 26 contacts on the other side (see also: wiring table in the following chapter ).
If you press a letter key , electrical current flows from a 4.5-volt battery in the Enigma via the pressed key through the roller set and lights up an indicator lamp. The lit letter corresponds to the encryption of the pressed letter. Since the reels continue to turn with each press of a button, similar to a mechanical odometer , the secret key alphabet changes after each letter.
If you enter "OTTO", the "PQWS" lamps, for example, light up one after the other. It is important and cryptographically strong that each letter is encrypted in a different way due to the rotation of the rollers, in the example the front O from OTTO to P, but the back to S. One speaks of many different (secret) " alphabets ", which are used for encryption and calls this polyalphabetic substitution . In contrast, a monoalphabetic substitution uses only a single secret alphabet , and a plaintext letter is always converted into the same ciphertext letter ("OTTO" for example into "GLLG"). If the reels of the Enigma did not turn, you would only get a simple monoalphabetic encryption.
construction
The Enigma including the wooden case weighs around 12 kg and the external dimensions (L × W × H) are about 340 mm × 280 mm × 150 mm (data without case: 10.35 kg and 310 mm × 255 mm × 130 mm). Its inventor says: "The machine is built very similar to a typewriter and is operated exactly like it."
In contrast to a typewriter, however, the Enigma cipher machine has a set of rollers made up of three rotatable rotors (with a diameter of around 100 mm). To the right of the three rotatable rollers (5) (see numbers highlighted in yellow in the schematic diagram) is the entry roller (4) ( stator ), which does not rotate and its contacts via 26 wires (only four of them are shown here) with the letter keys ( 2) are connected. To the left of the roller set is the reversing roller (6) (VHF), which is also fixed on the Enigma I. The reversing roller (also called: reflector ) is an invention (patented on March 21, 1926) by Willi Korn , an employee of Scherbius. It only has 26 contacts on its right-hand side (only four of them are shown in the sketch), which are connected to one another in pairs. The reversing roller has the effect that the current, which initially passes through the roller set from right to left, is deflected and then flows through it again, now from left to right. The flow leaves the roller set as it came, again via the entry roller.
The table shows the top-secret wiring diagram of the five rotatable rollers I to V available on the Enigma I and the reversing rollers A (used until 1937), B (in use from 1937) and C (1940 and 1941), classified as a “ secret matter of command !” At the time used sporadically):
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z I E K M F L G D Q V Z N T O W Y H X U S P A I B R C J II A J D K S I R U X B L H W T M C Q G Z N P Y F V O E III B D F H J L C P R T X V Z N Y E I W G A K M U S Q O IV E S O V P Z J A Y Q U I R H X L N F T G K D C M W B V V Z B R G I T Y U P S D N H L X A W M J Q O F E C K
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z UKW A E J M Z A L Y X V B W F C R Q U O N T S P I K H G D UKW B Y R U H Q S L D P X N G O K M I E B F Z C W V J A T UKW C F V P J I A O Y E D R Z X W G C T K U Q S B N M H L
A plug board with double-pole sockets for each of the 26 letters is attached to the front of the device . The current from the letter key (2) is passed through this plug board (3) before it reaches the entry roller (4). After running through the set of rollers, it flows a second time over the connector board (7, 8) and finally lights up one of the 26 letter lamps (9). The letter lamps as well as the keyboard and the sockets are arranged similarly to a German typewriter keyboard:
Q W E R T Z U I O A S D F G H J K P Y X C V B N M L
function
If the letter key, for example A, is pressed, the battery current is switched through to the socket of the same name on the plug board via the A key. If socket A is connected to another socket by an externally attached cable (“plugged in”), A is swapped with another letter, for example J. If no cable is plugged in ("not plugged in"), the current goes directly to contact A of the entry roller.
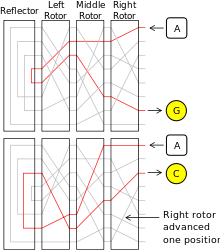
For the further description of the function, reference is made to the figure "Current flow" (initially only upper half). It is used for illustration purposes only and is a simplified representation of the rotating roller set (with left, middle and right rotor) and the static reversing roller (English: Reflector ). For reasons of clarity, the number of letters in the sketch has been reduced from 26 to 8 (only A to H).
Assuming the letter A is not plugged in, the current is passed via the entry roller (it is not shown in the sketch) to input contact A on the right-hand roller. Their wiring causes a substitution (replacement) of the letter by another. The current that enters from the right at input contact A leaves the roller on its left side at output contact B. Thus, A is replaced by B by the right roller.
The current now reaches the middle roller via contact B. Since it is quite possible when wiring a roller that (as in the picture) an input contact is connected to the output contact of the same name, B remains unchanged here. The current leaves the middle roller via contact B and enters the left roller. Their wiring ensures that the current is routed from input contact B to output contact D. The current has now passed through all three (rotatable) rollers once and has reached the reversing roller. It only has contacts on the right side and connects the letters in pairs, for example D with E.
Now the current flows a second time through the set of rollers, but now from left to right. Through the reversing roller, it reaches the left roller via contact E. Here, for example, E is wired to C. As a result, the current continues to flow via contact C into the middle roller, leaves it again via contact F and flows into the right roller. The current finally leaves the right roller at contact G.
The further flow of current is not apparent from the sketch, but is easily explained. After exiting the roller set, the current is fed back to the plug board via the entry roller. If the letter G is plugged into another letter, then a final permutation takes place. If G is not plugged in, lamp G lights up. It only lights up as long as button A is held down, since the changeover contact is only switched to the battery when the button is pressed. If you let go of it, the lamp goes out. In the example shown, the letter A, the key of which was pressed at the beginning and is still pressed, is encrypted as the letter G.
If the text to be encrypted is "AACHENISTGERETTET", an A must be entered again. So button A is released and pressed a second time. It is important that with the mechanical pressure on the button with the help of an indexing mechanism, the right roller is rotated by one position at the same time. The middle roller only rotates after the right roller has taken 26 steps. In the lower half of the picture “Current flow” the situation is sketched after the right roller has rotated one position (downwards).
As can be seen from the sketch, the path for the current entering again at contact A of the right roller has changed radically. It now takes a completely different path than before for the middle and left rollers as well as the reversing roller, although these rollers have not turned. The result is a different encryption of the letter A, which is now converted to C.
service
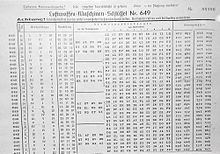
The Enigma I initially had three, and from 1939 five different rollers, which were numbered consecutively with Roman numerals (I, II, III, IV and V). The user selected three of the five rollers according to a secret key table, which provided for changing settings for each day, and used them according to the arrangement prescribed in the daily key under the heading "Roller position".
The " key table" presented the valid daily keys for a full month, which were changed at midnight (exceptions: in the case of the Luftwaffe , the change took place at 3 o'clock in the morning. For the Navy, see Enigma-M4 ). Only three days of the month are shown below as an example, whereby, as was common at the time, the days are sorted in descending order. This allows the encryptor to cut off and destroy the codes that have been used up in the past few days.
Example for the 29th of the month: Roller position I IV III means that roller I on the left (as a slow rotor), roller IV in the middle and roller III on the right (as a fast rotor). (With a few exceptions, the VHF B was always used as the reversing roller.) The rings, which are attached to the outside of the roller body and determine the offset between the internal wiring of the rollers and the letter to which the transfer to the next roller takes place, are on the Set the 16th, 26th and 8th letters of the alphabet, i.e. P, Z and H.
Tag Walzenlage Ringstellung ---- Steckerverbindungen ---- 31 III I IV 01 17 22 AH BL CX DI ER FK GU NP OQ TY 30 II V I 18 24 11 BN DZ EP FX GT HW IY OU QV RS 29 I IV III 16 26 08 AD CN ET FL GI JV KZ PU QY WX
The ring position was often (as here) listed numerically and not alphabetically, presumably to avoid confusion with the other partial keys. As an aid for the operator “to convert the numbers into letters or vice versa”, a conversion table is attached to the inside of the Enigma's housing cover as part of the label “Please note!”.
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 01 02 03 04 05 06 07 08 09 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26
Finally, the double-pole sockets on the front panel must be wired with corresponding double-pole cables. As a rule, exactly ten cables were plugged in. The upper socket of each socket pair has a slightly larger diameter (4 mm) than the lower one (3 mm), so that the plugs can only be inserted in one orientation. In this way, the desired electrical crossover and thus the swapping of the two letters was achieved. Six letters were left unplugged. (This rule of the six self-steckered letters helped the code breakers .)
In order to reduce the risk of guessing the keys, the German authorities have invented some rules for drawing up the key tables. It was (temporarily) forbidden for a roller position that was already in use on one day of the month to be repeated on another day of the month. (The British recognized this and called it the non-repeating rule .) Also, a roller was not allowed to be in the same place in the roller set on two consecutive days of the month ( non-clashing rule ). A third rule should prevent guessing of obvious plug combinations. It was forbidden for two letters in the alphabet to be plugged together. (The British Codebreakers also used this to their advantage and called it Consecutive Connector Knock-Out CSKO .)
All these regulations have the opposite effect, namely a weakening of the encryption. They made work easier for the code breakers, who, due to the rules mentioned, were able to exclude more and more key combinations, especially as a month progressed.
After inserting the three rollers and adjusting the rings as well as plugging in the ten plug connections according to the key panel, the operator closed the flap above the set of rollers and the front flap. The latter brought about a firm pressure on the connector and a secure contact as well as protection against spying on the key. The Enigma was then ready for encryption or decryption, provided that the user turned the three (rotating) rollers into the correct starting position.
Radio message

In order to ensure that not all radio messages in a key network are encrypted with identical keys, which would make the texts vulnerable, it was prescribed to set an individual starting position of the three reels for each message, known as the "saying key ". The procedures for this changed from time to time and were not the same for all parts of the Wehrmacht . In army and air force was from May 1, 1940 (nine days before the start of the campaign in the west ) the following in the "key guide to Enigma machine" described scheme, for example, the following plain text is to be transmitted:
“The Wehrmacht High Command announces: Aachen has been saved. The threat could be averted by the bundled deployment of the aid workers and the rescue of the city ensured at around 6:00 p.m. "
Since the Enigma can only encrypt capital letters and no digits or punctuation marks and also does not recognize spaces , the plain text shown above must first be prepared accordingly before encryption. Punctuation marks are replaced by "X", proper names are doubled and enclosed in "X" and numbers are written out digit by digit. It was also common to replace the “ch” and “ck” with “Q” (except for proper names) and then to divide the text into groups of five. This gives you the following plain text prepared for encryption:
DASOB ERKOM MANDO DERWE HRMAQ TGIBT BEKAN NTXAA CHENX AACHE NXIST GERET TETXD URQGE BUEND ELTEN EINSA TZDER HILFS KRAEF TEKON NTEDI EBEDR OHUNG ABGEW ENDET UNDDI ERETT UNGDE RSTAD TGEGE NXEIN SXAQT XNULL XNULL XUHRS IQERG ESTEL LTWER DENX
The encryptor has set his Enigma I, as described above, to the day key, for example for the 29th of the month. (Roller position B I IV III, ring position 16 26 08 and plug connections AD CN ET FL GI JV KZ PU QY WX. Both this and the steps described below can be realistically reproduced using freely available computer simulations , see also: Enigma simulations and simulations under Web links .) The operator now thinks of a random basic position, for example "QWE", and sets the three rollers so that exactly these three letters are visible in the display windows. Now he comes up with a random key with three letters, for example "RTZ". He encrypts this with his Enigma and watches how the "EWG" lamps light up one after the other. He openly informs the recipient of the message key encrypted in this way, along with the randomly selected basic position as an indicator, as well as the time and the number of letters in the text as the “message head”.
According to the then applicable H.Dv. G. 14 (= Army Service Regulations, secret, No. 14), the message header contains the time as a four-digit number, the number of letters of the message including the five letters of the identification group as well as the selected basic position and the encrypted message key (example: 2220 - 204 - qweewg). In general, all the letters were handwritten in small letters , as they could be listed as faster than use of capital letters . An authentic slogan form with the slogan "kr - 2300 - 182 - zzxprq -", where "kr" (abbreviation for "war important" or "war emergency report" with the conspicuous Morse code - · - · - · ) stands as a symbol for "urgent", can be seen under web links as "Spruch Nr. 233". It concerns a request for ammunition for the heavy field howitzer (sFH).

Next, the operator selects three code group letters that are valid for this day using a code group table, for example “NOW”. The identification group has no cryptological meaning, it only serves the recipient of the message to recognize that the message is really intended for him and that it can also be decrypted with authorization. To disguise the identification group, the three letters are freely permuted by the sender and supplemented by two “ filler letters ”, for example “XY”, which can be randomly changed for each saying . “NOW” first becomes “OWN” and finally “XYOWN”. These five letters are placed in front of the ciphertext in unencrypted form as the first group of five.
The encryptor now sets the three reels of his Enigma to the phrase "RTZ" chosen by him and encrypts the above plain text, that is, he enters every single letter of the plain text via the Enigma's keyboard and reads the light that lights up as ciphertext letters and write it down. Together with the message head and the camouflaged identification group, the following radio message results:
Kopf: 2220 – 204 – QWE EWG -
XYOWN LJPQH SVDWC LYXZQ FXHIU VWDJO BJNZX RCWEO TVNJC IONTF QNSXW ISXKH JDAGD JVAKU KVMJA JHSZQ QJHZO IAVZO WMSCK ASRDN XKKSR FHCXC MPJGX YIJCC KISYY SHETX VVOVD QLZYT NJXNU WKZRX UJFXM BDIBR VMJKR HTCUJ QPTEE IYNYN JBEAQ JCLMU ODFWM ARQCF OBWN

The header and ciphertext are broadcast as Morse code and recorded by the recipient. This first checks whether the number of letters (here: 204) is correct and the message was received without mutilation . Then he looks at the identification group, i.e. the first group of five, ignores the first two letters and sees "OWN". He sorts the three letters in alphabetical order, receives "NOW", looks in his identification group table, discovers these identification group letters there and can now be sure that the saying is intended for him and that he can decipher it. His Enigma is already set identical to that of the sender in terms of roller position, ring position and plug connections in accordance with the day code he is familiar with. He still lacks the spell key, i.e. the correct starting position of the reels to decipher the spell. He receives this information from the indicator "QWE EWG" in the message head, which he interprets as follows: Set the rollers to the basic position "QWE" and then press "EWG". Now he can observe how the "RTZ" lamps light up on his Enigma one after the other. This is the key to be set.
He now turns the reels to the starting position “RTZ” and begins to enter the ciphertext, starting with the second group of five “LJPQH”, into his Enigma. The lamps will now light up one after the other and the following text will appear
dasoberkommandoderwehrmaqtgibtbekanntxaachenxaache nxistgerettetxdurqgebuendelteneinsatzderhilfskraef tekonntediebedrohungabgewendetunddierettungderstad tgegenxeinsxaqtxnullxnullxuhrsiqergestelltwerdenx
Cryptographic strengths

When Scherbius applied for a patent for the Enigma in 1918, i.e. during the First World War, it was an extremely strong cryptographically machine and could rightly be called " unbreakable ". In contrast to the manual encryption methods ( e.g. ADFGVX ) that were still in use at the time , the introduction of machine encryption was innovative . It was unassailable through the manual, mainly linguistically supported, deciphering methods that were customary at the time and remained so until the 1930s, i.e. for more than ten years.
During this time, the then newly established cross- armed forces cryptographic office ( Dutch Cryptographic Bureau ) of the Dutch armed forces received an Enigma-D (picture) from Chiffriermaschinen AG for viewing and testing. After two months of analysis, the head of the office, Captain Henri Koot , gave the following assessment:
“I dare say that it satisfies all requirements, be they ever so high even the possession of an equal machine with the same electrical connections both in the ciphering cylinders and in the other parts of the machine will not enable an unauthorized person to find out its solution. "
“I dare say that it meets all requirements, no matter how high. Even having an equivalent machine with the same electrical connections both in the encryption cylinders and in the other parts of the machine will not enable an unauthorized person to find a solution. "
The cryptographic strengths of the Enigma are essentially given by the rotating set of rollers. By rotating the rollers it is achieved that each letter of the text is encrypted with a new alphabet (polyalphabetic encryption). In this way, the frequency range , which is so treacherous in the monoalphabetic method, is ground down beyond recognition and classic attacks to decipher the ciphertext, such as statistical analyzes , Doppler or pattern searches , are doomed to failure. The period search using the coincidence index , as a common method of attacking polyalphabetic encryption, such as the Vigenère cipher , is also futile, because compared to the period length (of 16,900, see also: improvement potential ) of the Enigma, a comparatively tiny maximum length of the radio messages of 250 Prescribed letters.

Decisive for the security of the encryption against unauthorized decipherment are the secrecy of the roller wiring and the number of rollers used in the roller set. The latter is an important factor that explains the much stronger encryption of the four-roller Enigma-M4 used in the German submarines compared to the Enigma I (with only three rollers). Three radio messages encrypted with an M4 machine are known to the public, the content of which could not be deciphered until 2006. Only then did the amateur cryptologists Stefan Krah, two of the news that the submarine U 264 or U 623 were sparked in 1942 by distributed computing ( distributed computing ) and merger of several thousand computers on the Internet within one month decipher. The third radio message lasted a further seven years and was only deciphered in January 2013. This impressively shows that the Enigma, which was patented for the hundredth time on February 23, 2018, is not easy to crack even with modern cryptanalytic attack methods and today's advanced computer technology , but is still a "tough nut".
The rings (ring position), originally invented in 1928 by Willi Korn, and not, as has often been wrongly published, by his colleague Paul Bernstein , determine the offset between the internal wiring of the rollers and the letter that is transferred to the next roller . They were also used to protect against espionage . This prevented that the internal rotational position of the rollers could be inferred by reading the externally visible roller position.
With the help of the “double connector cords”, which can be plugged into the connector board from the front, letters can be swapped involutorily in pairs before and after passing through the set of rollers . This measure served to further strengthen the cryptographic security of the Enigma. In fact, this considerably expands the key space.
Key room


The size of the Enigma's key space can be calculated from the four individual partial keys and the number of different key settings that are possible in each case. The entire key space of the Enigma I (for M4 see Enigma-M4 ) results from the following four factors:
- a) The roller position
- Three out of five reels (I through V) are selected. (The VHF B was almost always used as the reversing roller.) This results in 5 · 4 · 3 = 60 possible roller positions (corresponds to a " key length " of around 6 bits ).
- b) The ring position
- There are 26 different ring positions (01 to 26) for the middle and right roller. The ring of the left roller does not contribute to the enlargement of the key space, since its transfer notch does not cause an advancement of a roller further to the left. A total of 26² = 676 ring positions are relevant (corresponds to approximately 9 bits).
- c) The roller position
- There are 26 options for setting each of the three (rotating) rollers (A to Z). The reverse roller cannot be adjusted. A total of 26³ = 17,576 roller positions are available. If the ring position is assumed to be known, then 26² = 676 initial positions are to be eliminated as cryptographically redundant due to an unimportant anomaly in the indexing mechanism . What remains as relevant is 26 · 25 · 26 = 16,900 roller positions (corresponds to approximately 14 bits).
- d) The plug connections
- Up to 13 plug connections can be made between the 26 letters. Based on the case of the unplugged connector board (taken into account as number 0 in the table below), there are 26 options for the first connector for one end and then 25 for the other end of the cable. There are thus different possibilities for the first cable 26 · 25 to plug it in. However, since it does not matter in which order the two cable ends are plugged, half of the options are omitted. This leaves 26 · 25/2 = 325 possibilities for the first connection. For the second one receives analogously 24 · 23/2 = 276 possibilities. In general there are (26−2 n +2) · (26−2 n +1) / 2 possibilities for the n th plug connection (see also: Gaussian formula ).
Nummer der ---- Möglichkeiten für ---- Möglichkeiten für Steckverbindung erste Seite zweite Seite Steckverbindung 0 1 1 1 1 26 25 325 2 24 23 276 3 22 21 231 4 20 19 190 5 18 17 153 6 16 15 120 7 14 13 91 8 12 11 66 9 10 9 45 10 8 7 28 11 6 5 15 12 4 3 6 13 2 1 1
- The total number of possible plug combinations when using several plugs results from the product of the possibilities for the individual plug connections. However, since the order in which it is carried out does not matter here either (it is cryptographically equivalent if, for example, A is plugged in with X first and then B with Y or vice versa, first B with Y and then A with X), the corresponding cases are not allowed as key combinations must be taken into account. With two plug connections, this is exactly half the time. The previously determined product has to be divided by 2. With three plug connections there are six possible sequences for performing the connections, all six of which are cryptographically equivalent. The product has to be divided by 6. In the general case, with n plug connections, the product of the previously determined possibilities is given by n ! ( Factorial ) to divide. The number of possibilities for exactly n plug connections results as
Stecker -------------- Möglichkeiten für ----------------
n Steckver- genau n Steck- bis zu n Steck–
bindung verbindungen verbindungen
0 1 1 1
1 325 325 326
2 276 44850 45176
3 231 3453450 3498626
4 190 164038875 167537501
5 153 5019589575 5187127076
6 120 100391791500 105578918576
7 91 1305093289500 1410672208076
8 66 10767019638375 12177691846451
9 45 53835098191875 66012790038326
10 28 150738274937250 216751064975576
11 15 205552193096250 422303258071826
12 6 102776096548125 525079354619951
13 1 7905853580625 532985208200576
- After only six and later between five and eight connection cables were plugged in in the first few years, from August 1939 the fixed rule applied to always make exactly ten plug connections. According to the table above, there are 150,738,274,937,250 (more than 150 trillion) plug-in options (corresponds to about 47 bits) for these.
The entire key space of an Enigma I with three from a supply of five selected rollers and one reversing roller and when using ten plugs can be calculated from the product of the 60 roller positions, 676 ring positions, 16,900 roller positions and 150,738 determined in sections a) to d) above .274.937.250 calculate connector options. He is:
60 676 16,900 150,738,274,937,250 = 103,325,660,891,587,134,000,000
That is about 10²³ possibilities and corresponds to a key length of about 76 bits. The occasional "150 million million million" combinations, for example in the films " Enigma - The Secret " and " The Imitation Game - A Top Secret Life ", are based on the omission of the ring positions. The exact calculation in this case results in 60 · 16,900 · 150,738,274,937,250 or 152,848,610,786,371,500,000 different cases, with the British mostly taking into account all 26³ or 17,576 possible roller positions instead of 16,900 and the product then being 158,962,555,217,826,360. 000 received.
The key room was enormous for the time and even stands up to a comparison with more modern processes. For example, the DES ( Data Encryption Standard ) encryption method , which has become the standard for several decades towards the end of the 20th century, has a key length of exactly 56 bits, which is significantly less than the Enigma. An Exhaustion (full browsing) the key area of the Enigma itself is hardly possible with modern means and was completely illusory with the former technology.
However, the size of the key space is only a necessary but not a sufficient condition for the security of a cryptographic method. Even a method as simple as simple monoalphabetic substitution has 26 (when using an alphabet of 26 letters like Enigma)! ( Faculty ) possible keys. That is roughly 4000 x 10²³ keys (approx. 88 bits) and compared to the number 10²³ of the Enigma I is even bigger by a factor of about 4000. However, a monoalphabetic substitution is very insecure and can be broken (deciphered) easily.

In the case of the Enigma, too, the structural component that significantly contributes to the size of the key space, namely the plug board, is similar to a simple monoalphabetic substitution, because the plug ultimately remains unchanged during the entire encryption process. The plug board can consequently be overcome and practically completely eliminated with the help of an intelligent cryptanalytic attack method ( Turing bomb ). This means that the factor 150,738,274,937,250 can effectively be deleted again when calculating the key area.
The rings also only slightly strengthen the cryptographic method. If the ring on the right cylinder is incorrectly positioned and the key is otherwise correct, plain text passages can be read periodically (period length = 26 letters), which are repeatedly torn off after a few letters. The ring of the middle roller is even less effective, the period length here being 650 letters (25 x 26). The middle ring position therefore usually does not contribute to the size of the key area at all, namely whenever there is no transfer to the left cylinder during the spell , which only rarely happened due to the prescribed spell length of at most 250 letters. The ring position of the left cylinder is completely meaningless from a cryptanalytic point of view. Overall, fine adjustment of the rings is no longer a major problem. This means that when calculating the size of the key space, the factor 676 can also be safely deleted.
Only the 60 roller positions and the 17,576 roller positions to be taken into account (if the ring position is unknown) remain cryptographically effective. So shrinks before that so gigantic appearing key space at a comparatively tiny 60 x 17,576 = 1,054,560 (about one million) options (such as 20 bits), a number that already at that using the times of World War II electromechanical equipment exhaustively (exhaustively ) could be processed.
Cryptographic weaknesses

Scherbius' colleague Willi Korn achieved through the reversing roller that the key procedure becomes involutorial , i.e. if a U is encoded into an X in a certain position of the rollers, then an X is also encoded into a U in this position. In this way, he simplified the operation and construction of the machine, because you no longer have to differentiate between encryption and decryption. In addition, he hoped for an increase in safety, because the current now flows through the rollers twice:
“This decline in the current through the cipher roller set causes further scrambling. As a result of this arrangement, it is possible to get by with relatively few encryption rollers and still maintain a high level of encryption security. "
With these words Korn explains the advantages of his reversing roller in the patent specification (DRP No. 452 194). However, this was a fallacy with far-reaching consequences.
On the one hand, the reversing roller has the effect that no more letters can be encoded in itself, because the current cannot in any case take the exact route back through the set of rollers that it came from. It is always returned on a different path than when it flowed to the reversing roller. Mathematically, one speaks here of fixed-point-free permutations . This restriction may appear to be an insignificant minor, because there are still 25 more letters of the alphabet for encryption, but in fact this means a drastic reduction in the alphabets available for encryption and, moreover, a new vulnerability of the ciphertext. On the other hand, the reverse roller causes the permutation and thus the encryption to become involutorial, a further reduction in the number of alphabets.
The cryptographic weaknesses introduced by the reversing cylinder, in particular the reduction in the number of available alphabets, can easily be made clear if, for example, instead of 26 letters, one simply starts with only four letters. With four letters you can get 4! = Generate 24 different alphabets (by which the cryptographer means different arrangements of letters), namely
ABCD ABDC ACBD ACDB ADBC ADCB BACD BADC BCAD BCDA BDAC BDCA CABD CADB CBAD CBDA CDAB CDBA DABC DACB DBAC DBCA DCAB DCBA
If you limit yourself to only the fixed-point-free permutations instead of all 24 possible, then all alphabets in which a letter is encoded in itself, i.e. in its usual alphabetical place, are omitted. The following fifteen alphabets are to be deleted from the list above, as they have one or more fixed points (below red and underlined).
ABCD ABDC ACBD ACDB ADBC ADCB BACD BCAD BDCA CABD CBAD CBDA DACB DBAC DBCA |
Only the following nine fixed-point-free permutations remain:
---- ---- ---- ---- ---- ---- ---- BADC ---- BCDA BDAC ---- ---- CADB ---- ---- CDAB CDBA DABC ---- ---- ---- DCAB DCBA
If one now takes into account that the reversing cylinder not only eliminates all permutations with fixed points, but also all non-involutive permutations, then six more cases must be deleted from the table above, namely those in which the double application of the permutation does not return to the original letter leads. Of all the possible 24 permutations of a four-letter alphabet, only the three fixed-point-free and involutor cases remain . They are referred to as " truly involutive permutations ".
---- ---- ---- ---- ---- ---- ---- BADC ---- ---- ---- ---- ---- ---- ---- ---- CDAB ---- ---- ---- ---- ---- ---- DCBA

In the case of the Enigma with its 26 letters, this restriction means that instead of the 26! ( Factorial ), i.e. about 4 · 10 26 total possible permuted alphabets only the 25 · 23 · 21 · 19 · 7 · 5 · 3 · 1 = 25 !! ( Double faculty ), i.e. about 8 · 10 12 genuinely involutorically permuted alphabets can be used. The reversing roller wastes a factor of about 5 · 10 13 in possibilities - a gigantic weakening of the combinatorial complexity of the machine. What remains is less than the square root of the originally possible permutations.
Cryptographically even more catastrophic than this drastic reduction in the number of alphabets, however, is that by avoiding fixed points, statements about the text such as "Nothing is ever itself" are possible, which were a very important aid in deciphering. If the attacker knows that a letter is never the encryption of himself, then this knowledge opens up abbreviations for him and he no longer has to laboriously work through each individual case, as the following example illustrates.
A deciphering method that has been known and proven for centuries is the “ method of the probable word ”. The attacker guesses, suspects or knows that a certain phrase ( English Crib , French Mot probable ) appears in the text , for example "OBERKOMMANDODERWEHRMACHT". If, for example, the attacker has a ciphertext fragment encrypted with the Enigma like the following, he can easily determine where in the text the presumed probable word can not be by checking for every possible position whether there is a character in it itself would be encrypted, which, as he knows from the Enigma, is impossible. For this he writes the likely word in the various layers below the ciphertext and checks for collisions ( English Crash ) that are red in the example highlighted and underlined:
BHNCXSEQKOBIIODWFBTZGCYEHQQJEWOYNBDXHQBALHTSSDPWGW 1 OBERKOMMANDODERWEHRMACHT 2 OBERKOMMANDODERWEHRMACHT 3 OBERKOMMANDODERWEHRMACHT 4 OBERKOMMANDODERWEHRMACHT 5 OBERKOMMANDODERWEHRMACHT 6 OBERKOMMANDODERWEHRMACHT 7 OBERKOMMANDODERWEHRMACHT 8 OBERKOMMANDODERWEHRMACHT 9 OBERKOMMANDODERWEHRMACHT 10 OBERKOMMANDODERWEHRMACHT 11 OBERKOMMANDODERWEHRMACHT 12 OBERKOMMANDODERWEHRMACHT 13 OBERKOMMANDODERWEHRMACHT 14 OBERKOMMANDODERWEHRMACHT 15 OBERKOMMANDODERWEHRMACHT 16 OBERKOMMANDODERWEHRMACHT 17 OBERKOMMANDODERWEHRMACHT 18 OBERKOMMANDODERWEHRMACHT 19 OBERKOMMANDODERWEHRMACHT 20 OBERKOMMANDODERWEHRMACHT 21 OBERKOMMANDODERWEHRMACHT 22 OBERKOMMANDODERWEHRMACHT 23 OBERKOMMANDODERWEHRMACHT 24 OBERKOMMANDODERWEHRMACHT 25 OBERKOMMANDODERWEHRMACHT 26 OBERKOMMANDODERWEHRMACHT 27 OBERKOMMANDODERWEHRMACHT BHNCXSEQKOBIIODWFBTZGCYEHQQJEWOYNBDXHQBALHTSSDPWGW |
The number of layers to be excluded by collisions can be estimated according to the following consideration: With a probable word of length 1 (i.e. only a single probable letter) the probability of a collision is 1/26. Hence the probability of no collision is 1−1 / 26. For a probable word as above with length 24, the probability of no collision (1−1 / 26) is 24 , which is around 39%. This means that in the case of 27 examined locations, no collisions are expected on average for 27 · (1−1 / 26) 24 of the cases. The expression yields about 10.5 and agrees quite well with the eight collision-free crib layers observed in the example (and marked in green).
With the help of this extremely simple cryptanalytic attack method, 19 of the 27 possible positions of the probable word here, i.e. more than two thirds, can be eliminated as impossible - a considerable simplification of work for the attacker.
Decipherment


The operators of the Enigma key machine were of the opinion that, in contrast to almost everything that was in use until 1918, the texts they machine-encrypted could not be cracked using manual methods. It was overlooked that machine encryption can be countered by machine deciphering.
The history of the Enigma's decipherment begins in 1932 when the German Hans-Thilo Schmidt, spying for France under the code name HE ( Asché ) , kept secret keyboards for the months of September and October 1932 as well as the instructions for use ( H.Dv. g. 13) and the key instructions (H.Dv.g.14) to the French secret service employee Capitaine (German: captain ) and later Général Gustave Bertrand betrayed for money . At that time, only three rollers (I to III) were in use and the roller position was only changed every quarter and not yet, as was the case from October 1936, on a daily basis. The Deuxième Bureau of the French secret service forwarded the documents to British and Polish authorities.
While it failed French and the British, in the encryption break and they classified the Enigma as "unbreakable," the 27-year-old Polish mathematicians succeeded Marian Rejewski in his work in the charge of Germany Unit BS4 of Biuro Szyfrów (German: "Cipher Bureau" ) the first break into the Enigma in 1932. He used a legally purchased commercial machine (presumably model C ) in which - unlike the military Enigma I, which was still unknown to him - the keyboard was connected to the entry roller in the usual QWERTZ order (sequence of letters on a German keyboard , starting at the top left) was. Rejewski guessed the wiring sequence chosen by the Germans for the military variant, which in 1939 almost drove the British codebreaker Dillwyn "Dilly" Knox to despair. Then, with the help of his excellent knowledge of permutation theory (see also: Enigma equation ), Marian Rejewski managed to understand the wiring of the three rollers (I to III) and the reversing roller (A) (see also: Enigma rollers ) - a cryptanalytic masterpiece that made him the words of the American historian David Kahn "in the pantheon of the greatest cryptanalysts of all time rises" (in the original: "[...] elevates him to the pantheon of the greatest cryptanalysts of all time"). The British code breaker Irving J. Good designated Rejewskis performance as "The theorem did won World War II" (German: "The theorem that won World War II").
The next task that had to be solved was to find the right roll position and roll position. To do this, Rejewski, together with his colleagues Jerzy Różycki and Henryk Zygalski , who joined them in 1932, exploited a serious procedural error that the Germans made: In order to ensure a secure transmission, at that time the motto key was placed twice in a row and written in encrypted form at the beginning of a message ( " Slogan key duplication "). Thus the first and fourth, the second and fifth as well as the third and sixth ciphertext letters were each assigned to the same plaintext letter. With the help of two machines specially built for this purpose by their colleague Antoni Palluth from AVA , called Zyklometer and Bomba , which embodied two or three times two Enigma machines connected in series and each shifted by three rotational positions, the Polish cryptanalysts were able to work for each of the six possible Determine the roller positions at which roller positions the observed assignment of the letter pairs was possible and thus narrow the search space considerably . After analyzing several radio messages, the correct message key was found.
After the Germans, who knew nothing about all of this, changed their process technology on September 15, 1938 and three months later with the introduction of rollers IV and V, the number of possible roller layers from six (= 3 · 2 · 1) to sixty (= 5 · 4 · 3) increased, the Poles could no longer keep up and the Enigma was safe again. In view of the impending danger, shortly before the German invasion of Poland , they handed over all of their knowledge to their allies. On July 26 and 27, 1939, the legendary secret meeting of French, British and Polish code breakers took place in the Kabaty Forest of Pyry , just under 20 km south of Warsaw, where they presented their Enigma replicas and their cryptanalytic machines to the astonished British and French and revealed their methodologies . The first question that Dilly Knox asked at this meeting (according to Mavis Batey in French ) was: "Quel est le QWERTZU ?" (German: "What is the QWERTZU?" ? "). This had tormented him for a long time. Rejewski's answer was ingeniously simple: "ABCDEFG ...". A thought that Knox found so absurd that he couldn't believe it. Marian Rejewski, on the other hand, knew the “virtue of the Germans: the sense of order”, and this had already made him recognize the simplest of all permutations chosen by German cryptographers seven years earlier - the trivial case of identity . This resulted in the usual alphabetical order of the wiring of the entry roller, which he could easily guess.



With this boost, especially with the roller wiring that was finally known, the British cryptanalysts were able to launch another attack on the Enigma when the war broke out in Bletchley Park (BP), about 70 km north-west of London . Was the most important tool - in addition to their intellectual capacity and the high number of personnel of later ten thousand to fourteen thousand women and men - especially a special electromechanical machine called the bombe , which as a successor to the Polish Bomba built and the English mathematician Alan Turing was conceived. Turing's idea for the key search was to completely strip off the effect of the connector board by linking several, usually twelve, sets of Enigma rollers in a ring. This enabled him to drastically reduce the practically unmanageable number of more than 200 trillion encryption options on which German cryptographers were placing their hopes.
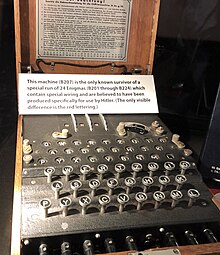
The basic principle is based on the Enigma I, in which three rollers from an assortment of five rollers are used and only the reversing roller B is available. Another reversing cylinder ( VHF C ), called Uncle Walter onomatopoeically by the British , appeared briefly and quickly disappeared again. For each of the 60 different roller layers there are 26³, i.e. 17,576 roller positions. If, when looking for the key, one can disregard the ring positions and the plug board, what was made possible with the help of the cryptanalytic attack method implemented by the bomb , then “only” 60 · 17,576, ie 1,054,560 possibilities remain. These approximately one million different cases are practically impossible to try out by hand in a reasonable amount of time. With the help of the Turing bomb, however, which was motorized at 64 revolutions per minute and could process 26 cases during each revolution, it only took 1,054,560 / (26 · 64) minutes, i.e. a little more than ten hours, to test all the options. In addition, there is the time to set and retool the machine for the sixty different roller positions, which doubles the time to around twenty hours. If you make the effort to use sixty bombs , one for each roller position, the time for a run of a little more than ten hours is reduced to a good ten minutes - a tolerable time. In fact, there were more than 330 bombs in operation in the United Kingdom and the United States in early 1944 , after the British had to make do with just twelve bombs in late 1941 .
The probable words ( cribs ) that can be expected to appear in the text are of decisive importance for the function of the bomb . If these are missing, the deciphering fails. For example, the British managed to break into two key sections of the Deutsche Reichsbahn not, at Bletchley Park after the early steam locomotive Rocket as Rocket II and Rocket III were known. The reason, as they discovered to their surprise after the war, was not a particularly safe Enigma variant, but the unfamiliar railway workers' language and the type of transport reports that did not allow them to guess likely words. Military reports, on the other hand, were often stereotyped and contained many easy-to-guess cribs such as OBERKOMMANDERWEHRMACHT, which the British code breakers could use for deciphering.
In addition, they benefited from the German thoroughness in the preparation of routine reports, such as weather reports, which were sent punctually every morning at the same time and from the same place. The German regulation “General key rules for the Wehrmacht” (H.Dv.g.7) expressly forbade “regularities in the structure, identical expressions and repetitions in the text” and warned urgently “It must be avoided in any case that by fleetingly trained Personnel key mistakes are made that [...] enable enemy intelligence to decipher, ”but precisely these mistakes happened that the code breakers were able to perceive and exploit. From the British point of view, a daily freshly encrypted Enigma message, which always began with the words “WETTERVORHERSAGEBEREICHSIEBEN”, was just as valuable as a direct public disclosure of the currently valid daily key would have been. For example, the Enigma key from D-Day , the day the Allies landed in Normandy ( Operation Overlord ), was saved in less than two by the crib “ WEATHER FORECAST BISKAYA ”, which the British cryptanalysts could easily guess and correctly guessed Broken hours after midnight.
Not infrequently, the British even deliberately provoked incidents just to receive the expected German radio messages with known content (and encrypted with the current day key), and called this technology gardening (German: "gardening"). The British code breaker Rolf Noskwith from Barrack 8 described it as follows: “The RAF dropped mines at certain points in the North Sea, so that the German mine warning served us as a crib. The digits were carefully chosen to avoid certain digits, such as 0 and 5 in particular, [as coordinates ] for which the Germans used different letters. ”The British were able to avoid the distinction between“ NULL ”and“ NUL ”. as well as "FUENF" and "FUNF", which make work a little easier. Except in the case of “ZWEI” and “ ZWO ”, there was only one spelling for the remaining digits. Deciphered messages from smaller naval units, such as harbor ships, which did not have the Enigma and instead used manual key procedures ( shipyard keys or reserve manual procedures ), served the British as cribs when the Enigma broke. The Germans sent many radio messages, such as mine warnings, verbatim both as Enigma ciphertexts and encrypted using the manual method. The British were grateful for these “ ciphertext-ciphertext compromises ” and called them Kisses .


Under the code name “ Ultra ”, it was possible, beginning in January 1940, to break the messages encrypted by the Luftwaffe and later also by the army with the Enigma I for almost the entire duration of World War II. In 1943, for example, more than 80,000 radio messages were intercepted and deciphered per month , an average of more than 2500 every day; during the war it was over two and a half million.
The encryption methods of the German Navy , which used a variant ( Enigma-M3 ) with three out of eight rollers (I to VIII) and a sophisticated spell key agreement , were more persistent . The British only managed to break in here in May 1941 after the capture of the German submarine U 110 and the capture of an intact M3 machine and all secret documents ( code books including the crucial " double-letter exchange boards ") by the British destroyer HMS Bulldog on May 9, 1941 There was a painful interruption ( black-out ) for the British when on February 1, 1942 the M3 (with three rollers) was replaced by the M4 (with four rollers) in the submarines. This procedure, called “ Schlüsselnetz Triton ” by the Germans and Shark (German: “ Hai ”) by the British , could not be broken for ten months, a time that the submariners called the “ second happy time ” the German submarine weapon was again able to record great successes. The break-in in Shark only succeeded on December 12, 1942, after the British destroyer HMS Petard landed the German submarine U 559 in the Mediterranean on October 30, 1942 . A boarding party consisting of Lieutenant Tony Fasson (1913-1942), Able Seaman Colin Grazier (1920-1942) and the young Tommy Brown (1926-1945), boarded the boat and captured important top-secret key documents, such as short signal stitching and weather short-key , with whose help the cryptanalysts in Bletchley Park managed to overcome the Enigma-M4 as well.

Now the Americans also came to the rescue. Under the leadership of Joseph Desch they produced from April 1943 at the United States Naval Computing Machine Laboratory (NCML) , which is based in the National Cash Register Company (NCR) in Dayton ( Ohio had), more than 120 pieces high-speed variants of the bombe . These so-called Desch bombs were specifically aimed at the M4. In quick succession, other American authorities were added to provide support, such as the Signal Security Agency (SSA) and the United States Coast Guard Unit 387 (USCG Unit 387) . The workforce grew quickly from a few hundred to more than ten thousand employees who deciphered thousands of radio messages every day.
After that, the German submarines were never safe (see also: U-boat war ). Was a direct result of the American decipherments starting with U 463 on May 16, 1943 a U-tankers from Type XIV ( "cow") until U 220 on 28 October 1943 a body set up to supply mine-laying by type XB , the sinking eleven of the eighteen German supply submarines within a few months in 1943. This led to a weakening of all Atlantic U-boats that could not be supplied at sea now, but to the long and perilous journey home through the Bay of Biscay to had to enter the submarine bases on the French west coast.
Historical consequences

It is undisputed that the compromise of the Enigma was of enormous strategic importance for the course of the Second World War. Some historians assume that if the Enigma hadn't been broken, the outcome of the war would not have changed, but it would have lasted much longer and would have been far more bloody. The English historian Sir Harry Hinsley , who had worked in Bletchley Park , commented on the meaning of ultra with the words “shortened the war by not less than two years and probably by four years” ( German: “[ Ultra ] shortened the war not less than two years and probably by four years ” ). The assumption seems justified that it is thanks to the Polish, British and American cryptanalysts and their work in deciphering the German machine that the Second World War could be shortened considerably and the lives of countless people on all sides were saved.
But there are also historians, politicians and the military who regard the intelligence services as “decisive” for the victory of the Allies. For example, the American historian Harold Deutsch , who was Head of Analysis at the Office for Strategic Services in the United States War Department , the OSS , said:
"I feel that intelligence was a vital factor in the Allied victory - I think that without it we might not have won, after all."
"I believe that intelligence was a vital factor in the Allies' victory - I mean that without them we wouldn't have won after all."
Experts who share Deutsch's view take into account the fact that the decipherments were of great help not only on a military-tactical level (army, air force and navy), but also because of the almost complete penetration of German communications at all levels (police, secret services, diplomatic services, SD, SS, Reichspost, Reichsbahn and Wehrmacht) also allowed an extremely precise insight into the strategic and economic planning of the German leadership. The Allies particularly valued the authenticity of the information obtained from Enigma radio messages, which was not always available from other sources such as reconnaissance , espionage or betrayal . In this way, the British were able to coordinate their resources , which were still very limited at the beginning of the war, much better and use them in a much more targeted manner against the recognized German weaknesses than would have been possible without the deciphering of the Enigma. In the later course of the war, together with their American allies, they used the ultra information to better exploit their mutual superiority.
One of the leading former codebreakers from Bletchley Park, the British chess master Stuart Milner-Barry , wrote: “With the possible exception of antiquity, as far as I know, no war has ever been fought in which one side has constantly read the important secret reports of the opponent's army and navy . "A similar conclusion is drawn in an American investigation report written after the war:" Ultra created an awareness in the military leadership and at the political top that changed the way in which decision-making was made. The feeling of knowing the enemy is extremely comforting. It increases imperceptibly in the course of time if you can observe your thoughts and habits and actions regularly and very precisely. Knowledge of this kind frees one's own planning from excessive caution and fear; one becomes safer, bolder and more energetic. "
“In Europe, the ability of the Allies to crack the German encryption systems and read all messages (code name ULTRA) made the Allies rush from victory to victory. In the “ Battle of the Atlantic ”, the most fundamental dispute of the entire Second World War, the Allies were able to steer their convoys past the German submarines because they knew where they were lurking like packs of wolves. In this way, crippling losses could largely be avoided and people and goods could be brought safely to Great Britain. Later, during their great invasion of Europe that led to the victory over Hitler's Reich, the decoding of German embassies helped the Allies anticipate and repel counterattacks. In this way, they were able to better identify German weaknesses and advance into the Ruhr area and Berlin. Even Soviet code breakers could decipher the Germans the secret information, which contributed to their victory on the Eastern Front. "
The former national security adviser to US President Jimmy Carter , the Polish-American political scientist Zbigniew Brzezinski cited the Supreme Commander of the Allied Forces General Dwight D. Eisenhower , the Ultra as decisive ( German "critical" ) called for the win. The Polish historians Władysław Kozaczuk and Jerzy Straszak wrote "it is widely believed that Ultra saved the world at least two years of war and possibly prevented Hitler from winning". ( German "it is widely believed that Ultra saved the world at least two years of war and possibly prevented Hitler from winning it" ).
The renowned British historian and cryptologist Ralph Erskine said simply and clearly: The break-in of the naval Enigma "saved Great Britain from defeat in the submarine war". Even Stuart Milner-Barry took the view that "had we not at the most crucial times and for long periods read the U-boat ciphers, we shouldhave lost the war" ( German "we would not have the decisive time and for long periods could read the submarine ciphers, then we would have lost the war ” ). In an exhibition about the Secret War ( German "Secret War" ), the world in one of the most important war museums, the 2003 Imperial War Museum ( German "War Museum British Empire " took place) in London, former British prime minister Winston Churchill quoted, who gave his King George VI. had said. "It was thanks to Ultra did we won the war" ( German "It was ultra owe that we have won the war" ).
In his book The Hut Six Story , Gordon Welchman , who alongside Alan Turing was one of the leading figures in the British code breakers in Bletchley Park, describes the tightrope walk that the Allied cryptanalysts had to walk in order not to catch up with the Germans over and over again to lose introduced cryptographic complications. Multiple stand the Entzifferungsfähigkeit on a knife edge, and again the scales dropped in favor of the code breaker, often with the best of luck as Welchman admits in his book: "We were lucky" ( German "We were lucky" ).
“The success of the code breakers was ultimately based on some brilliant ideas […] If Marian Rejewski in Poland in 1931 and Alan Turing and Gordon Welchman in England in 1939 hadn't had these ideas, the» Enigma «might not have been cracked. So the idea that the Allies could have failed to crack this cipher machine is no speculation in a vacuum, but there actually was a lot to be said for this assumption. "
In his 2018 book X, Y & Z - The Real Story of how Enigma was Broken ( German "X, Y & Z - The true story of how the Enigma was broken" ) calls for the author Sir Dermot Turing , nephew of Alan Turing , the reader on:
“Imagine a counterfactual history in which the British had not been able to decipher Enigma messages during the Battle of Britain, the naval war in the Mediterranean, the early years of the Battle of the Atlantic, or in the campaign in the Western Desert. Such a scenario is frightening, as it would be a history that depicts not just a longer, drawn-out war but potentially one with a quite different outcome. "
“Imagine a counterfactual story in which the British used the Enigma sayings during the [air] battle for England , the sea war in the Mediterranean , the early years of the Atlantic battle or in the [Africa] campaign in the [Libyan ] Western desert could not have deciphered. Such a scenario is frightening because it would be a story that not only represents a lengthy, drawn-out war, but possibly a war with a completely different outcome. "
The consideration of alternative histories is inevitably highly speculative. Of course, the point in time at which the Enigma might have been made burglar-proof is also decisive. If this had only happened in 1945, it would probably have had only minor consequences for the course of the war. In 1944, however, the Allied invasion plans for Operation Overlord (" D-Day ") would have been hindered. As we know today, not only was the entire German battle line-up in Normandy known in detail from deciphered Enigma radio messages , but the Allied commanders were also kept extremely precise every day about the German plans and countermeasures thanks to Ultra . In the years from 1941 onwards, the German submarines would not have been so easy to find, the positions and plans of which the Allies could precisely follow from deciphered radio messages.
But what if the Enigma had remained unbreakable from the start? In 1940, for example, the Royal Air Force used its last reserves to eventually win the Battle of Britain . Here, too, deciphered radio messages, in particular about the German Air Force's attack plans, were of great help. Without this help, the air battle might have been lost and the Sea Lion operation , i.e. the German invasion of England, might have taken place. How it would have turned out can only be speculated about: It would be conceivable that the war would have ended after a German occupation of the British Isles in 1940, because at that time neither the Soviet Union nor the United States were at war. (The German attack on the Soviet Union began on June 22, 1941. The Japanese attack on Pearl Harbor took place on December 7, 1941 and Germany declared war on the USA on December 11, 1941.) How world history changed in such a case no one can say, because history does not tell us its alternatives. In an essay that David Kahn wrote as a counterfactual story on the assumption that the Allies did not succeed in cracking the Enigma, it leads to another triumphant advance of the Wehrmacht, which is finally ended abruptly by an atomic bomb . These are all speculations - however, the enormous importance of cryptography and the cryptanalysis of the Enigma key machine for the course of history becomes clear.
Particularly noteworthy is the fact of the perfectly functioning secrecy of the Enigma decipherments carried out in Bletchley Park and the ultra information obtained from it . Churchill himself paid tribute to his secretive code breakers with the words "My geese that laid the golden eggs and never cackled" ( German: "My geese that laid the golden eggs and never cackled" ). This "Enigma Secret" was throughout the war and even after that until the 1970s, guarded ( Britain's best kept secret , German "Britain's best kept secret" ). The Germans had no idea about Ultra . There was no mole in Bletchley Park - with one exception, John Cairncross , but he was spying for the Soviet Union.
Due to various suspicious events, several investigations were carried out on the German side as to whether the Enigma was really safe, but the wrong conclusions were drawn here and the experts with the correct assessment did not prevail. The fragmentation of the German services - in contrast to the competence concentrated in BP - is certainly a reason for not recognizing the security gaps in the machine. The partially rival cryptological offices existed side by side in Germany, such as the encryption department of the High Command of the Wehrmacht (OKW / Chi), the General of Intelligence (OKH / GdNA) in the High Command of the Army , the B-Dienst (observation service ) of the Navy , the Research Office ( FA) of the Air Force as well as the Office IV E in the Reich Security Main Office (RSHA).
A report by the American Army Security Agency written shortly after the war mentions that the German submarine commander (BdU) Admiral Karl Dönitz was the real reason for the victory, which was already within reach before July 1942, and the battle that was lost only a few months later Atlantic never understood:
"It was never realized that cryptanalysis, rather than radar and direction finding, disclosed the positions and intentions of the German submarines."
"At no point was it recognized that the cryptanalysis and not the radar technology or radio location revealed the positions and intentions of the German submarines."
It would not have been difficult for the Germans to check the safety of their machines. As a test , the British historian Hugh Sebag-Montefiore suggests sending a message encrypted with the Enigma as usual, in which, as a deception , a meeting of German submarine tankers at a remote location at sea, which is normally not from Allied ships are visited. If allied warships should suddenly appear at the agreed meeting point at the time specified in the radio message, it could have become clear to the Germans fairly quickly that their machine was indeed compromised.
Towards the end of the war, thousands of Enigma machines were destroyed, buried or sunk to prevent them from "falling into enemy hands". According to the “ rainbow order ” of the Kriegsmarine, for example, even submarines had to be scuttled in order not to have to hand them over to the enemy. Such relics are found from time to time. For example, at the end of 2020 it was reported that an Enigma specimen could be recovered from the seabed of the Geltinger Bay , and in January 2021 six damaged specimens were also lifted from the Baltic Sea near Schleimünde .
After the war, the Enigma machines, which were captured in numbers of several hundred, possibly thousands, and also replicated, were mainly sold or given away by the Western powers to allies or friendly nations. For example, the British offered the newly founded State of Israel in 1948 30 of the German encryption machines, which at that time were still generally considered to be “highly secure” and “unbreakable”. The Israelis were delighted with this precious gift and began to modify the German machines for their own purposes. They improved the cryptographic security and combinatorial complexity of the Enigma and replaced the Latin alphabet with Hebrew letters in the keyboard, lamp panel, plug board and roller set . However, they finally gave up the use of these now Israeli Enigma machines after they had received a subtle hint from the British-Jewish mathematician Joseph Gillis (1911–1993), who had worked at Bletchley Park. In Korea, in former British colonies and protectorates as well as in some African states, Enigmas were still used in some cases until 1975, which enabled the Western powers to read their communications. The few intact specimens that still exist today - it is estimated that there are still around 400 exhibits in museums or with private collectors - are traded at collector's prices in the five and even six-figure range. In 2017, Christie's , one of the world's leading auction houses for art and antiques , auctioned an Enigma-M4 from the war year 1944 for the record-breaking sum of $ 547,500 (around € 500,000 ).
potential for improvement
In 1883 the Dutch cryptographer formulated Auguste Kerckhoffs under the later (1946) explicitly by Shannon stated assumption "the enemy knows the system being used" ( German "The enemy knows the system used" ) its binding for serious cryptography maxim.
- Kerckhoffs' principle : The security of a cryptosystem must not depend on the secrecy of the algorithm . Security is only based on keeping the key secret.
The cryptographic security of the Enigma depended - contrary to Kerckhoffs' maxim - essentially on the secrecy of its roller wiring. This could not be changed by the user, so it was part of the algorithm and not of the key. It is noteworthy that the roller wiring was not changed from the beginning in the 1920s to 1945, with very few exceptions, called “ special circuits ”. Under the usual conditions of use of a key machine as widespread as the Enigma, one must not assume that its algorithmic components can be kept secret in the long term, even if the Germans tried.
A first possibility for improving the Enigma would have been to completely replace the range of rollers every year, for example, with radically changed wiring, similar to what the Swiss did with their K model . Rollers would be even more effective if their internal wiring could be designed variably depending on the key. Interestingly, there was an approach to this, namely the reverse roller D (British nickname: Uncle Dick ), which had exactly this property, but was only used late (Jan. 1944) and only occasionally. This "pluggable reversing roller Dora", as it was called from the German side using the spelling alphabet used at the time, enabled freely selectable wiring between the contact pins and thus a variable connection between pairs of letters.

Significant cryptographic strengthening of the Enigma would easily have been possible in the construction stage. First and foremost, the restriction to fixed-point-free permutations should have been avoided. The Involutorik (encrypt = decrypt), although convenient for operation, weakened the machine enormously. Both would have been avoided if the reversing roller had been omitted.
Already an early forerunner of the Enigma I, meaning the Enigma-H from 1929, which was called Enigma II by the Reichswehr and later also by the Wehrmacht, had eight firmly arranged (non-exchangeable) rollers and one alone adjustable key space of more than 200 billion through the roller position. Compared to the only 17,576 cylinder positions of the Enigma I, it offers a considerably greater combinatorial complexity. In addition, this early Enigma model did not have a reverse roller, so it did not have any of its weaknesses. If this basic design with eight (instead of just three) rollers had been transferred to the Enigma I and, as there, the position of the rollers had been made interchangeable, this would have been 8 with eight rollers! = 40,320 (instead of just 60) roller positions and, in combination with the roller positions, result in a cryptographically effective key space of 8,419,907,243,704,320 (more than eight quadrillion or almost 53 bits). Compared to the only good one million (about 20 bit) cryptographically effective possibilities of the actually implemented Enigma, this would have resulted in a significantly stronger machine, which, despite the many errors on the German side and the gigantic effort on the British side, probably could not have been broken. However, such a machine with eight rollers would have been less handy than the Enigma with only three rollers.
Scherbius had in his basic patent of February 23, 1918 even ten indicated around 100 trillion key rolls and the resulting (even without replacement) from it, also not turning roll, but a switch for setting the encryption and decryption, and an above gear adjustable Irregular further movement of the rollers suggested - all good ideas and cryptographically strong design features, which, however, were forgotten in the course of time. The founding president of the Federal Office for Information Security (BSI), the mathematician and cryptologist Otto Leiberich, said in 2001 that with four cylinders "and with a non-uniform drive, the Enigma would never have been deciphered."

An example of the strength of these ideas is the Sigaba key machine . This is an American rotor machine similar to Enigma, and also from the Second World War, but do not turn roll, but five Chiffrierwalzen ( cipher rotor Bank , German "Chiffrierwalzensatz" offers) and additionally twice five other rolls ( control rotor bank and index rotor bank , German "Steuerwalzsatz" and "Indexwalzsatz" ), which serve solely to generate an irregular progression of the cipher rollers. The Sigaba creates fixed points as well as non-invulatory permutations and could not be broken at any time, neither by German nor by Japanese cryptanalysts, nor by the Americans themselves, who tried to do this on a trial basis.
A very easy way to make the Enigma more secure is to use more than one carryover notch . These notches are part of every roller and cause the transfer to the next roller, which is further to the left in the roller set, and thus ensure that the rotors are switched. It was very convenient for the code breakers that they could assume, for 26 letters, that only the right roller was rotating and only then would it be switched to the middle rotor. For relatively long text passages, the Enigma therefore consists, from the perspective of the cryptanalyst, of a single rotating (right) roller and a particularly thick (stationary) reversing roller consisting of a middle and left roller as well as the reversing roller. This only interferes with the transfer to the middle roller. If the Enigma reels had more than a single transfer notch, for example nine, as in the British key machine Typex , practically nothing would have changed for the user, but the cryptanalysis would be strong due to the more frequent switching of the middle and left reels been disturbed.

Peter Twinn , one of Turing's employees in Bletchley Park, commented on it with the words "they certainly missed a trick in not combining multiple-turnover wheels with plug connections" ( German: "They [the Germans]] certainly missed a trick by not rolling with several transfer notches and the plug connections combined " ). Gordon Welchman underlined the consequences of this German mistake: "We would have been in grave trouble if each wheel had two or three turnover positions instead of one" ( German: "We would have had serious problems if each roller had had two or three transfer notches instead." [only] one " ). The Typex proved to be unbreakable for OKW / Chi , the cipher department of the OKW , not least because of its larger number of transfer notches compared to the Enigma .
Perhaps the developers of the Enigma feared a reduction in the period , that is the number of characters after which the alphabet used for encryption repeats itself. The period for the Enigma I is 26 · 25 · 26 = 16,900, whereby the factor 25 for the middle roller is caused by the already mentioned (unimportant) anomaly of the indexing mechanism. Using an even number or thirteen carry notches instead of just one would actually drastically decrease the period since these numbers have common factors of 26. For example, with three, five, seven, nine or eleven notches, however, this risk does not exist, since these numbers are relatively prime to 26 . Interestingly, in addition to the five rollers known from the Enigma I, three further rollers were used in the Navy (VI, VII and VIII), which have more than one, namely two transfer notches. The three rollers used exclusively by the Navy also avoided another fault of the five rollers on the Enigma I, because they all had their transfer notches with identical letters. Not so with reels I to V, which are revealed by the transfer of different letters. The code breakers had for the (linguistically nonsensical) Merkspruch " R oyal F lags W ave K ings A bove" formed, which calls for the rolls I to V in this order each character that always appears in the window after a carry on the next roll is done.
A significant innovation that would have significantly improved the cryptographic security of the Enigma, but which came too late to be used during the war, were the so-called " gap filler rollers " ( see photo under web links ). These new types of rotors made it possible to “set any type and number of switching gaps on each roller”. The settings could have been changed depending on the key and thus contributed significantly to the cryptographic strengthening of the machine. In July 1944, the Ertel factory in Munich received a production order for 8,000 pieces of gap filler rollers, which was increased to 12,000 pieces shortly afterwards. Due to the war, however, only a few could be produced and none could be delivered. The American Target Intelligence Committee (TICOM) confiscated all information about the gap filler roller towards the end of the war and carefully kept it under lock and key for many years. If it could have been manufactured and used in sufficient numbers, the British code breakers would probably have been out of the running, especially if the gap filler roller had been used in combination with the reversing roller D as planned.

The German Abwehr (secret service) used an Enigma model (G) , which had an exclusive set of rollers in which the (three) rollers actually had several transfer notches , namely 11, 15 and 17 notches, respectively. In contrast to the other Enigma models, even the reversing roller was rotatable and rotated with it. This strengthened the encryption and made sure that other German authorities could not read along. However, the defense did without a plug board in this particularly compact (external dimensions 270 mm × 250 mm × 165 mm) and superbly crafted Enigma. The result was that the codebreakers of Bletchley Park, at the head "Dilly" Knox and his colleagues Margaret Rock and Mavis Lever , respected in BP as "Dilly's girls", succeeded on December 8, 1941 in overcoming this encryption and thus to contribute to the fact that German agents could be "received" as soon as they entered the country. These were then not simply eliminated, but the British domestic secret service MI5 succeeded in "turning around" many of them and using them as double agents within the framework of the Double Cross system ( German " Doppelkreuz ", but also: " Doppelspiel " ) . Together with the information deciphered from Enigma-G sayings, the MI5 received such a detailed and accurate picture of the plans and the level of knowledge of the defense that every single German agent still operating in Great Britain was precisely known and could be specifically controlled and manipulated. This was also used to disinformation the German leadership (see also: Operation Fortitude ).
In summary, the following points can be noted about the cryptographic strengthening of the Enigma, the implementation of which would have been possible before or during the war and which could easily have led to the Enigma suddenly being "beyond the reach of the already strongly stretched Anglo-American cryptanalytic fingers would have what might have changed the course of the war "( English " Improvement in anyone of the foregoing particulars could easily have pushed the plug-board Enigma beyond the reach of already-straining Anglo-American cryptanalytic fingers, and possibly altered the course of the was " ):
- allow identical encryption
- Avoid involvement
- Attach several (e.g. nine) transfer notches
- Arrange transfer notches identically for all rollers
- use adjustable transfer notches (gap filler rollers)
- install more than three rollers (e.g. six as with the SG-41 )
- Expand the range of rollers (e.g. ten instead of just five)
- freely wirable pluggable reversing roller (VHF Dora)
- Radically change roller wiring occasionally
- do not use involutive plugs

An amazingly simple yet resoundingly effective measure which, according to Gordon Welchman, could easily have been introduced at any point in time and which he feared most during the war, is the use of single-pole plug connections instead of double-pole involutive cables. Then, for example, you could plug X with U and U now not necessarily with X, but with any other letter. In this way, the involvement of the plug board - if not the whole machine - could have been abruptly eliminated. According to Welchman, this would have had disastrous consequences for the code breakers in Bletchley Park. Much of the developed methodology there including the Welchman self-invented diagonal board ( German Diagonal Board ) would have been useless. He writes "the output of Hut 6 Ultra would have been reduced to at best a delayed dribble, as Opposed to our up-to-date flood." ( German "the yield of the ultra-information from barrack six would have, at best, on a delayed trickle reduced, in contrast to our daily tide. " )
Models



A rough overview of the confusing variety of Enigma models is shown in the following table (see also: Enigma family tree under web links ). In addition to the model name, the year of commissioning, the number of rollers and the resulting number of possible roller positions are given. Furthermore, the number and type of reversing roller (VHF) is noted, whereby a distinction must be made between built-in VHF and manually adjustable, ie "settable" VHF and rotating VHF, i.e. VHF that continue to rotate during the encryption process. An example of this is the Enigma-G of defense described above . Some early machines, such as the “ Handelsmaschine ” from 1923 and the “ Writing Enigma ” from 1924, had no VHF. The number of transfer notches is also given, as well as a literature reference for reference and for further information.
| model | year | Rollers | Locations | FM | Notches | Ref |
|---|---|---|---|---|---|---|
| Enigma I | 1930 | 3 out of 3 (5) | 6 (60) | 1 (3) fixed | 1 | Kruh 11 |
| Enigma II | 1929 | 8th | 1 | 1 fixed | see Enigma H | |
| Enigma-A | 1924 | 2 | 1 | 1 rotates | Crypto Museum | |
| Enigma-B | 1924 | 2 or 3 | 1 | 1 fixed | Crypto Museum | |
| Enigma-C | 1925 | 3 | 1 | 1 fixed | 1 | Kruh 5ff |
| Enigma-D | 1926 | 3 | 1 | 1 settable | 1 | Farmer 114 |
| Enigma-G | 1936 | 3 out of 3 | 6th | 1 rotates | 11, 15, 17 | Hamer |
| Enigma-H | 1929 | 8th | 1 | 1 fixed | Crypto Museum | |
| Enigma-K | 1936 | 3 out of 3 | 6th | 1 settable | 1 | Hamer 10ff |
| Enigma-M1 | 1934 | 3 out of 6 | 120 | 1 fixed | 1 | Prose 50 |
| Enigma-M2 | 1938 | 3 out of 7 | 210 | 1 fixed | 1 | Prose 50 |
| Enigma-M3 | 1939 | 3 out of 8 | 336 | 1 fixed | 1 (2) | - |
| Enigma-M4 | 1942 | 4 out of 8 + 2 | 1344 | 2 settable | 1 (2) | Erskine & Weierud 50 |
| Enigma-T | 1942 | 3 out of 8 | 336 | 1 settable | 5 | Girard |
| Enigma-Z | 1931 | 3 out of 3 | 6th | 1 rotates | 1 | Wik |
| Trading machine | 1923 | 4th | 1 | no | transmission | Kruh 2 |
| Test machine | 1918 | 2 to 7 | 1 | no | transmission | Scherbius |
| Writing Enigma | 1924 | 2 times 4 | 1 | no | transmission | Prose 50 |
In addition to the most widely used models Enigma I, Enigma-M3 and Enigma-M4 as well as their predecessors Enigma-A to Enigma-D and the already mentioned Enigma-G and Enigma-K, the Enigma-T is also worth mentioning, which is specially designed for the communication of the two War allies Germany and Japan was conceived. It was named after the German Grand Admiral of the former Imperial Navy Alfred von Tirpitz (1849-1930) as the " Tirpitz machine " and had no plug board, but a "settable" (adjustable, but not rotating) reversing roller and a total of eight rollers each with five transfer notches (see also: Enigma rollers ), three of which have been selected. The Enigma-T was hardly ever used. It should not be confused with the Enigma replica developed in Japan, the San-shiki Kaejiki .
The Enigma-Z , which was offered for sale to the Spanish Foreign Ministry in 1931, is a curiosity . It is a variant similar to the Enigma-D, but does not have any letter keys, just ten number keys (“1” to “0”) and corresponding (smaller) rollers with only ten contacts and ten light bulbs for “1” to Has "0". So she was not thought to encrypt texts, but only by numbers, such as the over coding of diplomatic codes. For example, the sequence of digits “25183 91467” could be encoded as “38760 15924”. The Spaniards decided not to purchase the Enigma-Z and instead opted for the even less secure Kryha .
anomaly
The indexing mechanism of the rollers has a special design feature, which means that the Enigma's rollers do not keep turning as would be the case with a mechanical odometer. This peculiarity manifests itself in such a way that the left (slow) roller always “takes” the middle roller with it when it moves forward. This can be illustrated with an example.
For example, in the case of roller position B I II III, ring position 01 01 01 and roller position ADU, the roller set continues to rotate with the first push of the button ADV. This is a completely normal further rotation of only the right roller, without switching the middle or left roller. According to the known rule of thumb " R oyal F lags W ave K ings A bove", ie when they weiterrotiert for roll III with the next keystroke from V to W, can be expected to transfer to the middle roll. Then not only will the right roller continue to rotate normally, but the middle roller will also switch from D to E at the same time. The next roller position is therefore AEW.
Now, however, the middle roller (here: roller II) has reached the letter, namely E, which, according to the rule of thumb, is immediately before its shift letter F. The moment has now come when the middle roller in turn effects a transfer to the left roller. The next time you press the button, the left roller will continue to turn from A to B. Due to the special design feature mentioned, this further turning leads to the fact that it takes the middle roller with it and it rotates again, i.e. from E to F. Consequently, the next time the button is pressed, all three rollers are switched on at the same time and after the previous roller position AEW is now immediately the letters BFX can be seen in the display windows of the Enigma. After this somewhat strange occurrence, the machine returns to the regular advance mode, until the middle roller reaches the letter E again after pressing 650 keys. A video can be found under web links , which uses a wooden model to illustrate the roller progression, in particular the anomalous double step of the middle roller.
In summary, once again the indexing of the roller set. The anomaly can be seen here when the button is pressed three times, which manifests itself as a “double step” of the middle roller (here: D → E → F).
Anfangsstellung ADU 1. Tastendruck ADV 2. Tastendruck AEW 3. Tastendruck BFX ← Anomalie 4. Tastendruck BFY
In total, this effect of the double step of the middle roller caused by the anomaly of the indexing mechanism leads to the fact that of the theoretically possible 26³ = 17,576 roller positions of the Enigma I 26² = 676 are left out and only 26 · 25 · 26 = 16,900 remain.
Authentic radio messages
Messages encrypted with the Enigma were usually transmitted by radio , only rarely as a telex or by telephone as a "message" or by a signal lamp as a "flashing message". The sender filled out a form with the plain text that the encryptor used as the basis for the ciphertext generated using the Enigma machine. He transferred this letter by letter into a corresponding radio message form (see also: Documents under web links ), which in turn served the radio operator as the basis for the radio message transmitted in Morse code . The author, the encryptor and the radio operator of the message could be three different people or one and the same.
An important identification of the radio message, which was particularly highlighted in the message sheet with a colored pencil , was the "message number". By indicating the number in color, the Germans differentiated between "departed", i.e. those to be sent or already sent, in which the message number was entered in the form with a blue colored pen, and "arrived", i.e. received, radio messages in which the number was in Was written in red. Only a few of the innumerable slogans filled out during the war have survived. The vast majority were destroyed after the messages were received and decrypted.
The second very important source for authentic Enigma sayings are the rich records of the Allies. In particular, the archives of the British Y Service (German: "Y-Dienst"), which operated worldwide at the time, are full, but unfortunately only a small part is public accessible. The picture shows one of the rare exceptions from the archive of the service in Bletchley Park. In English, the “Y” onomatopoeically stands for the initial syllable of the word wireless (German literally: “wireless”, meaning “funk”). A corresponding translation of Y Service would therefore be “radio monitoring service”.
The Enigma radio messages reproduced below come from free sources. The secret texts have now been deciphered using modern cryptanalytic methods and computer technology. It should be noted that these are not fictitious radio messages, as offered by the Enigma Cipher Challenge competition (see also: deciphering under web links ), but that these are original radio messages that were actually recorded in this way during the Second World War. It is therefore entirely possible (and also the case here) that mutilations will occur. This means that some characters are incorrect or missing. This applies to both letters and numbers. The latter can be seen very easily. All you have to do is count the length of the ciphertext and compare it with the number given in the headline. Reasons hardly avoidable in practice mutilation, which can also be explained by the special war-related conditions are spelling errors , duty error , atmospheric disturbances such as flashes of lightning during the radio transmission, hearing impairment or simply careless. Outgoing radio messages, which can also be identified by the entry in the “Transported on ...” field (and not “Recorded on ...”), are naturally less garbled than the incoming ones and are therefore usually easier to crack (given the same length of text).
- 83 - ADJ JNA - LMHNX WEKLM UERDS EVHLC JSQQK VLDES ANEVT YEDGI ZQDOD RMDKG SXGSQ SHDQP VIEAP IENLI CLZCL LAGWC BJZD |
- 149 - TLS CMU - FTMKV DRJMG FBUDK LZCTR FLTUU IWVJL OYKYX GDCKJ TMDFB WNLZQ JAXHP GGKFG SBZOQ KQKUK TINMH BAJOO AUILA QVFTK LSTMM XGAQL CNHUW LFHKA ULTXT BIVIF EWWDY PUCNS TPJHR OBWHE KYUSB CANYC W |
- 167 - MRJ LLT - KLIBM ERJAR WMMHJ STHOY OOIQB HSSZU EOOKF TASXN XVYWE SCTCH NRNBL ZPEBH XPAQE DFNYS XHMNI HRARO UNBMD ZRZDN WTGUI UCBZN ZTFJA EKOMJ AZILN RKVFD UNIEW ILZVL KQYYJ ANKXG NNNHT EMAVD FXKAY MLWCV QDFWX LO |
- 186 - DOQ VHZ - PBNXA SMDAX NOOYH RCZGV VZCBI GIBGW HMXKR RVQCF JCZPT UNSWA DDSTI GQQCS AGPKR XXLOM GFXAP HHMRF SDKYT MYPMV ROHAS QYRWF WVAVG CCUDB IBXXD YZSAC JSYOT MWUCN WOMHH JPYWD CCLUP GSWCL MBCZS SYXPG MGMQX AUFUL NOZEQ ENHEI ZZAKL C |
- 195 - EHW TNH - ABTWU GWDMP OGKMQ KBHGK HROUP RMYQY INHSA MWFBP CDQRG LDBFK YNXPP DIQHE AOIFQ AOLRZ ZFPDJ MCGEC TAHHQ MVUYA JIAWM WSOYU UTLEP AVZKG HJWCD LOQHW IMSTC LQDNP VCFCN FRUYR GSSJH ORQMU IFFYU WYNTA XPYIX MYTEE FTDCV EHUOA DCPLM APCAU JJYUK |
- 232 - KPL ZFT - IKPKE WZVTB TXWID JCJAN MPWQZ RKUGF TBBAL IERPD BCDVM ARZEL XXWKF ABVKI WFXDV HJGRR CUCQN YQGAE PNOYN LIYLC DGKYL TXTYP IVDGP YMZLY UXWQS FQLCB DELAN PXXWH TDMNQ ENFWA TJVHO EUPGO CQJCF WSLJR EJJFL TJFJT UIYKT |
- 241 - SDV RUD - TAZUK DVNNF AZOUV YYSXO ZLRJO TMMXK AWPVU TTUXS LAQOX GQUKX XKXAL URHGR SUOHD FJTRE TLFKD MGDXE MWIXX INTLG EDKVL RTJFX RFOIE NNIRR WFKTI BVFVE LLAWR GJNVB YHBZS CJVTZ PDBGV PBNNA LNAKX OUOJG WLJXO UXHDS HXJOU HVBVF DOLMN LYNVC MRGKK YTOCP DUEVN FMIPT GGJYA YBDES P |
- 272 - PPS QJH - QSDCK HQOGN OSAIC GADNM PJIAI NPWBM VLTKQ YUDII GWSHT TZEYE CCHFJ CNYBC HXZNE KOOMV SOLLS NDDGR RXPMS GFOPY SJFSY SBYBS CSKDP IOBQM HSFKV MCSMD HYJNO CHB |
Cinematic reception


The Enigma can be seen in a number of films that are set against the backdrop of the submarine war. In the German cinema classic " Das Boot ", based on the novel of the same name , it is used to decrypt received radio messages. One hears the voice of Herbert Grönemeyer say "Only through the key machine slowly arises from tangled strings of letters a sense," while in close-up the Enigma in action to see and can also be heard. Historically, the use of an M4 is not entirely correct here, as it was only put into service on February 1, 1942, while the boat in the novel and film carried out its patrol in the autumn and early winter of 1941. Thus, correctly, an M3 should have been shown.
In the American film "U-571" , an Enigma is captured by American sailors from a German submarine. Especially from the British side it was criticized that, in misunderstanding of historical reality, Americans are portrayed here as heroes in the capture of an Enigma, while in reality it was the British who succeeded.
The British-American co-production " The Imitation Game - A Top Secret Life " illustrates the life and contributions of Alan Turing as a code breaker in Bletchley Park. Here, too, the Enigma plays a central role. At the expense of historical correctness , many facts are twisted or dramatically exaggerated in the film. For example, Turing's romance with his colleague Joan Clarke is portrayed more intensely than it actually was. Turing's niece Inagh Payne criticized the script with the words: “You want the film to show it as it was, not a lot of nonsense” a lot of nonsense "). In the film, Turing finds out that Cairncross is a spy. However, he succeeds in blackmailing Turing with his homosexuality, which was punishable at the time. So they cover each other's secret from each other. This misrepresentation was heavily criticized because Turing is actually portrayed as a “ traitor ” in the film. In fact, he was never under that suspicion. Despite all sympathy for exaggeration from a dramaturgical point of view, this representation was vigorously rejected as a degradation of Turing and the film was therefore classified as unsustainable.
The British feature film Enigma - The Secret , which is based on the novel Enigma , focuses on the deciphering work of the British code breakers in Bletchley Park. Noteworthy are the many authentic props in the film, which are original showpieces from the Bletchley Park Museum. The various radio messages have been realistically generated and encrypted especially for the film according to the original rules and procedures. Towards the end of the film, a Polish code breaker turns out to be a traitor who tries to reveal the “Enigma secret” to the Germans. This is inconsistent with historical facts in two respects. For one thing, there were - as already stated - no traitors in Bletchley Park who spied for the Germans. On the other hand, not a single Polish cryptanalyst worked there, because for reasons of secrecy the British denied almost all foreigners, even Marian Rejewski, entry and even more so their participation. Thus, the cinematic representation is historically wrong on this point. There was particular criticism of portraying a Pole in the film as a traitor, because least of all Poles have betrayed the Enigma secret. On the contrary, Polish cryptanalysts such as Marian Rejewski, Jerzy Różycki and Henryk Zygalski laid the decisive foundations for breaking into the enigma of the Enigma even before the war, without which the British code breakers would probably not have been able to decipher German radio messages and the second World War would have taken a different course.
chronology

Some important points in time in the history of the Enigma are listed below
(specific points in time for the marine version, see M4 ):
| date | event |
|---|---|
| Feb. 23, 1918 | First patent for Enigma |
| Apr 15, 1918 | Test machine |
| July 9, 1923 | Founding of Chiffriermaschinen AG |
| March 21, 1926 | Patenting of the reverse roller (VHF) |
| July 15, 1928 | The Reichswehr introduces a previous version of the Enigma |
| Aug 9, 1928 | The plug board is introduced by the Reichswehr exclusively for machines used by the military |
| June 1, 1930 | Commissioning of the Enigma I (six plugs and quarterly changing roller positions) |
| Feb. 1, 1936 | Monthly change of the roller position |
| Oct. 1, 1936 | Daily change of the roller position and instead of six now five to eight plugs |
| Nov 1, 1937 | Replacement of VHF A by VHF B |
| Sep 15 1938 | New indicator method (freely selectable basic position for the key encryption) |
| Dec 15, 1938 | Commissioning of rolls IV and V |
| Jan. 1, 1939 | Seven to ten plugs |
| July 26, 1939 | Two days allied meeting at Pyry |
| Aug 19, 1939 | Ten plugs |
| May 1, 1940 | Dropping the spell key duplication |
| 1940/41 | Temporary use of VHF C (as an alternative to VHF B) |
| Oct 5, 1941 | Introduction of the "Triton" key network for the submarines initially with the M3 |
| Oct 15, 1941 | Introduction of the key network "Neptune" for the battleships with the M4 |
| Dec 8, 1941 | First breach of the defense enigma by Dilly Knox |
| Feb. 1, 1942 | Commissioning of the M4 now also for the submarines |
| Sep 1 1943 | Dropping the identification group |
| Jan. 1, 1944 | Occasional use of the pluggable VHF D |
| July 10, 1944 | The Air Force introduces the " clock " |
| Sep 15 1944 | The CY procedure is introduced in the army |
glossary
In connection with the way the Enigma works and its cryptanalysis, the following specialist terminology is used:
- Alphabet - an ordered arrangement of symbols permuted in sequence, specifically the 26 uppercase Latin letters (example: EKMFLGDQVZNTOWYHXUSPA IBRCJ)
- B-Dienst - (abbreviation for observation service): Intelligence service of the German navy in World War II, which dealt with the wiretapping and recording as well as the deciphering and interpretation of the enemy, especially the British radio traffic
- Biuro Szyfrów - (Abbreviation: BS): Polish name for the "cipher office" located in Warsaw, in which Polish cryptanalysts broke the Enigma encryption from 1932 onwards
- Bletchley Park - (Abbreviation: BP): Country estate in the English village of Bletchley , which was the headquarters of the British code breakers during World War II and is now a museum
- Bomba - (plural: Bomby ): Polish name for the cryptanalytical machine developed by Rejewski in 1938, with which the error of the key doubling was exploited to reveal the roller position and the key
- Bomb - (plural: Bombes ): English name for the cryptanalytic machineinventedby Turing in 1939 and improved by Welchman, by means ofwhich the daily key was determinedwith the help of cribs and bypassing the plug board
- Chi - Abbreviation for the encryption department of the Wehrmacht High Command, i.e. the department that dealt with the deciphering of enemy communications and the security control of its own key procedures
- Cipher - Another term for ciphertext
- Encryption - Another term for encryption
- Chi-Text - Another term for ciphertext
- Cillis - (not authentically also called “sillies” (German: “Dummchen”)): English nickname for the incorrect choice of the basic position and the key from neighboring letters on the keyboard (example: QWE RTZ, see also: radio message and faulty slogan head )
- Clash - (German: collision): English technical term for the repeated occurrence of the same roller in the same position (in the same place) in the roller set on two consecutive days.
- Click - Repeated occurrences of identical ciphertext characters
- Confirmation - English technical term used by British code crackers, especially when searching for a connector. (Example: The WF connector is determined after FW had already been recognized, see also: Contradiction )
- Consecutive connector knock-out - see: CSKO
- Constatation - (German: Relation ): English technical term for the pair of letters formed at a certain position in the cryptogram and in the crib .
- Contradiction - (German: contradiction): English technical term used by the British code breakers, especially when searching for connectors. (Example: The WX connector is determined after FW had already been recognized, see also: Confirmation )
- Crab - (German: Krabbe): English nickname for a rotation step of the middle roller in the defense Enigma
- Crash - (German: collision ): English technical term for the simultaneous occurrence of one and the same letter in the same position in the cryptogram and in the crib . Since this was known to be impossible with the Enigma, it served to exclude the assumed crib location.
- Crib - (German: Eselsbrücke, more aptly: Probable word): English term for a text fragment that is expected to appear in plain text (German technical term also: " plain text-ciphertext compromise ").
- CSKO - Abbreviation for "Consecutive plug knock-out" (German: " knocking down consecutive plugs"). British method and device that exploited the frequently practiced flawed peculiarity of the German keyboards of not stickingadjacent letters in the alphabetwith one another (examples: not AB, PQ or XY).
- CY procedure - From Sep 15 Procedure introduced in the army in 1944, in which the left cylinder was adjusted by hand roughly in the middle of a saying.
- Dechiffrat - Another expression for plain text
- Depth - (from English literally "depth"): Two or more ciphertexts that have been encrypted with the same key (German technical term: " Klartext-Klartext-Kompromiss ").
- Double-letter exchange board - code boards used in the submarines for the secret transmission of the spell key
- Double plug cords - (short: plug): connection cable between the front panel sockets
- Entry roller - Fixed roller at the beginning of the roller set
- Decrypt - (English: to decipher ): Conversion of the ciphertext into the plaintext with the help of the key
- Decipher - (English: to decrypt ): Breaking the ciphertext without prior knowledge of the key
- Female - (in the Polish original: samica or colloquially: samiczkami , literally in German: “Weibchen”, German technical term: “one cycle”, occasionally but less precisely: “Fixed point”): Repeated occurrence of an identical ciphertext-plaintext letter pair, thecan be usedfor deciphering
- Filler letters - letters to be chosen randomly for camouflage, especially the first two letters of the identification group
- Ciphertext - Text generated from plaintext by encryption
- Plugged in - two letters are swapped using a cable plugged into the front panel
- Basic position - (English: initialPosition ): rolling position to the coding of the Chamber key
- JABJAB - English nickname coined by Dennis Babbage for the negligent choice of the basic position, also as a key to a saying
- Kenngruppe - (also: letter identification group , English: discriminant , also: disc ): Five letters (two filler letters and three identification group letters) at the beginning of a phrase to identify the key
- Identification group book - code book used by the submarines for the secret transmission of the message key
- Identification Group Letters - The last three letters of the identification group
- Identity group booklet - code book used by the submarines in connection with short signals
- Identification group table - The key table is supplemented by a list with daily changing identification group letters
- Kiss - (German literally: Kuss): English expression for two different ciphertexts based on the same plain text (German technical term: " ciphertext-ciphertext compromise ").
- Cryptogram - Another term for ciphertext
- Short signal booklet - code book used by the submarines to shorten the radio messages
- Letchworth-Enigma - model of the roller set devised by Alan Turing for the purpose of advantageous cryptanalysis
- Lobster - (German: Hummer): English nickname for a simultaneous rotation step of all rollers including the reversing roller in the defense Enigma
- Gap filler roller - innovative roller with freely adjustable transfer notches
- Non-clashing rule - (German: non -collision rule ): English nickname for the incorrect German custom of key panels for neighboring days of the month to avoid reusing a roller in the same place in the roller set
- Non-repeating rule - (German: non-repeating rule ): English nickname for the incorrect German custom of key panels to avoid the reuse of a roller layer within a month
- Period - number of letters after which the alphabet used for encryption repeats (16,900 for the Enigma I)
- QWERTZU - Term coined by Dilly Knox for the wiring sequence of the individual letter keys on the keyboard with the exit contacts of the entry roller
- Ring position - the rotational position of the rings, which determines the offset between the internal wiring of the rollers and the letter that is transferred to the next roller
- Key - Secret setting of the key machine
- Key machine - a summary term for encryption and decryption machine
- Keys - A general term for encryption and decryption
- Key space - set of all possible keys (see also other meaning below)
- Key room - room in which "keying" takes place, often the radio room (see also other meaning above)
- Key table - list of daily keys
- Ciphertext - Another word for ciphertext
- Encryptor - the person who encrypts or decrypts messages
- Six self-steckered letters - (German: six unplugged letters): English term for the (incorrect) German rule for keyboards to leave exactly six letters unplugged (“self-plugged”) and only swap ten pairs (instead of all thirteen)
- Special circuit - In rare cases, special wiring of the rotating rollers is made
- Spruch - ciphertext that is usually transmitted by radio
- Spruchkopf - (English: preamble ): First part of the radio message with unencrypted indication of the time, the number of letters, the basic position and the encrypted message key (such as QWE EWG , English: indicator )
- Message number - serial number of a radio message, with a color differentiation between outgoing (blue) and incoming (red)
- Message key - (English: message setting or indicator ): Individual key for a radio message
- Slogan key duplication - In May 1940 abolished (incorrect) method of transmitting the slogan key twice, which made it possible for Polish cryptanalysts to break in in the 1930s
- Plug - cable connections between the front panel sockets
- Plug board - socket plate attached to the front of the Enigma
- Day key - Daily changing key
- Clock - additional device for the creation of non-intrusive plug connections
- Reversing roller - (mostly) fixed roller at the end of the roller set (abbreviation: UKW)
- Reversing roller D - Innovative reversing roller with selectable wiring (also called: VHF Dora)
- Uncle Charlie - (German: Onkel Charlie): English nickname for the reverse roller C
- Uncle Dick - (German: Onkel Dick): English nickname for the reverse roller D
- Uncle Walter - (German: Onkel Walter): English onomatopoeic paraphrase of the German term "reversing roller"
- Unplugged - (English: self-steckered ): Letters that are not swapped because the cable is not plugged in
- Encrypt - converting plain text into ciphertext
- Wahlwort - (English: Wahlwort ): Word to be chosen randomly that is inserted at the beginning or end of the plain text of a radio message in order to bring it "to different lengths".
- Roller - (English: wheel ): rotor that turns during the keying process
- Roller position - (English: wheel order ): Key-dependent placement of the rollers in the roller set
- Roller set - (English: wheel set or scrambler ): A summary term for all rollers
- Roller setting - (English: wheel setting ): The rotation position of the rollers can be adjusted manually and changed during the keying process
- Weather shortcut key - Code book used by the Kriegsmarine to shorten weather reports
- Y Service - (German: "Y-Dienst"): English name of the British radio monitoring service, whose main task during the Second World War was to intercept and record enemy, especially German, radio traffic
- Cyclometer - (in the Polish original: Cyklometr ): Name for the cryptanalytic device designed by Rejewski in 1934, with which the error of the key doubling was exploited to reveal the roller position and the key
See also
- Enigma watch
- Enigma rollers
- Enigma patents
- Enigma exhibits
- Enigma equation
- Enigma plug board
- Enigma replicas
- Enigma simulations
- Enigma supplements
- Enigma key procedures
- Enigma production mark
literature
- Primary literature
- General key rules for the Wehrmacht. H.Dv.g. 7, M.Dv.Nr. 534, L.Dv.g. 7, April 1, 1944, Books on Demand, 2019 reprint . ISBN 978-37431-9385-7 .
- Signal key for the radio signal service (radio signal key) - secret. M.Dv.Nr. 114, October 1939, Books on Demand, reprint 2019. ISBN 978-37494-6791-4 .
- Gustave Bertrand : Énigma ou la plus grande enigme de la guerre 1939-1945 . Librairie Plon, Paris 1973.
- Francis Harry Hinsley , Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, ISBN 0-19-280132-5 .
- Marian Rejewski : An Application of the Theory of Permutations in Breaking the Enigma Cipher . Applicationes Mathematicae, 16 (4), 1980, pp. 543-559. cryptocellar.org (PDF; 1.6 MB).
- Marian Rejewski: How Polish Mathematicians Deciphered the Enigma . Annals of the History of Computing, 3 (3), July 1981, pp. 213-234.
- Arthur Scherbius: "Enigma" cipher machine . Elektrotechnische Zeitschrift , November 1923, pp. 1035-1036, cdvandt.org (PDF; 1 MB), accessed on February 21, 2019.
- Frederick William Winterbotham : The Ultra Secret . Weidenfeld and Nicolson, London 1974.
- Gordon Welchman : The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, ISBN 0-947712-34-8 .
- Secondary literature
- Arthur O. Bauer: Radio direction finding as an Allied weapon against German submarines 1939-1945. How weaknesses and failures in the radio control of the submarines contributed to the outcome of the “Battle of the Atlantic”. Arthur O. Bauer Selbstverlag, Diemen , The Netherlands 1997, ISBN 3-00-002142-6 .
- Friedrich L. Bauer : Deciphered Secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, ISBN 3-540-67931-6 .
- Ralph Erskine : The Code-Breaking War . Bavarian Academy of Sciences, Akademie aktuell, Munich, November 2002, pp. 5–11. badw.de (PDF; 0.2 MB)
- David Kahn : The Code Breakers - The Story of Secret Writing . Macmillan USA, Reissue 1974, ISBN 0-02-560460-0 .
- David Kahn: Seizing the Enigma - The Race to Break the German U-Boat Codes, 1939-1943 . Naval Institute Press, Annapolis, MD, USA, 2012, ISBN 978-1-59114-807-4 .
- Rudolf Kippenhahn : Encrypted messages, secret writing, Enigma and chip card . Rowohlt, Reinbek bei Hamburg 1999, ISBN 3-499-60807-3 .
- Władysław Kozaczuk , Jerzy Straszak: Enigma - How the Poles Broke the Nazi Code . Hippocrene Books, 2004, ISBN 0-7818-0941-X .
- Władysław Kozaczuk: Secret Operation Wicher . Bernard and Graefe, Koblenz 1989, Karl Müller, Erlangen 1999, ISBN 3-7637-5868-2 , ISBN 3-86070-803-1 .
- Władysław Kozaczuk: Under the spell of Enigma . Military Publishing House , Berlin 1987, ISBN 3-327-00423-4 .
- Jürgen Rohwer : The influence of the Allied radio reconnaissance on the course of the Second World War. Quarterly Issues for Contemporary History , Volume 27, Issue 3, IfZ Munich 1979, ifz-muenchen.de (PDF 1.8 MB), accessed on April 24, 2019.
- Hugh Sebag-Montefiore : Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, ISBN 0-304-36662-5 .
- Simon Singh : Secret Messages . Carl Hanser Verlag, Munich 2000, ISBN 3-446-19873-3 .
- Michael Smith: Enigma deciphered - The "Codebreakers" from Bletchley Park . Heyne, 2000, ISBN 3-453-17285-X .
- Geoff Sullivan , Frode Weierud : Breaking German Army Ciphers . Cryptologia , Vol XXIX (3), July 2005, pp. 193–232 tandf.co.uk (PDF; 6.1 MB)
- Dermot Turing : X, Y & Z - The Real Story of how Enigma was Broken. The History Press , Stroud 2018, ISBN 978-0-75098782-0 .
- Heinz Ulbricht: The Enigma cipher machine - deceptive security. A contribution to the history of the intelligence services. Dissertation Braunschweig 2005. tu-bs.de (PDF; 4.7 MB), accessed on May 18, 2016.
Web links
Details
- Website Bletchley Park , English
- Website Breaking German Navy Ciphers , especially Breaking the M4, English
- Website Cipher Machines and Cryptology , simulation programs and challenges , English
- Crypto Cellar website , many original documents, English
- Website Crypto Museum , lots of detailed information about the various Enigma models, English
- Website Enigma Museum , many photos of original Enigma machines, English
- Enigma Family Tree Family tree of the Enigma, English
- Secret operation Wicher of the Polish secret service
- The pinch from U 559 , report on the capture of the weather short key and the short signal booklet, English
- Radio direction finding as an allied weapon against German submarines 1939–1945 , website with excerpts from the book by Arthur O. Bauer
- The golden goose that never chatters by André Schulz
- Defense radio - radio defense. Technology and procedures of espionage radio services. Revised version of an unpublished manuscript, 2018, by Rudolf Staritz

Documents
- The Enigma writing cipher sales brochure (front), ca.1924.
- The Enigma writing cipher sales brochure (back), approx. 1924.
- Brief description of the writing “ENIGMA” cipher machine (PDF; 1.7 MB), scan of the product brochure from 1931.
- The key M (PDF; 3.3 MB), scan of the original regulation from 1940.
- Spruch Nr. 233 (PDF; 201 kB), authentic Spruchform with received radio message.
- Air Force machine key No. 619 (PDF; 316 kB), authentic key board.
- Double-letter exchange tables (PDF; 2.9 MB), scan of the original “Password: Source” tables.
- Radio message forms
- The Enigma Collection by Frode Weierud (English).
Decipherments
- Breaking German Wehrmacht Ciphers by Frode Weierud (English).
- Breaking German Navy Ciphers , modern deciphering of the M4, English
- M4 Message Breaking Project , modern deciphering of the M4, English
- Enigma Cipher Challenge competition: Crack ten (fictitious) Enigma radio messages, English
Exhibits
Photos, videos and audios
- Photos of the Enigma machine
- Historical photos of the key work with the Enigma
- Photos by Arthur Scherbius , Hans-Thilo Schmidt , Alan Turing and the "gap filler roller"
- Instructional videos on Enigma on the YouTube video portal , English
- Audio interview with the German cryptologist Friedrich L. Bauer about the Enigma (about 19 minutes)
- Video on YouTube, which uses a wooden model to illustrate the roller progression, in particular the double step of the middle roller .
Replica projects
- Replica of an Enigma I
- Replica of an Enigma I
- Replica of an M4
- Replica of an M4 , English
- Electronic replica " Enigma-E " in the Crypto Museum , English
- Electronic replica " meinEnigma ", English
- 3D-printed replica "ENIGMA RDE"
Simulations of the machine
- Windows , Enigma I, M3 and M4 realistically visualized, English.
- Windows , other variants such as Enigma-G and Enigma-T as well as Nema and Sigaba, English.
- Android "EnigmAndroid" , free app for Android , English.
- Android "Enigma Simulator APK" , free app for Android, English.
- MAC OS , English.
- RISC OS , English.
Encryption simulations
- Paper Enigma ( Memento from March 30, 2017 in the Internet Archive ) (PDF; 84 kB), paper version of the Enigma encryption
- The Enigma on paper (PDF; 210 kB), document for building a paper Enigma yourself
- Universal Enigma , JavaScript, cross-browser
- Cryptii , JavaScript, cross-browser
Individual evidence
- ^ Karl de Leeuw and Jan Bergstra (eds.): The History of Information Security - A Comprehensive Handbook . Elsevier BV, Amsterdam, Netherlands, 2007, p. 389. ISBN 978-0-444-51608-4 .
- ↑ Tom Perera, Dan Perera : Inside Enigma. 2nd edition, Radio Society of Great Britain (RSGB) 2019, p. 19, ISBN 9781-9101-9371-6 .
- ^ A b Karl de Leeuw: The Dutch Invention of the Rotor Machine, 1915-1923 . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 27.2003,1 (January), pp. 73-94. ISSN 0161-1194 .
- ^ A b c Louis Kruh, Cipher Deavours: The Commercial Enigma - Beginnings of Machine Cryptography . Cryptologia, Vol. XXVI, No. 1, January 2002, p. 1. apprendre-en-ligne.net (PDF; 0.8 MB) Accessed: November 4, 2013.
- ^ Friedrich L. Bauer: An error in the history of rotor encryption devices . Cryptologia, July 1999.
- ↑ a b c patent specification cipher DRP No. 416 219. Accessed : Nov. 4, 2013. cdvandt.org (PDF; 0.4 MB)
- ↑ David Kahn: Seizing the Enigma - The Race to Break the German U-Boat Codes, 1939-1943 . Naval Institute Press, Annapolis, MD, USA, 2012, p. 35. ISBN 978-1-59114-807-4 .
- ↑ David Kahn: An Enigma Chronology . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 17.1993, 3, p. 239, ISSN 0161-1194 .
- ↑ Friedrich L. Bauer: Historical Notes on Computer Science . Springer, Berlin 2009, p. 49. ISBN 3-540-85789-3 .
- ↑ Louis Kruh, Cipher Deavours: The commercial Enigma - Beginnings of machine cryptography . Cryptologia, Rose-Hulman Institute of Technology, Taylor & Francis, Philadelphia PA 26.2002,1 (January), p. 1. ISSN 0161-1194 Retrieved: October 18, 2016. apprendre-en-ligne.net (PDF; 0.8 MB)
- ↑ Anders Wik: The First Classical Enigmas - Swedish Views on Enigma Development 1924–1930. Proceedings of the 1st International Conference on Historical Cryptology, PDF; 12.5 MB 2018, pp. 83-88.
- ↑ Winston Churchill : The World Crisis - 1911-1918 . 4 volumes, 1923 to 1929, ISBN 978-0-7432-8343-4 .
- ^ Julian Corbett : Naval Operations . 1923, ISBN 1-84342-489-4 .
- ↑ Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, p. 177. ISBN 3-446-19873-3 .
- ↑ Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, p. 178. ISBN 3-446-19873-3 .
- ↑ José Ramón Soler Fuensanta, Francisco Javier López-Brea Espiau and Frode Weierud: Spanish Enigma: A History of the Enigma in Spain . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 34.2010,4 (October), p. 309. ISSN 0161-1194 .
- ^ A b c Friedrich L. Bauer: Decrypted Secrets, Methods and Maxims of Cryptology . Springer, Berlin 2007 (4th edition), p. 123, ISBN 3-540-24502-2 .
- ^ Reichswehr and Wehrmacht Enigma Orders in Frode Weierud's CryptoCellar , accessed on April 5, 2021.
- ↑ Enigma Production at Konski & Krüger in Frode Weierud's CryptoCellar , accessed on April 4, 2021.
- ↑ Max Rüegger: Memories of a Korea radio operator - Working with the ENIGMA cipher machine . 2016. PDF; 4.7 MB ( August 25, 2016 memento in the Internet Archive ) Retrieved August 24, 2018.
- ^ Arthur O. Bauer: Radio direction finding as an Allied weapon against German submarines 1939-1945 . Self-published, Diemen Netherlands 1997, p. 31. ISBN 3-00-002142-6 .
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 85. ISBN 0-19-280132-5 .
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 83. ISBN 0-19-280132-5 .
- ↑ Arthur Scherbius: "Enigma" cipher machine . Elektrotechnische Zeitschrift, 1923, p. 1035.
- ↑ a b David H. Hamer : G-312. To defense Enigma . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 24.2000,1 (January), p. 46. ISSN 0161-1194 . Retrieved: November 4, 2013. PDF scan as ZIP; 1.1 MB ( Memento from June 11, 2007 in the Internet Archive )
- ↑ a b Patent electrical device for encryption and decryption DRP No. 452 194. cdvandt.org (PDF; 0.5 MB) Retrieved: November 4, 2013.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 119.
- ↑ High Command of the Navy : The Key M - Procedure M General . Berlin 1940. Retrieved: Nov. 4, 2013, p. 23. cdvandt.org (PDF; 0.7 MB)
- ↑ a b c d e f g Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 115.
- ^ A b Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, ISBN 0-947712-34-8 , p. 213.
- ^ Louis Kruh: How to Use the German Enigma Cipher Machine -A Photographic Essay . Cryptologia , Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 29.2005,3, pp. 193-232.
- ↑ a b c d e OKW: Key instructions for the Enigma key machine . H.Dv. G. 14, Reichsdruckerei , Berlin 1940. (Copy of the original manual with a few small typing errors.) Accessed: August 24, 2018. PDF; 0.1 MB ( memento from September 24, 2015 in the Internet Archive )
- ↑ Philip Marks: Umkehrwalze D: Enigma's rewirable reflector - Part 1 . Cryptologia , Volume XXV, Number 2, April 2001, p. 117.
- ↑ The US 6812 Bomb Report 1944 . 6812th Signal Security Detachment, APO 413, US Army. Publication, Tony Sale, Bletchley Park, 2002. p. 2. codesandciphers.org.uk (PDF; 1.3 MB) Retrieved November 4, 2013.
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 107. ISBN 0-19-280132-5 .
- ↑ John Jackson: Solving Enigma's Secrets - The Official History of Bletchley Park's Hut 6. BookTower Publishing 2014, pp. 96-100. ISBN 978-0-9557164-3-0 .
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 57. Retrieved March 30, 2017. codesandciphers.org.uk (PDF; 0.4 MB)
- ↑ CHO'D. Alexander: Plug knock-out . Publication, Bletchley Park, March 1944. Edited and edited by Frode Weierud , July 1998. Accessed : August 24, 2018. PDF; 0.1 MB ( memento from July 2, 2007 in the Internet Archive )
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 459.
- ↑ Derek Taunt: Hut Six in Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 100. ISBN 0-19-280132-5 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 314. ISBN 0-304-36662-5 .
- ↑ High Command of the Navy: The Key M - Procedure M General . Berlin 1940. Retrieved: Nov. 4, 2013, p. 23. cdvandt.org (PDF; 0.7 MB)
- ↑ a b Dirk Rijmenants: Enigma Message Procedures Used by the Heer, Luftwaffe and Kriegsmarine . Cryptologia , 34: 4, 2010, p. 329 ff.
- ^ A b Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 357. ISBN 0-304-36662-5 .
- ↑ High Command of the Wehrmacht : General key rules for the Wehrmacht . H.Dv.g. 7, Reichsdruckerei , Berlin 1944, p. 13. cdvandt.org (PDF; 0.9 MB) Retrieved on November 4, 2013.
- ↑ High Command of the Navy: The Key M - Procedure M General . Berlin 1940, p. 25 ff. Cdvandt.org (PDF; 0.7 MB) Accessed : Nov. 4, 2013.
- ↑ David H. Hamer, Geoff Sullivan, Frode Weierud: Enigma Variations - An Extended Family of Machines . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 22.1998,1 (July), p. 214, ISSN 0161-1194 . cryptocellar.org (PDF; 80 kB) Accessed: February 15, 2016.
- ↑ Modern breaking of Enigma ciphertexts.Retrieved April 4, 2021.
- ↑ a b Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 117.
- ↑ High Command of the Navy: The Key M - Procedure M General . Berlin 1940, p. 26. cdvandt.org (PDF; 0.7 MB) Retrieved on November 4, 2013.
- ^ A b c Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 168. ISBN 0-947712-34-8 .
- ↑ Louis Kruh, Cipher Deavours: The commercial Enigma - Beginnings of machine cryptography . Cryptologia, Rose-Hulman Institute of Technology, Taylor & Francis, Philadelphia PA 26.2002,1 (January), p. 10. ISSN 0161-1194 , accessed on March 14, 2019. apprendre-en-ligne.net (PDF; 0, 8 MB)
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 404 ISBN 0-304-36662-5 .
- ^ M4 Message Breaking Project. Accessed: Nov. 4, 2013. (Warning: The page doesn't seem to have been updated since 2009!)
- ↑ M4 Project 2006, Third Message (on hoerenberg.com) Retrieved on November 4, 2013.
- ↑ US1905593 Coding Machine. 5 claims Application date November 12, 1929 and in Germany November 16, 1928 (PDF; 487 kB). Granted April 25, 1933. Applicant: Willi Korn of Berlin-Friedenau, Germany, accessed June 5, 2019.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 117.
- ^ Colleen Carper: Bletchley's Secret War - British Code Breaking in the Batlle of the Atlantic. Ashbrook Statesmanship Thesis, 2009, p. 3, PDF
- ↑ Louis Kruh, Cipher Deavours: The Commercial Enigma - Beginnings of Machine Cryptography . Cryptologia, Vol.XXVI, No. 1, January 2002, p. 11. apprendre-en-ligne.net (PDF; 0.8 MB), accessed on February 18, 2019.
- ↑ OKW: Key instructions for the Enigma key machine . H.Dv. G. 14, Reichsdruckerei , Berlin 1940, p. 6. (Copy of the original manual with a few small typing errors.) Accessed: August 24, 2018. PDF; 0.1 MB ( memento from September 24, 2015 in the Internet Archive )
- ↑ a b Robert Harris: Enigma . Novel. Weltbild, Augsburg 2005, p. 71. ISBN 3-89897-119-8 .
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park. Oxford University Press, Reading, Berkshire 1993, p. 86. ISBN 0-19-280132-5 .
- ↑ Patent specification Electrical device for encryption and decryption DRP No. 452 194, p. 1. cdvandt.org (PDF; 0.5 MB) Retrieved: November 4, 2013.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 49.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 276.
- ^ Claude Shannon: Communication Theory of Secrecy Systems . Bell System Technical Journal, Vol 28, 1949 (October), p. 710 f. Netlab.cs.ucla.edu (PDF; 0.6 MB) Retrieved on November 4, 2013.
- ↑ David Kahn: Seizing the Enigma - The Race to Break the German U-Boat Codes, 1939-1943 . Naval Institute Press, Annapolis, MD, USA, 2012, p. 131. ISBN 978-1-59114-807-4 .
- ^ Krzysztof Gaj: Polish Cipher Machine -Lacida . Cryptologia . Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 16.1992,1, ISSN 0161-1194 , p. 74.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 210. ISBN 0-947712-34-8 .
- ↑ OKW: Instructions for use for the Enigma cipher machine . H.Dv.g. 13, Reichsdruckerei , Berlin 1937. Online (PDF; 2 MB) Accessed: Nov. 4, 2013.
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 22. ISBN 0-304-36662-5 .
- ↑ Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, p. 199. ISBN 3-446-19873-3 .
- ^ Marian Rejewski: An Application of the Theory of Permutations in Breaking the Enigma Cipher . Applicationes Mathematicae, 16 (4), 1980, pp. 543-559. Accessed: August 24, 2018. PDF; 1.6 MB ( Memento from December 21, 2015 in the Internet Archive )
- ↑ Friedrich L. Bauer: Historical Notes on Computer Science . Springer, Berlin 2009, p. 295. ISBN 3-540-85789-3 .
- ^ Marian Rejewski: How Polish Mathematicians Broke the Enigma Cipher . IEEE Annals of the History of Computing, Vol. 03, No. 3, p. 221, July 1981, p. 229 f.
- ^ A b Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 42. ISBN 0-304-36662-5 .
- ^ Frank Carter: The Polish Recovery of the Enigma Rotor Wiring . Publication, Bletchley Park, March 2005.
- ↑ David Kahn: Seizing the Enigma - The Race to Break the German U-Boat Codes, 1939-1943 . Naval Institute Press, Annapolis, MD, USA, 2012, p. 76. ISBN 978-1-59114-807-4 .
- ^ IJ Good, Cipher A. Deavours, afterword to Marian Rejewski: How Polish Mathematicians Broke the Enigma Cipher . IEEE Annals of the History of Computing, Vol. 03, No. 3, pp. 213-234, July 1981, pp. 229 f.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 412.
- ↑ Chris Christensen: Review of the IEEE Milestone Award to the Polish Cipher Bureau for “The First Breaking of Enigma Code” . Cryptologia . Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 39.2015,2, p. 180. ISSN 0161-1194 .
- ↑ Tadeusz Lisicki : The performance of the Polish deciphering service in solving the process of the German "Enigma" radio key machine in J. Rohwer and E. Jäkel: The radio clearing up and its role in the Second World War , Motorbuch Verlag, Stuttgart, 1979, p. 66– 81. fgcu.edu (PDF; 1.7 MB) Retrieved May 16, 2017.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 207. ISBN 0-947712-34-8 .
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 16. ISBN 0-947712-34-8 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 49. ISBN 0-304-36662-5 .
- ↑ a b c Ralph Erskine: The Poles Reveal their Secrets - Alastair Dennistons's Account of the July 1939 Meeting at Pyry . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 30.2006,4, p. 294.
- ↑ Mavis Batey : Dilly - The Man Who Broke Enigmas . Dialogue 2011, ISBN 1-906-44715-2 , p. 76.
- ↑ Mavis Batey: Dilly Knox - A Reminiscence of this Pioneer Enigma Cryptanalyst. Cryptologia, Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 32.2008,2, pp. 104-130.
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 126. ISBN 0-19-280132-5 .
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 412.
- ↑ Friedrich L. Bauer: Historical Notes on Computer Science . Springer, Berlin 2009, p. 207. ISBN 3-540-85789-3 .
- ↑ The Alan Turing Internet Scrapbook (English). Retrieved June 17, 2016.
- ↑ The US 6812 Bomb Report 1944 . 6812th Signal Security Detachment, APO 413, US Army. Publication, Tony Sale, Bletchley Park, 2002. p. 9. codesandciphers.org.uk (PDF; 1.3 MB) Retrieved November 4, 2013.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 219. ISBN 0-947712-34-8 .
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 11. ISBN 0-947712-34-8 .
- ↑ David Kahn: The unsolved riddle . In Robert Cowley (Ed.) What Would Have Happened If? Knaur, 2006, p. 395. ISBN 3-426-77887-4 (Counterfactual story under the assumption that the Allies fail to crack the Enigma).
- ^ A b John AN Lee, Colin Burke, Deborah Anderson: The US Bombes, NCR, Joseph Desch, and 600 WAVES - The first Reunion of the US Naval Computing Machine Laboratory . IEEE Annals of the History of Computing, 2000. p. 35. thecorememory.com (PDF; 0.5 MB) Retrieved November 4, 2013.
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, pp. 381f. ISBN 0-304-36662-5 .
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 113. ISBN 0-947712-34-8 .
- ↑ The US 6812 Bomb Report 1944 . 6812th Signal Security Detachment, APO 413, US Army. Publication, Tony Sale, Bletchley Park, 2002. p. 59. codesandciphers.org.uk (PDF; 1.3 MB) Retrieved January 7, 2014.
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 235. ISBN 0-304-36662-5 .
- ↑ Michael Miller: Symmetrical encryption methods - design, development and cryptanalysis of classic and modern ciphers . Teubner, April 2003, p. 70. ISBN 3-519-02399-7 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 344. ISBN 0-304-36662-5 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 345. ISBN 0-304-36662-5 .
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 22. codesandciphers.org.uk (PDF; 0.4 MB) Retrieved March 30, 2017.
- ↑ Michael Pröse: Encryption machines and deciphering devices in the Second World War - the history of technology and aspects of the history of computer science . Dissertation at Chemnitz University of Technology, Leipzig 2004, p. 46.
- ↑ David H. Hamer, Geoff Sullivan, Frode Weierud: Enigma Variations - An Extended Family of Machines . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 22.1998,1 (July), pp. 2 ff, ISSN 0161-1194 . cryptocellar.org (PDF; 80 kB) Accessed: February 15, 2016.
- ↑ High Command of the Wehrmacht: General key rules for the Wehrmacht . H.Dv.g. 7, Reichsdruckerei , Berlin 1944, p. 10. cdvandt.org (PDF; 0.9 MB) Accessed : Nov. 4, 2013.
- ↑ High Command of the Wehrmacht: General key rules for the Wehrmacht . H.Dv.g. 7, Reichsdruckerei , Berlin 1944, p. 6. cdvandt.org (PDF) Retrieved on November 4, 2013.
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 121. ISBN 0-19-280132-5 .
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 400.
- ↑ Michael Smith: Enigma decrypted - The "Codebreakers" by Bletchley Park . Heyne, 2000, p. 107. ISBN 3-453-17285-X .
- ↑ Christopher Morris: Navy Ultra's Poor Relations in Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 235. ISBN 0-19-280132-5 .
- ↑ Impact Of Bombe On The War Effort , accessed May 23, 2018.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 230. ISBN 0-947712-34-8 .
- ↑ Jack Copeland : Enigma . P. 256; Retrieved November 4, 2013. canterbury.ac.nz (PDF; 0.8 MB)
- ↑ Stephen Pincock and Mark Frary: Secret Codes - The Most Famous Encryption Techniques and Their History . Bastei Lübbe, 2007, ISBN 3-431-03734-8 , p. 109.
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 136. ISBN 0-304-36662-5 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, pp. 149 ff. ISBN 0-304-36662-5 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 225. ISBN 0-304-36662-5 .
- ↑ Michael Smith: Enigma decrypted - The "Codebreakers" by Bletchley Park . Heyne, 2000, p. 181. ISBN 3-453-17285-X .
- ^ Rudolf Kippenhahn: Encrypted messages, secret writing, Enigma and chip card . Rowohlt, Reinbek bei Hamburg 1999, p. 247. ISBN 3-499-60807-3 .
- ↑ Stephen Harper: The Battle for Enigma - The Hunt for U-559 . Mittler, Hamburg 2001, p. 50 ff. ISBN 3-8132-0737-4 .
- ↑ Stephen Harper: The Battle for Enigma - The Hunt for U-559 . Mittler, Hamburg 2001, p. 66 ff. ISBN 3-8132-0737-4 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 311. ISBN 0-304-36662-5 .
- ↑ Jennifer Wilcox: Solving the Enigma - History of the Cryptanalytic Bombe . Center for Cryptologic History, NSA, Fort Meade (USA) 2001, p. 52. Accessed Nov. 4, 2013. PDF; 0.6 MB ( memento from January 15, 2009 in the Internet Archive )
- ↑ John AN Lee, Colin Burke, Deborah Anderson: The US Bombes, NCR, Joseph Desch, and 600 WAVES - The first Reunion of the US Naval Computing Machine Laboratory . IEEE Annals of the History of Computing, 2000, pp. 27 ff.
- ^ The Achievements of the Signal Security Agency (SSA) in World War II. NSA, Fort Meade, 2010, p. 4.
- ↑ Erich Gröner: The German warships 1815-1945; - Volume 3: U-Boats, auxiliary cruisers, mine ships, net layers, barrage breakers . Bernard & Graefe, Koblenz 1985, ISBN 3-7637-4802-4 , pp. 118f
-
↑ After Eberhard Rössler: History of the German submarine building. Volume 1. Bernard & Graefe, Bonn 1996, ISBN 3-86047-153-8 , pp. 248-251, the following boats of type XB (4 of 8) and type XIV (7 of 10) were lost from May to October 1943 :
- on May 15; however, according to Wikipedia on May 16, U 463 (Type XIV),
- on June 12th U 118 (type XB),
- on June 24th U 119 (type XB),
- on July 13th U 487 (Type XIV),
- on July 24th U 459 (Type XIV),
- on July 30th U 461 (Type XIV),
- on July 30th U 462 (Type XIV),
- on August 4th U 489 (Type XIV),
- on 07 Aug. U 117 (type XB),
- on October 4th U 460 (Type XIV),
- on Oct. 28, U 220 (Type XB).
- on May 15; however, according to Wikipedia on May 16, U 463 (Type XIV),
- ^ A b Frederick William Winterbotham: The Ultra Secret - The Inside Story of Operation Ultra, Bletchley Park and Enigma . Orion, 2000, pp. 16-17, ISBN 0-7528-3751-6 .
- ↑ Craig P. Bauer: Secret History - The Story of Cryptology . CRC Press, Boca Raton 2013, p. 285. ISBN 978-1-4665-6186-1 .
- ↑ Ralph Erskine: The War of the Code Breakers . Bavarian Academy of Sciences, Akademie aktuell, Munich, November 2002, p. 11.
- ^ David Kahn: The Significance of Codebreaking and Intelligence in Allied Strategy and Tactics . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 1.1977,3, p. 221. ISSN 0161-1194 .
- ↑ Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, p. 229. ISBN 3-446-19873-3 .
- ↑ Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, pp. 229f. ISBN 3-446-19873-3 .
- ↑ David Kahn: The unsolved riddle . In Robert Cowley (Ed.) What Would Have Happened If? Knaur, 2006, p. 398. ISBN 3-426-77887-4 . (Counterfactual story assuming the Allies fail to crack the Enigma)
- ^ Zbigniew Brzeziński: The Unknown Victors . Pp. 15–18 in Jan Stanisław Ciechanowski (Ed.): Marian Rejewski, 1905–1980 - Living with the Enigma Secret , 1st edition, Bydgoszcz, Bydgoszcz City Council, 2005, p. 18, ISBN 83-7208-117 -4 .
- ↑ Władysław Kozaczuk Jerzy Straszak, Enigma: How the Poles Broke the Nazi code . Hippocrene Books, 2004, p. 74. ISBN 0-7818-0941-X .
- ↑ Ralph Erskine: The War of the Code Breakers . Bavarian Academy of Sciences, Akademie aktuell, Munich, November 2002, p. 5.
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 96. ISBN 0-19-280132-5 .
- ^ A b Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, ISBN 0-947712-34-8 , p. 169.
- ↑ David Kahn: The unsolved riddle . In Robert Cowley (Ed.) What Would Have Happened If? Knaur, 2006, p. 400. ISBN 3-426-77887-4 . (Counterfactual story assuming the Allies fail to crack the Enigma)
- ↑ Dermot Turing: X, Y & Z - The Real Story of how Enigma was Broken. The History Press, 2018, ISBN 978-0-75098782-0 , p. 20.
- ↑ David Kenyon: Bletchley Park and D-Day. Yale University Press, New Haven and London 2019 (English), ISBN 978-0-300-24357-4 .
- ↑ Michael Smith: Enigma decrypted - The "Codebreakers" by Bletchley Park . Heyne, 2000, pp. 252f. ISBN 3-453-17285-X .
- ^ A b c Army Security Agency: Notes on German High Level Cryptography and Cryptanalysis . European Axis Signal Intelligence in World War II, Vol 2, Washington (DC), 1946 (May), p. 2, 24 August 2018. PDF; 7.5 MB ( memento from June 11, 2014 in the Internet Archive )
- ↑ a b Stephen Harper: The Battle for Enigma - The Hunt for U-559 . Mittler, Hamburg 2001, p. 24. ISBN 3-8132-0737-4
- ^ Rudolf Kippenhahn: Encrypted messages, secret writing, Enigma and chip card . Rowohlt, Reinbek bei Hamburg 1999, p. 244. ISBN 3-499-60807-3 .
- ↑ Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, p. 202. ISBN 3-446-19873-3 .
- ↑ Diana Payne: The bombes . In Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 137. ISBN 0-19-280132-5 .
- ↑ David Kahn: The unsolved riddle . In Robert Cowley (Ed.) What Would Have Happened If? Knaur, 2006, p. 411. ISBN 3-426-77887-4 . (Counterfactual story assuming the Allies fail to crack the Enigma)
- ↑ James W. Mc Lendon: Information Warfare - Impact an Concerns . Research Report , Maxwell Air Force Base, Alabama 1994, p. 8. iwar.org.uk (PDF; 0.2 MB) Retrieved Nov. 4, 2013.
- ↑ Ted Enever: Britain's Best Kept Secret - Ultra's Base at Bletchley Park . Sutton Publishing Ltd, January 1994. ISBN 0-7509-2355-5 .
- ^ Army Security Agency: Notes on German High Level Cryptography and Cryptanalysis . European Axis Signal Intelligence in World War II, Vol 2, Washington (DC), 1946 (May), p. 5. Accessed: August 24, 2018. PDF; 7.5 MB ( memento from June 11, 2014 in the Internet Archive )
- ↑ Michael Smith: Enigma decrypted - The "Codebreakers" by Bletchley Park . Heyne, 2000, p. 241. ISBN 3-453-17285-X .
- ↑ BBC News: The Cambridge spy ring . Retrieved Nov. 4, 2013.
- ↑ TICOM I-38: Report on Interrogation of Lt. Frowein of OKM / 4 SKL III, on his Work on the Security on the German Naval Four-Wheel Enigma. Naval Communication School, Flensburg-Mürwik, June 1945, (English).
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 222.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology . 3. Edition. P. 447. Springer, Berlin et al. 2000, ISBN 3-540-67931-6 , doi: 10.1007 / 978-3-642-58345-2 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 4. ISBN 0-304-36662-5 .
- ↑ Geltinger Bucht - Divers find "Enigma" on the Baltic Sea bottom . NDR from December 4, 2020, accessed on December 9, 2020.
- ↑ Six Enigma cipher machines in the Baltic Sea recovered from orf.at on January 21, 2021, accessed on January 21, 2021.
- ↑ Schleimünde: Taucher finds six more Enigma cipher machines from January 21, 2021, accessed on March 6, 2021
- ↑ When the British gave away unsafe enigmas to Israel, Klausi's crypto column. Retrieved November 9, 2016.
- ↑ a b Simon Singh: Secret Messages . Carl Hanser Verlag, Munich 2000, p. 231. ISBN 0-89006-161-0 .
- ↑ Nazi Enigma encryption machine may have been used by Britain to spy on Israel (English). Retrieved November 9, 2016.
- ↑ Max Rüegger: Memories of a Korea radio operator - Working with the ENIGMA cipher machine . 2016.
- ↑ Cipher A. Deavours, Louis Kruh: Machine Cryptography and Cryptanalysis Modern . Artech House, 1985, p. 40. ISBN 0-89006-161-0 .
- ↑ David Hamer’s List of Surviving Enigma Machines XLS file; 110 kB , accessed June 6, 2018.
- ↑ Enigma Museum ( Memento from July 12, 2017 in the Internet Archive ) SPECIAL NOTE ABOUT PRICES Accessed: July 10, 2017.
- ↑ ArtDaily.org ( Memento from June 17, 2017 in the Internet Archive ) Christie's sets world auction record for an Enigma Machine sold to online bidder - “World auction records were set for A Four-Rotor Enigma Cipher Machine, 1944, which sold above the high estimate for $ 547,500 to an online bidder ” , accessed October 25, 2020.
- ^ Army Security Agency: Notes on German High Level Cryptography and Cryptanalysis . European Axis Signal Intelligence in World War II, Vol 2, Washington (DC), 1946 (May), p. 76. Accessed: August 24, 2018. PDF; 7.5 MB ( memento from June 11, 2014 in the Internet Archive )
- ^ Claude Shannon: Communication Theory of Secrecy Systems . Bell System Technical Journal, Vol 28, 1949 (October), p. 662. netlab.cs.ucla.edu (PDF; 0.6 MB) Retrieved November 4, 2013.
- ↑ Auguste Kerckhoffs: La cryptographie militaire. Journal des sciences militaires. Vol. 9, pp. 5-38 (Jan. 1883) and pp. 161-191 (Feb. 1883). petitcolas.net (PDF; 0.5 MB) Retrieved November 4, 2013.
- ↑ José Ramón Soler Fuensanta, Francisco Javier López-Brea Espiau and Frode Weierud: Spanish Enigma: A History of the Enigma in Spain . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 34.2010,4 (October), pp. 325-326. ISSN 0161-1194 .
- ↑ David H. Hamer, Geoff Sullivan, Frode Weierud: Enigma Variations - An Extended Family of Machines . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 22.1998, 1 (July), p. 11, ISSN 0161-1194 . cryptocellar.org (PDF; 80 kB) Accessed: February 15, 2016.
- ↑ CHO'D. Alexander: Method for testing “Holmes Hypothesis” for UD publication, Bletchley Park 1998, p. 14. PDF; 0.1 MB ( memento from June 11, 2007 in the Internet Archive )
- ^ A b Louis Kruh, Cipher Deavours: The commercial Enigma - Beginnings of machine cryptography . Cryptologia, Rose-Hulman Institute of Technology, Taylor & Francis, Philadelphia PA 26.2002,1 (January), p. 2. ISSN 0161-1194 Retrieved: August 24, 2018. PDF; 0.8 MB ( Memento from April 13, 2006 in the Internet Archive )
- ↑ Patent Chiffrierapparat . DRP No. 416219, p.1 cdvandt.org (PDF; 0.4 MB) Accessed: November 4, 2013.
- ↑ Otto Leiberich: From the diplomatic code to the trapdoor function. Spectrum of Science , Dossier Cryptography, 4/2001, p. 15.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 221.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 143.
- ↑ Peter Twinn: The Abwehr Enigma in Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 125. ISBN 0-19-280132-5 .
- ^ Army Security Agency: Notes on German High Level Cryptography and Cryptanalysis . European Axis Signal Intelligence in World War II, Vol 2, Washington (DC), 1946 (May), p. 77. Accessed: August 24, 2018. PDF; 7.5 MB ( memento from June 11, 2014 in the Internet Archive )
- ^ Alan Stripp: The Enigma machine in Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 86. ISBN 0-19-280132-5 .
- ↑ a b David H. Hamer: Enigma - Actions involved in the 'double stepping' of the middle rotor . Publication. intelligenia.org (PDF; 0.1 MB) Retrieved November 4, 2013.
- ↑ Jack Good: Enigma and fish . In Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, p. 158. ISBN 0-19-280132-5 .
- ↑ Michael Pröse: Encryption machines and deciphering devices in the Second World War - the history of technology and aspects of the history of computer science . Dissertation at Chemnitz University of Technology, Leipzig 2004, p. 43f.
- ^ When the Russians Visited the Enigma Firm . Retrieved October 14, 2016.
- ^ Report on Berlin Targets by Major Heller. TICOM Report I-104 of September 17, 1945 (English), p. 200, accessed in Frode Weierud's CryptoCellar on April 4, 2021.
- ^ Army Security Agency: Notes on German High Level Cryptography and Cryptanalysis . European Axis Signal Intelligence in World War II, Vol 2, Washington (DC), 1946 (May), p. 2. Accessed: August 24, 2018. PDF; 7.5 MB ( memento from June 11, 2014 in the Internet Archive )
- ^ David H. Hamer: G-312. To defense Enigma . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 24.2000,1 (January), p. 42. ISSN 0161-1194 .
- ↑ Mavis Batey: Dilly Knox - A Reminiscence of this Pioneer Enigma Cryptanalyst . Cryptologia , Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 32.2008,2, pp. 104-130.
- ↑ Frank Carter: The Defense Enigma Machine . Publication, Bletchley Park. bletchleypark.org.uk (PDF; 0.1 MB) Retrieved November 4, 2013.
- ^ A b Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 129. ISBN 0-304-36662-5 .
- ↑ Michael Smith: Enigma decrypted - The "Codebreakers" by Bletchley Park . Heyne, 2000, pp. 190 ff. ISBN 3-453-17285-X .
- ^ Army Security Agency: Notes on German High Level Cryptography and Cryptanalysis . European Axis Signal Intelligence in World War II, Vol 2, Washington (DC), 1946 (May), p. 12. Accessed: August 24, 2018. PDF; 7.5 MB ( memento from June 11, 2014 in the Internet Archive )
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 81. ISBN 0-947712-34-8 .
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 384. ISBN 0-304-36662-5 .
- ^ Manufacture of Enigma Machines by Heimsoeth and Rinke, Berlin. TICOM report M-13 (English) of November 17, 1945, accessed on April 4, 2021 in Frode Weierud's CryptoCellar .
- ↑ Louis Kruh, Cipher Deavours: The commercial Enigma - Beginnings of machine cryptography . Cryptologia, Rose-Hulman Institute of Technology, Taylor & Francis, Philadelphia PA 26.2002,1 (January), p. 11. ISSN 0161-1194 Retrieved: August 24, 2018. PDF; 0.8 MB ( Memento from April 13, 2006 in the Internet Archive )
- ↑ Enigma A in the Crypto Museum (English) accessed on February 20, 2019.
- ↑ Enigma B in the Crypto Museum (English) accessed on February 20, 2019.
- ↑ Louis Kruh, Cipher Deavours: The commercial Enigma - Beginnings of machine cryptography . Cryptologia, Rose-Hulman Institute of Technology, Taylor & Francis, Philadelphia PA 26.2002,1 (January), p. 5. ISSN 0161-1194 Retrieved August 24, 2018. PDF; 0.8 MB ( Memento from April 13, 2006 in the Internet Archive )
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 114.
- ^ David H. Hamer: G-312. To defense Enigma . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 24.2000.1 (January). ISSN 0161-1194 .
- ↑ Enigma-H in the Crypto Museum (English). Retrieved February 11, 2016.
- ↑ David H. Hamer, Geoff Sullivan, Frode Weierud: Enigma Variations - An Extended Family of Machines . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 22.1998,1 (July), pp. 10 ff., ISSN 0161-1194 . cryptocellar.org (PDF; 80 kB) Accessed: February 15, 2016.
- ↑ a b c Michael Pröse: Encryption machines and deciphering devices in the Second World War - the history of technology and aspects of the history of IT . Dissertation at Chemnitz University of Technology, Leipzig 2004, p. 50
- ↑ Ralph Erskine, Frode Weierud: Naval Enigma - M4 and its Rotors. Cryptologia, 11: 4, 1987, p. 237, doi: 10.1080 / 0161-118791862063 .
- ^ A b Daniel J. Girard: Breaking “Tirpitz” - Cryptanalysis of the Japanese German Joint Naval Cipher , Cryptologia, 2016. doi: 10.1080 / 01611194.2015.1087073
- ↑ a b Anders Wik: Enigma Z30 retrieved . In: Cryptologia . Taylor & Francis, December 14, 2015, pp. 1–6 , doi : 10.1080 / 01611194.2015.1055387 .
- ^ Frode Weierud: Tirpitz and the Japanese-German naval war communication agreement . Cryptolog, Vol. 20, No. 3, Summer 1999. cryptocellar.org (PDF; 0.1 MB) Accessed: February 15, 2016.
- ^ Arturo Quirantes: Model Z, a numbers-only Enigma version . Cryptologia, Rose-Hulman Institute of Technology, Taylor & Francis, Philadelphia PA 26.2002, April 2004. ISSN 0161-1194 Retrieved Nov. 4, 2013. Enigma-Z
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 142.
- ↑ Geoff Sullivan, Frode Weierud: Breaking German Army Ciphers . Cryptologia , Vol XXIX (3), July 2005, pp. 193-232.
- ^ Lothar-Günther Buchheim : The boat . Novel. dtv, Munich 1976. ISBN 3-423-01206-4 .
- ↑ Critique of the Rhein-Zeitung . Retrieved Nov. 4, 2013.
- ↑ Chris Christensen: Review of The Imitation Game, Cryptologia, 2016. doi: 10.1080 / 01611194.2016.1236639
- ↑ Benedict Cumberbatch and Keira Knightley's Imitation Game romance labeled inaccurate . Retrieved February 9, 2015.
- ↑ Don't turn my uncle's life into a romance, says Alan Turing's niece . Retrieved February 9, 2015.
- ↑ Alex von Tunzelmann The Imitation Game: inventing a new slander to insult Alan Turing in: The Guardian , November 20, 2014. Accessed : February 9, 2015.
- ^ Robert Harris: Enigma . Novel. Weltbild, Augsburg 2005. ISBN 3-89897-119-8 .
- ^ Tony Sale: Making the Enigma ciphers for the film "Enigma" . Retrieved Nov. 4, 2013.
- ^ Polish protests against the film "Enigma" . Retrieved Nov. 4, 2013.
- ^ Polish protests against the portrayal of a "Polish traitor". Retrieved Nov. 4, 2013.
- ^ Polish contributions to the break of the Enigma. Retrieved Nov. 4, 2013.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 204. ISBN 0-947712-34-8 .
- ^ Francis Harry Hinsley, Alan Stripp: Codebreakers - The inside story of Bletchley Park . Oxford University Press, Reading, Berkshire 1993, pp. 11 ff. ISBN 0-19-280132-5 .
- ^ A b Louis Kruh, Cipher Deavours: The Commercial Enigma - Beginnings of Machine Cryptography . Cryptologia, Vol. XXVI, No. 1, January 2002, p. 11. apprendre-en-ligne.net (PDF; 0.8 MB) Retrieved on November 4, 2013.
- ↑ Craig P. Bauer: Secret History - The Story of Cryptology . CRC Press, Boca Raton 2013, p. 248. ISBN 978-1-4665-6186-1 .
- ↑ David Kahn: Seizing the Enigma - The Race to Break the German U-Boat Codes, 1939-1943 . Naval Institute Press, Annapolis, MD, USA, 2012, p. 83. ISBN 978-1-59114-807-4 .
- ^ Rudolf Kippenhahn: Encrypted messages, secret writing, Enigma and chip card . Rowohlt, Reinbek bei Hamburg 1999, p . 226. ISBN 3-499-60807-3 .
- ^ A b Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 355. ISBN 0-304-36662-5 .
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 214. ISBN 0-947712-34-8 .
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 50.
- ↑ Scan of a (then) secret letter from the OKM dated October 15, 1941 to the commander of the battleships with entry stamp dated October 23, 1941, retrieved from the Crypto Museum on December 21, 2020.
- ↑ Philip Marks : Umkehrwalze D: Enigma's rewirable reflector - Part 1 . Cryptologia , Volume XXV, Number 2, April 2001, p. 107.
- ↑ Michael Pröse: Encryption machines and deciphering devices in the Second World War - the history of technology and aspects of the history of computer science . Dissertation at Chemnitz University of Technology, Leipzig 2004, p. 40.
- ↑ a b Heinz Ulbricht: The Enigma cipher machine - deceptive security. A contribution to the history of the intelligence services. Dissertation Braunschweig 2005, p. 22.
- ↑ Michael Pröse: Encryption machines and deciphering devices in the Second World War - the history of technology and aspects of the history of computer science. Dissertation 2004, p. 143.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 220. ISBN 0-947712-34-8 .
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 16. codesandciphers.org.uk (PDF; 0.4 MB) Retrieved October 19, 2017.
- ^ A b Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 108. ISBN 0-947712-34-8 .
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 20. codesandciphers.org (PDF; 0.4 MB) Retrieved March 30, 2017.
- ↑ Geoff Sullivan, Frode Weierud: Breaking German Army Ciphers . Cryptologia, Vol XXIX (3), July 2005, pp. 212-214.
- ↑ James A. Reeds, Whitfield Diffie , JV Field: Breaking Teleprinter Ciphers at Bletchley Park: An edition of IJ Good , D. Michie and G. Timms: General Report on Tunny with Emphasis on Statistical Methods (1945). Wiley - IEEE Press, 2015, p. 396 (English). ISBN 978-0-470-46589-9 .
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 26. codesandciphers.org.uk (PDF; 0.4 MB) Retrieved March 30, 2017.
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 27. codesandciphers.org.uk (PDF; 0.4 MB) Retrieved March 30, 2017.
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 49.
- ↑ Gordon Welchman: The Hut Six Story - Breaking the Enigma Codes . Allen Lane, London 1982; Cleobury Mortimer M&M, Baldwin Shropshire 2000, p. 102. ISBN 0-947712-34-8 .
- ↑ Friedrich L. Bauer: Deciphered secrets. Methods and maxims of cryptology. 3rd, revised and expanded edition. Springer, Berlin et al. 2000, p. 426.
- ↑ David Kahn: Seizing the Enigma - The Race to Break the German U-Boat Codes, 1939-1943 . Naval Institute Press, Annapolis, MD, USA, 2012, p. 139. ISBN 978-1-59114-807-4 .
- ↑ High Command of the Wehrmacht: General key rules for the Wehrmacht . H.Dv.g. 7, Reichsdruckerei , Berlin 1944, p. 5. cdvandt.org (PDF; 0.9 MB) Accessed : Nov. 4, 2013.
- ↑ OKW: Key instructions for the Enigma key machine . H.Dv. G. 14, Reichsdruckerei , Berlin 1940, p. 7. (Copy of the original manual with a few small typing errors.) Retrieved on November 28, 2018. PDF; 0.1 MB ( memento from September 24, 2015 in the Internet Archive )
- ↑ José Ramón Soler Fuensanta, Francisco Javier López-Brea Espiau and Frode Weierud: Spanish Enigma: A History of the Enigma in Spain . Cryptologia. Rose-Hulman Institute of Technology. Taylor & Francis, Philadelphia PA 34.2010,4 (October), p. 313. ISSN 0161-1194 .
- ↑ Tony Sale: The Bletchley Park 1944 Cryptographic Dictionary . Publication, Bletchley Park, 2001, p. 45, accessed December 14, 2018. codesandciphers.org.uk (PDF; 0.4 MB)
- ^ Hugh Sebag-Montefiore: Enigma - The battle for the code . Cassell Military Paperbacks, London 2004, p. 422. ISBN 0-304-36662-5 .
- ↑ John Jackson: Solving Enigma's Secrets - The Official History of Bletchley Park's Hut 6. BookTower Publishing 2014, p. 211. ISBN 978-0-9557164-3-0 .
- ^ OKM: The key M - Procedure M General . Berlin 1940, p. 9.
- ↑ Louis Kruh, Cipher Deavours: The Commercial Enigma - Beginnings of Machine Cryptography . Cryptologia, Vol. XXVI, No. 1, January 2002, p. 11. apprendre-en-ligne.net (PDF; 0.8 MB)